Phishing vs spear phishing: what's the difference in 2026?
By CaptainDNS
Published on May 4, 2026
- Phishing targets thousands of people with a generic email; spear phishing targets a single person after OSINT reconnaissance.
- In 2024, the FBI tallied BEC losses (the costliest form of spear) at $2.77 billion across 21,442 incidents.
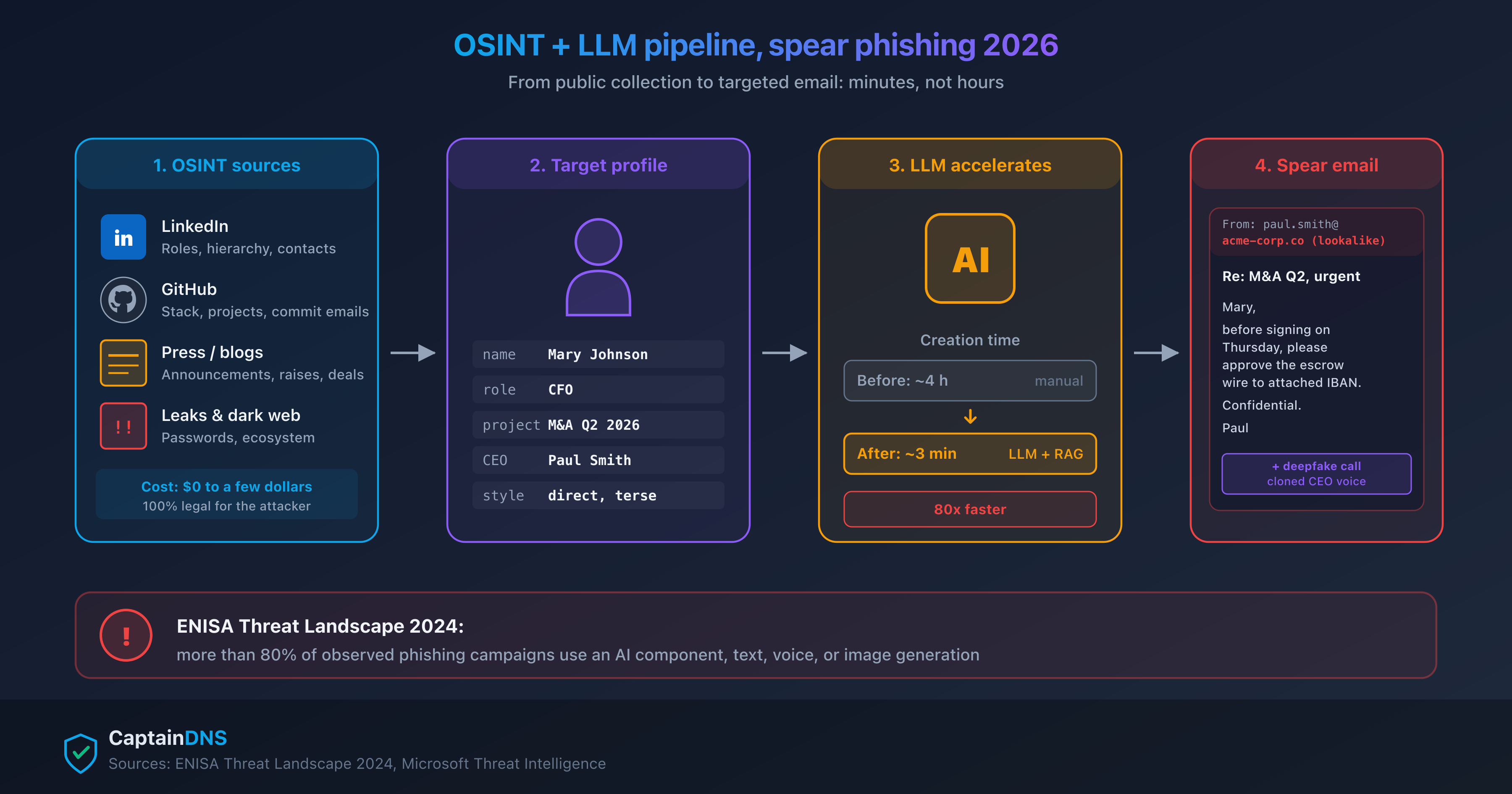
- Generative AI and LLMs cut the cost of a spear campaign from several hours to a few minutes: ENISA finds that more than 80% of phishing campaigns now use AI.
- The 2024 deepfake attack on Arup cost $25 million through a video call featuring a fake CFO and cloned colleagues.
- DMARC at reject policy, BIMI, and continuous training remain the most cost-effective defenses: Verizon DBIR 2025 measures a 4x improvement in reporting after training.
In 2024, the FBI Internet Crime Complaint Center recorded 859,532 cybercrime complaints and $16.6 billion in losses, up 33% from 2023. A significant share of those cases starts with a fraudulent email. Yet security leaders use phishing, spear phishing, BEC, and whaling interchangeably, even though the stakes and the defenses are not the same.
The confusion has a direct operational cost. A budget allocated to a standard antispam filter doesn't protect a finance team against a credible wire transfer request. Training focused on spelling mistakes doesn't prepare anyone for a DKIM-signed, flawless, personalized email