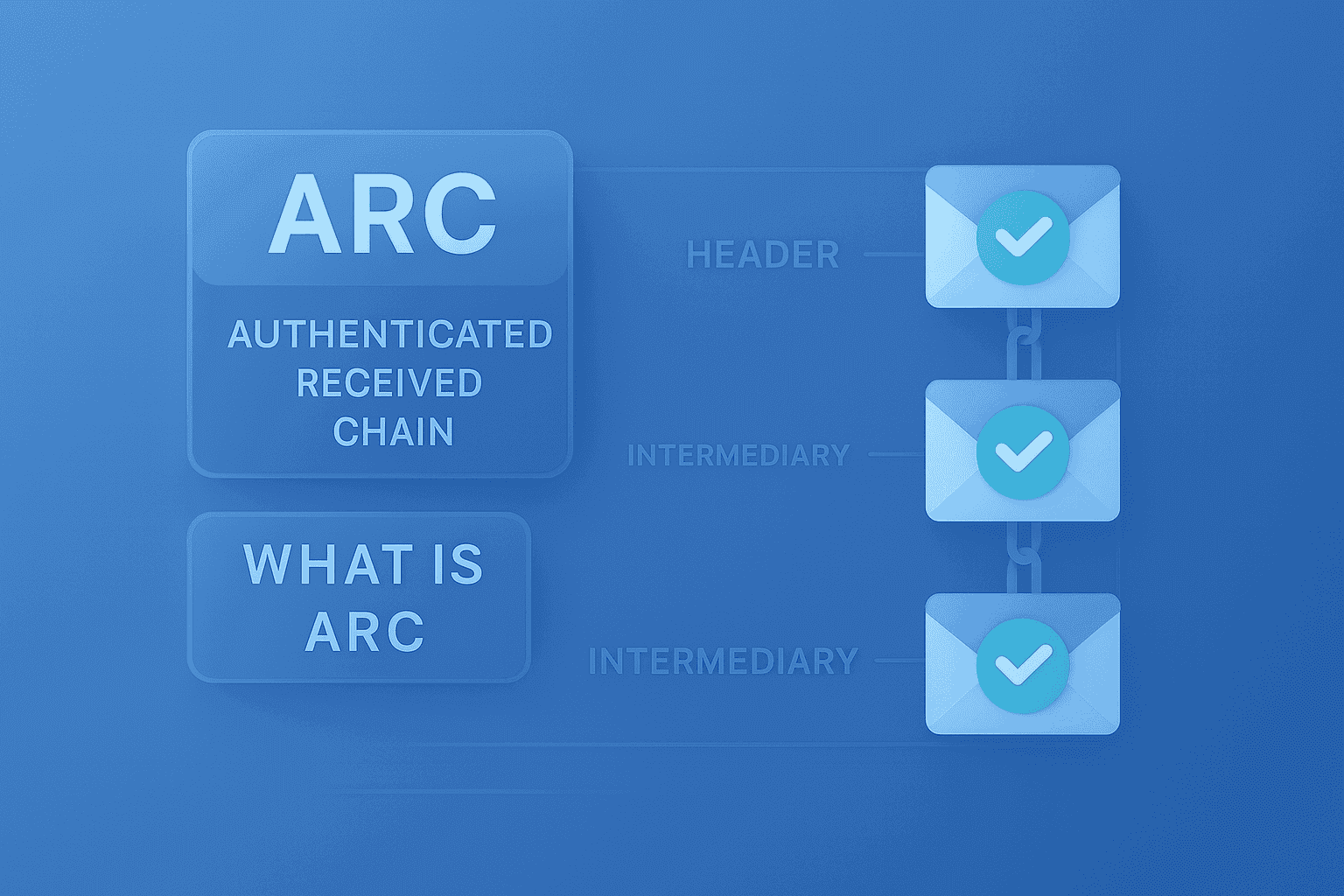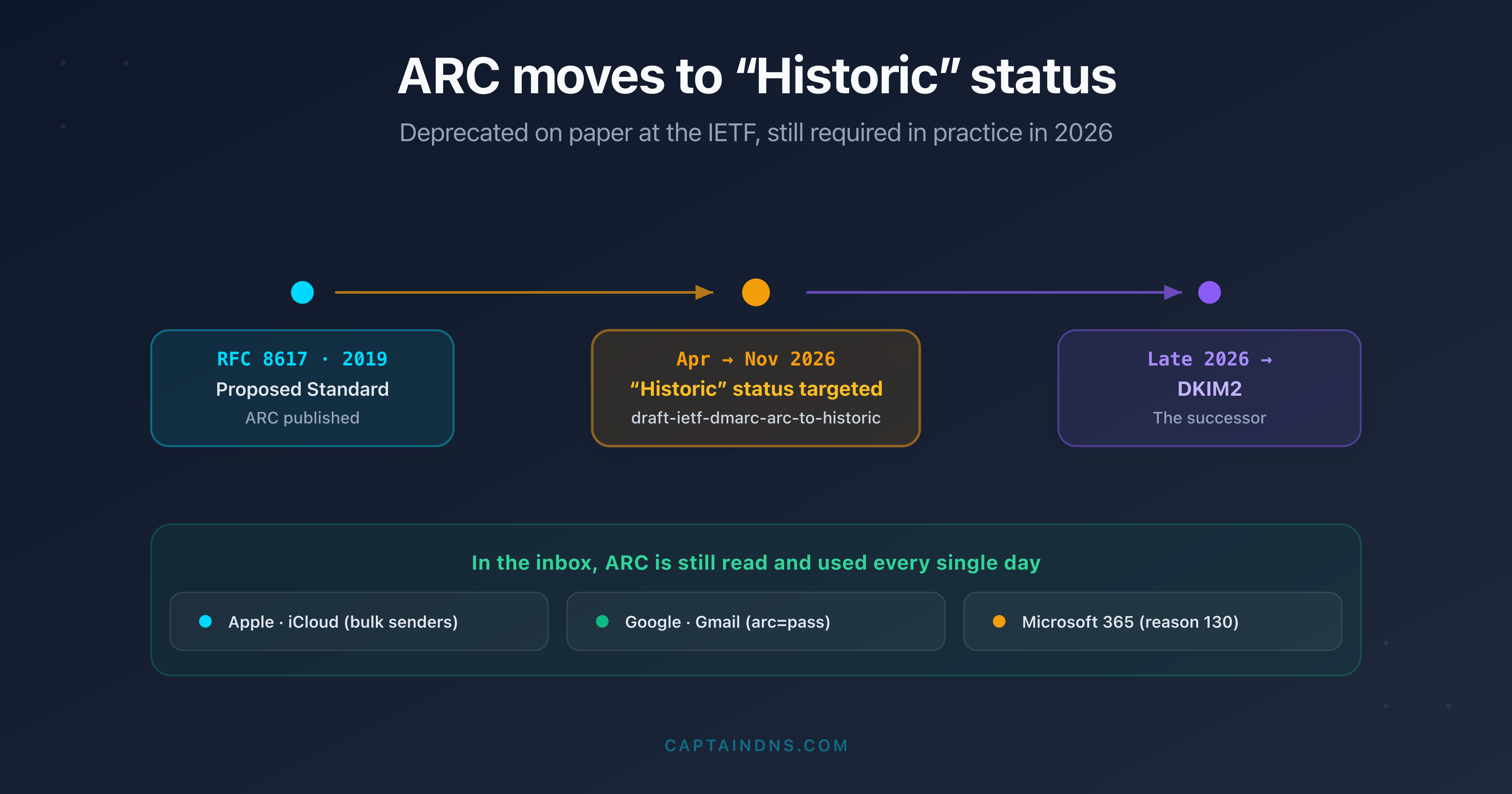
ARC moves to "Historic" status at the IETF: should you still care in 2026?
The IETF is reclassifying ARC (RFC 8617) as "Historic." But deprecated on paper does not mean dead in practice: Apple, Google and Microsoft still require it. Here is what really changes and what you should do.