Articles - Page 5
March 2026
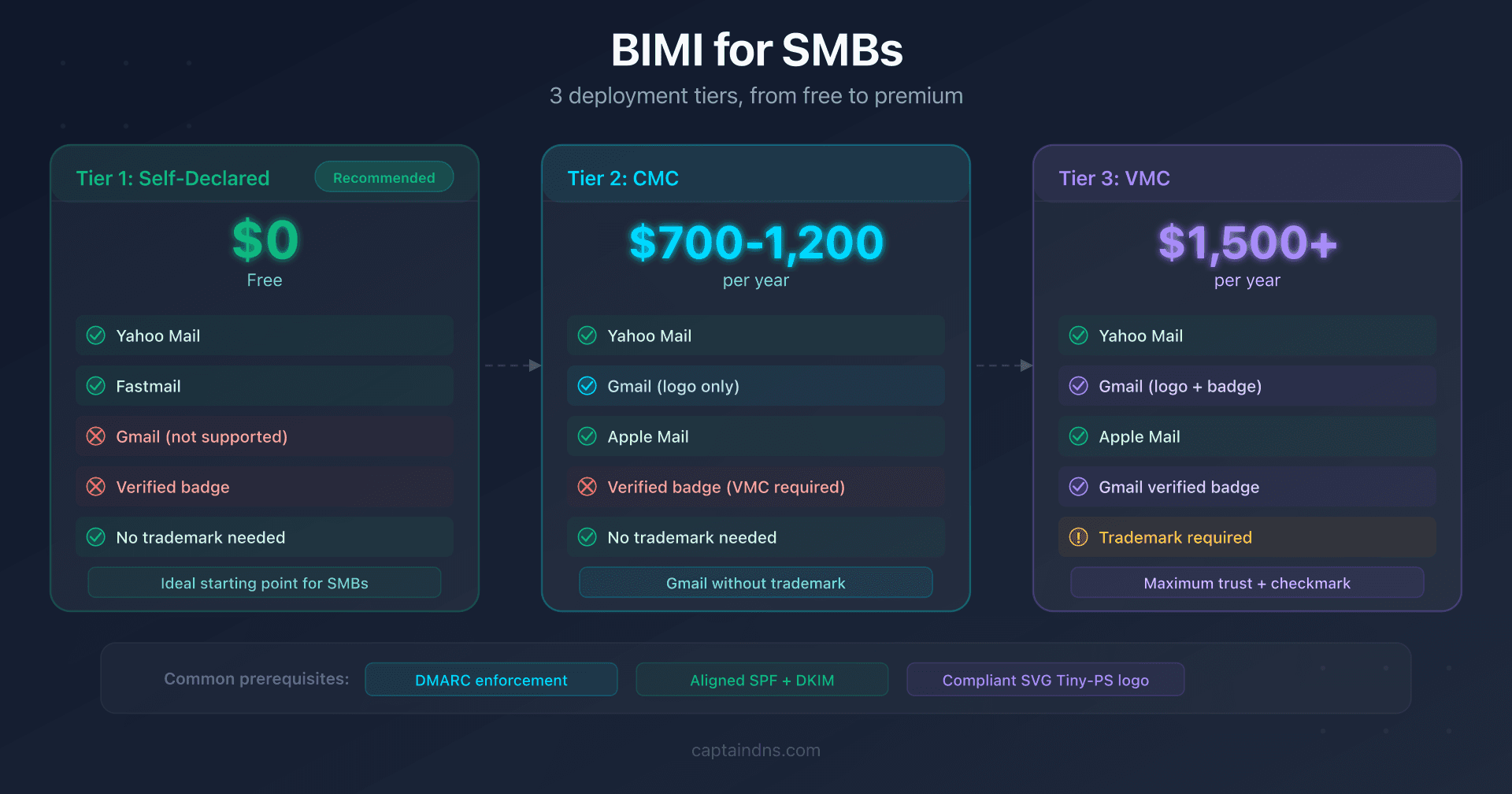
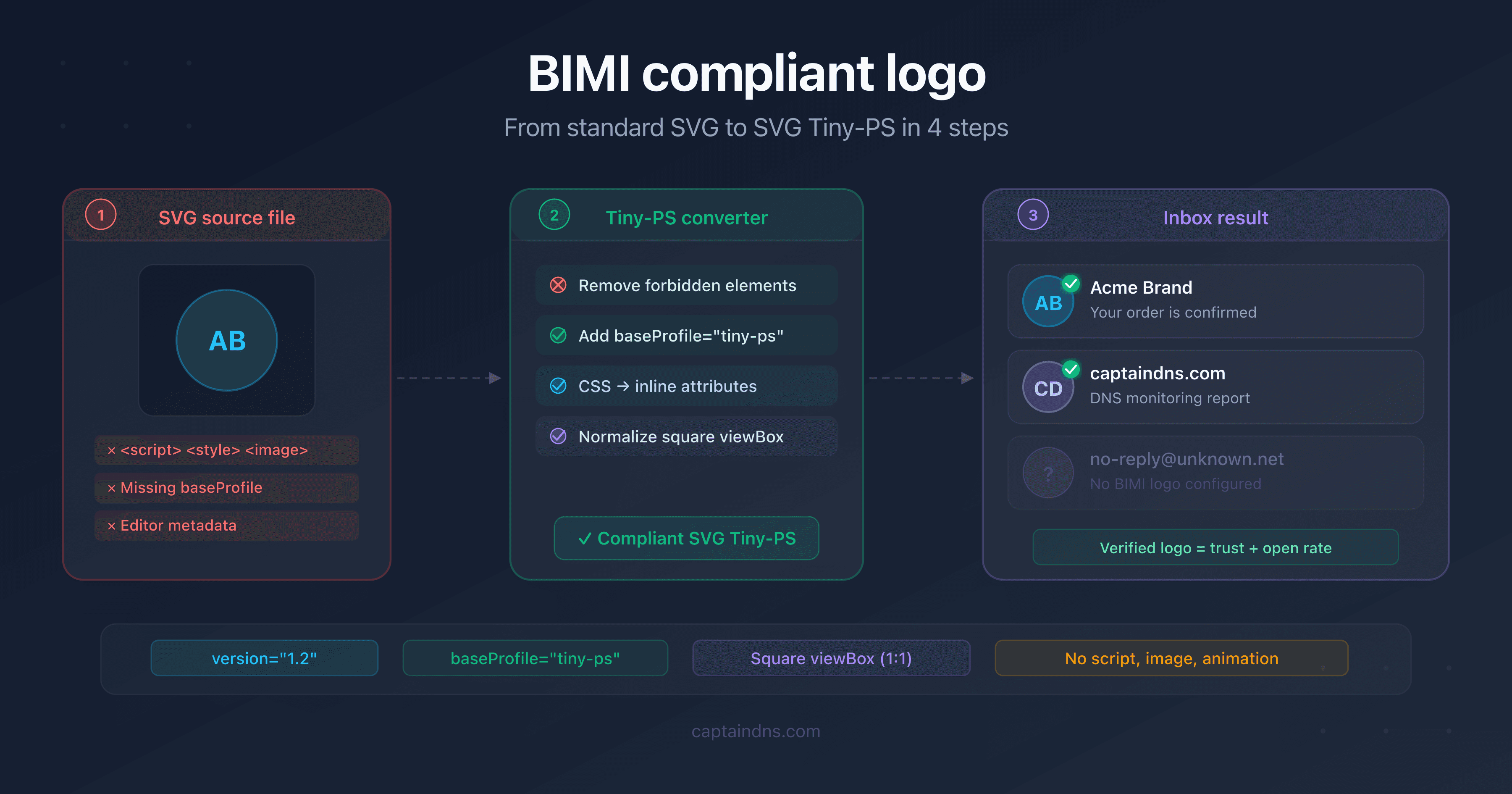
BIMI Without a VMC: The Budget-Friendly Guide to Displaying Your Logo in the Inbox
BIMI isn't just for large enterprises. This guide covers the 3 deployment tiers (free, CMC, VMC), the DNS prerequisites, and 5 steps for small and mid-sized businesses.
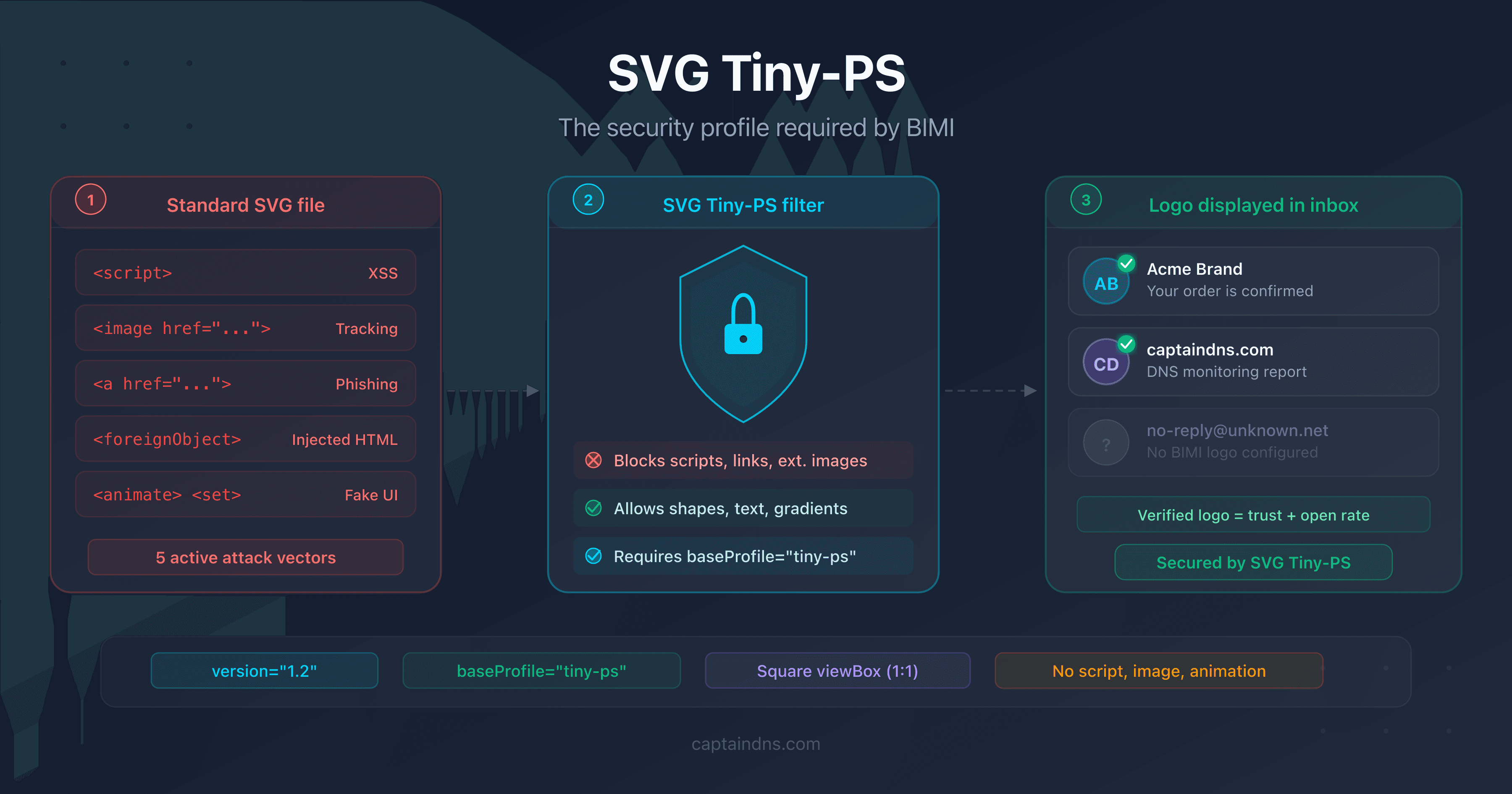
SVG Tiny-PS: understanding the security profile required by BIMI
An SVG file can contain JavaScript, phishing links and tracking pixels. Learn how the SVG Tiny-PS profile neutralizes these threats to secure BIMI logos.
February 2026
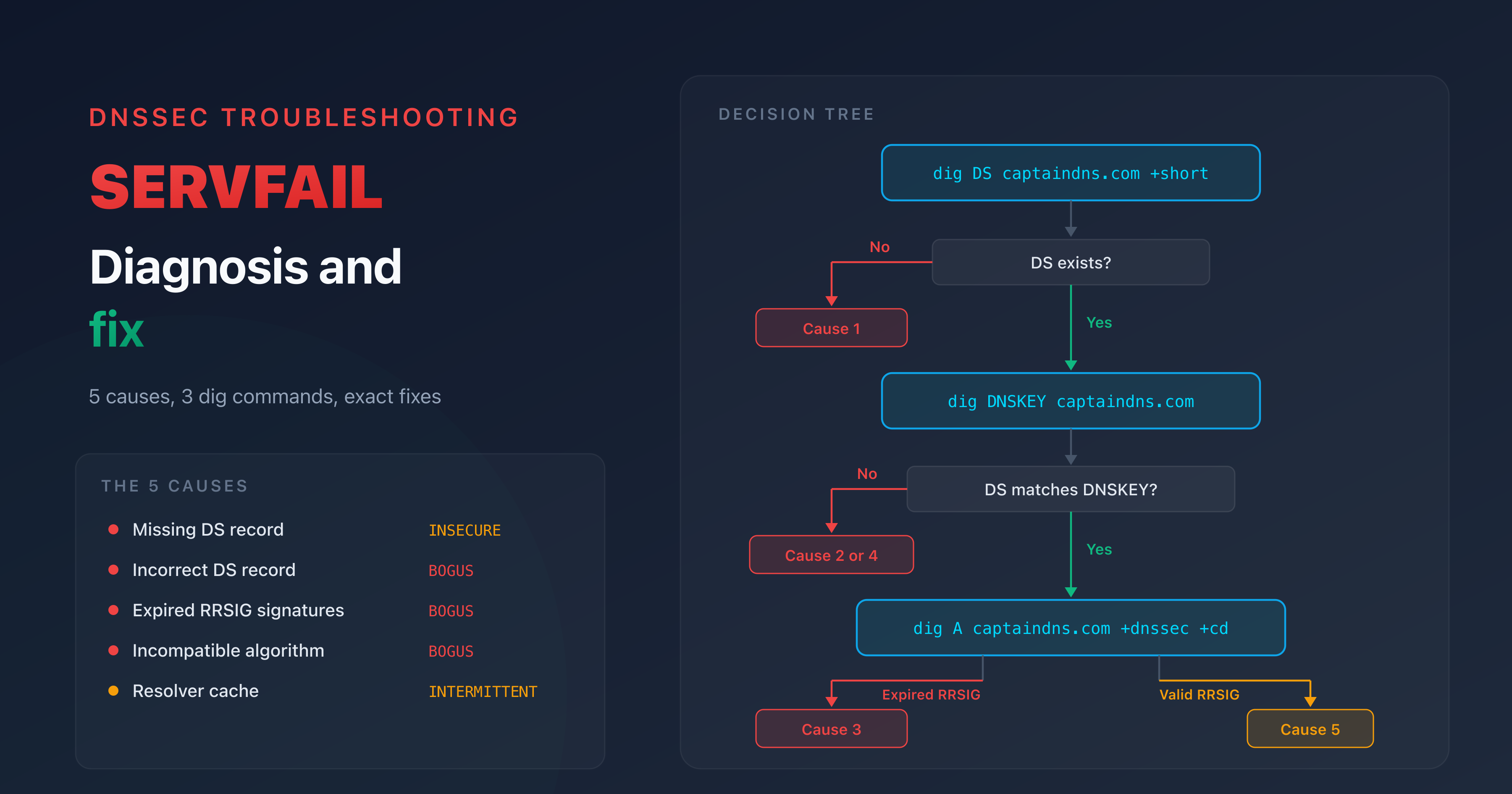
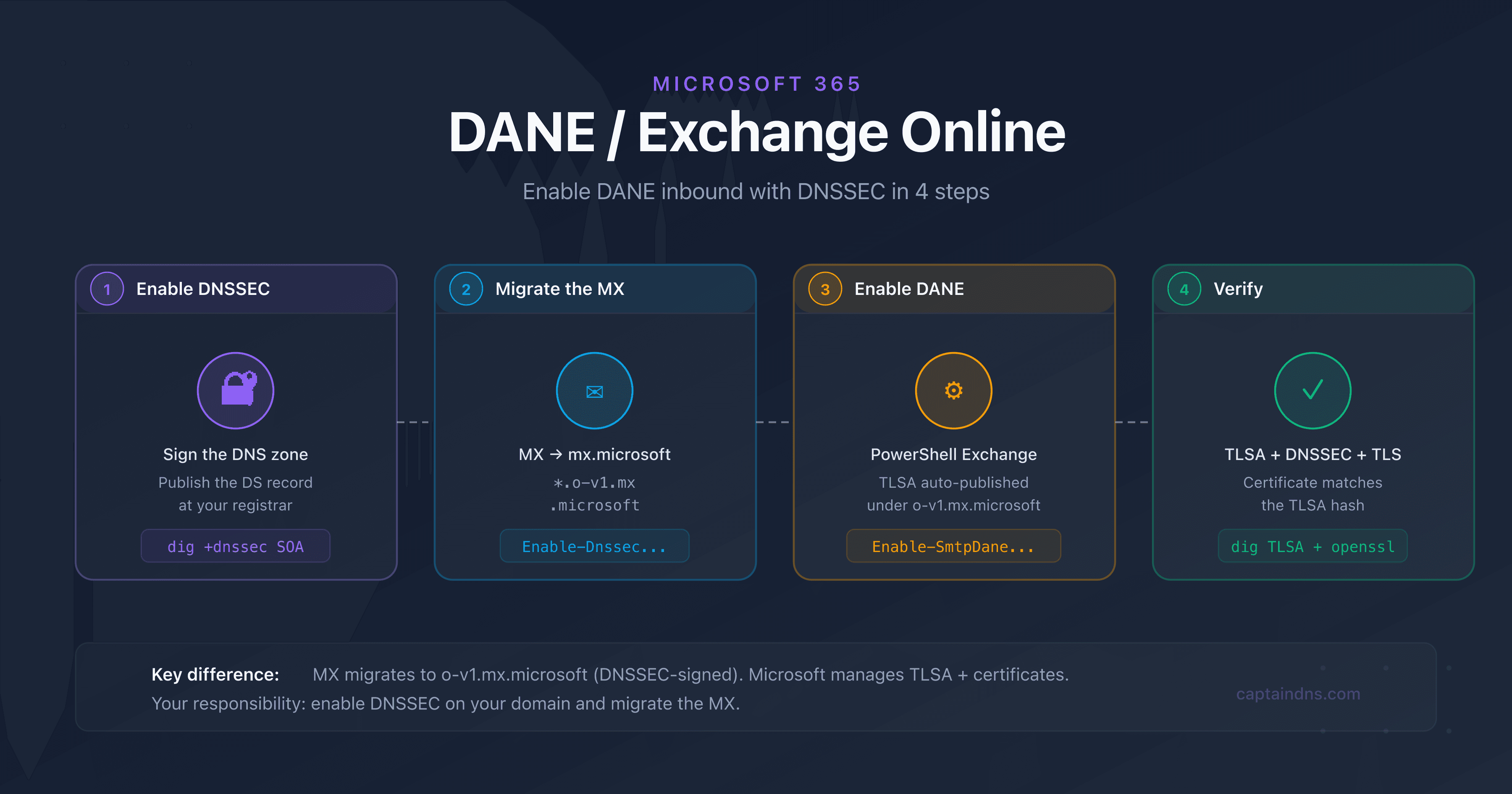
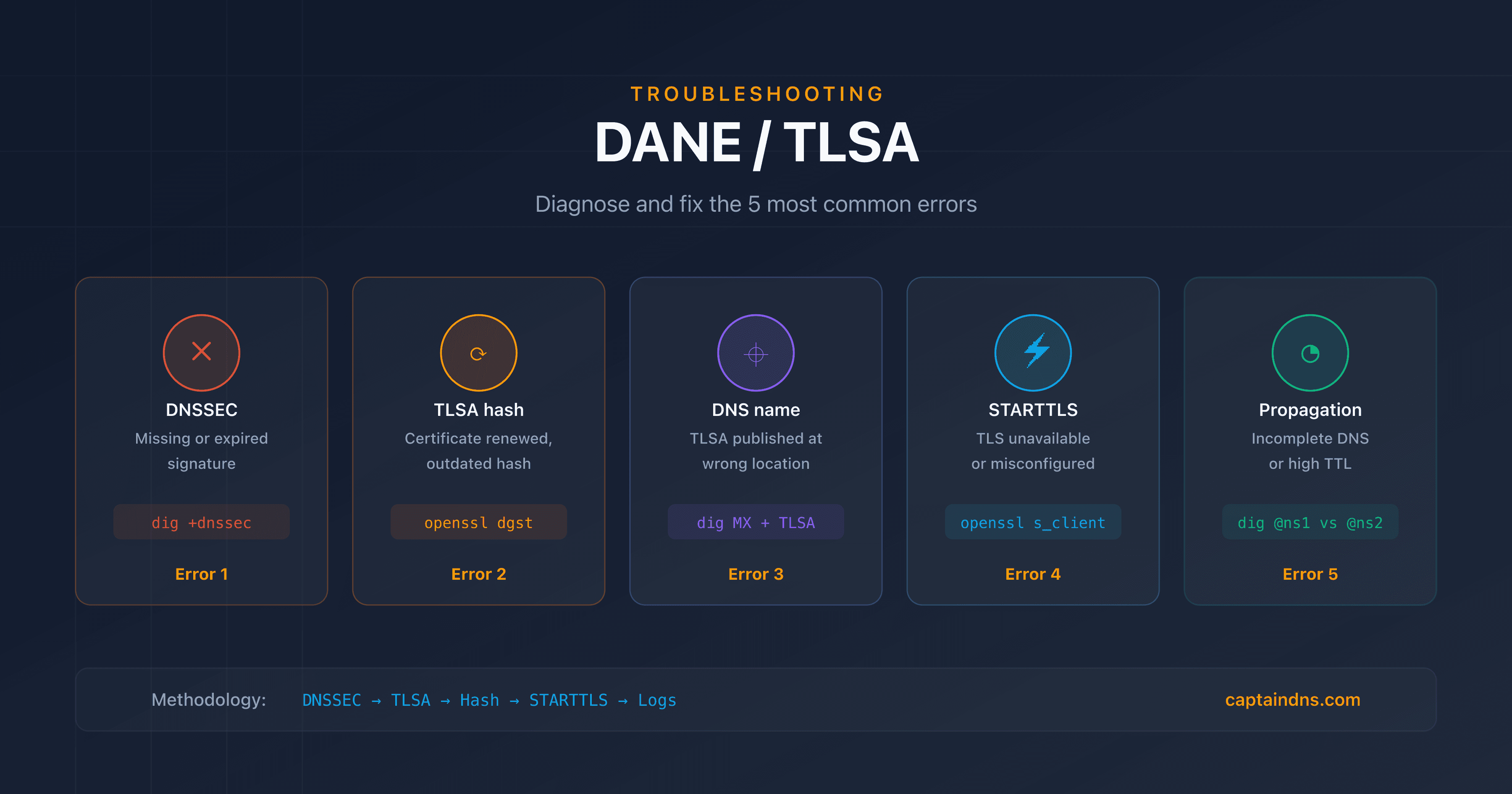
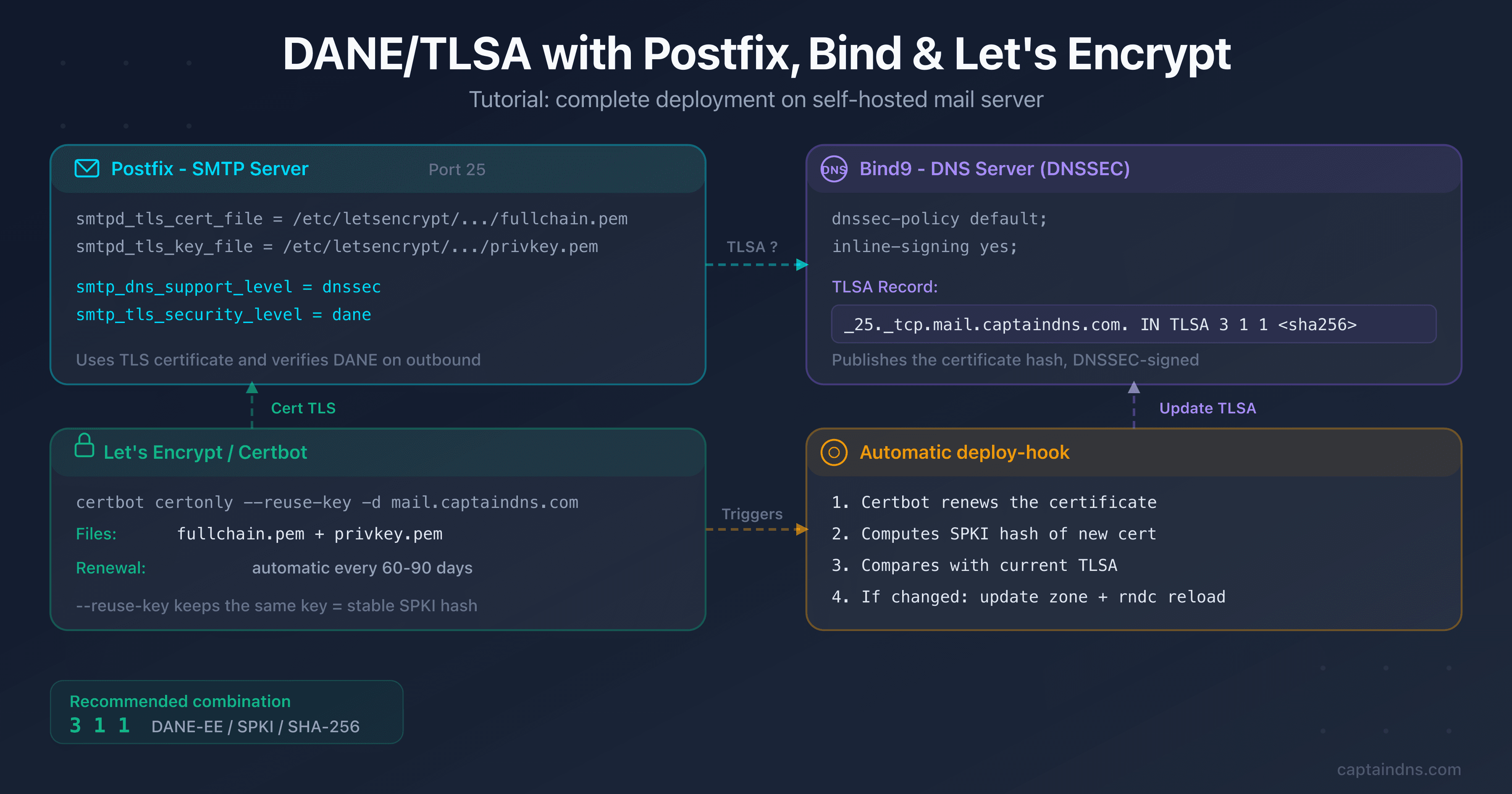
SERVFAIL after enabling DNSSEC: diagnosis and fix
A SERVFAIL after enabling DNSSEC points to a broken chain of trust. This guide covers the five causes, three diagnostic commands, and exact fixes for each scenario.
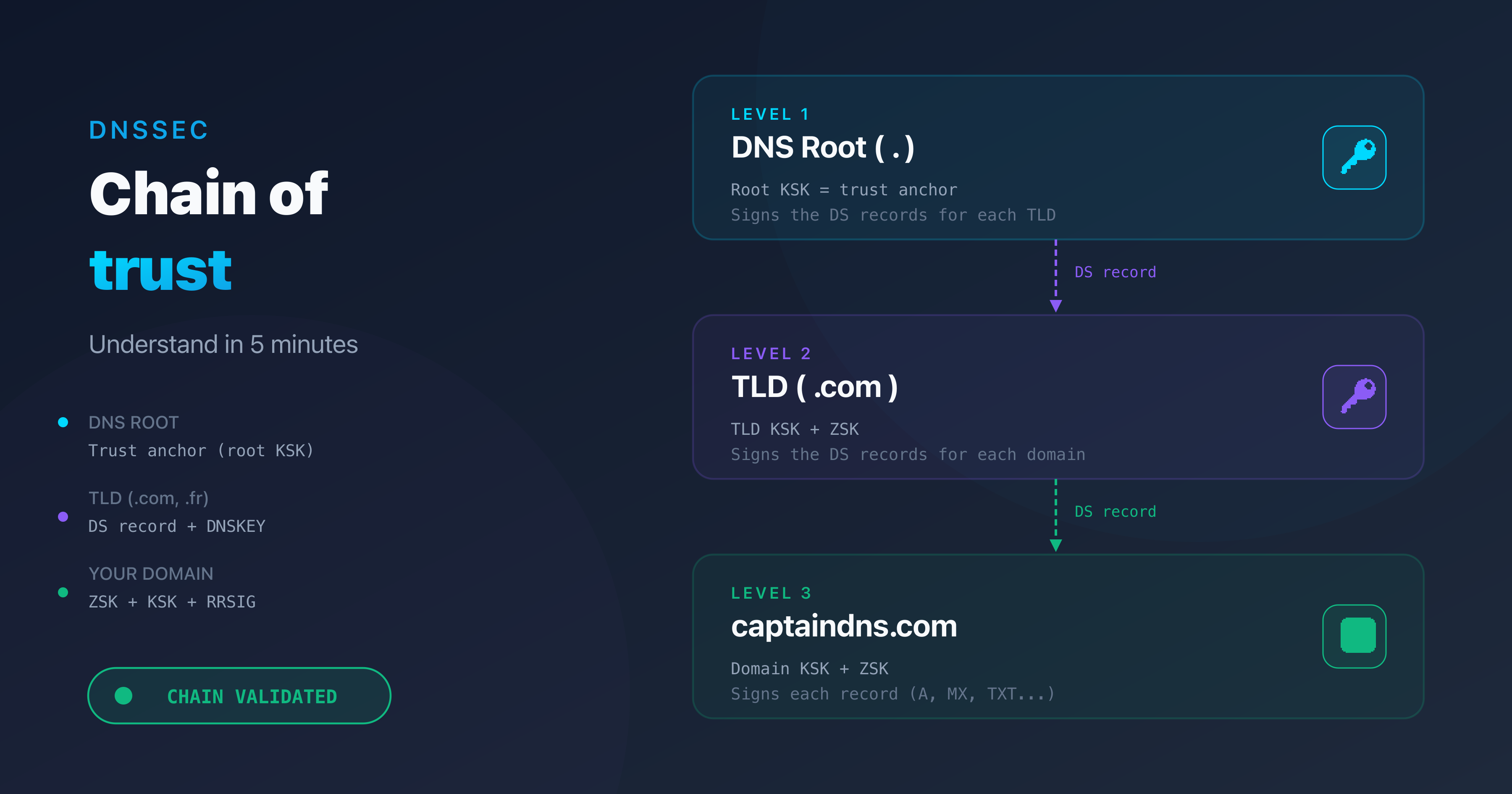
Understand the DNSSEC chain of trust in 5 minutes
The chain of trust is the core principle behind DNSSEC. This guide explains every link, from the DNS root to your domain, with clear diagrams.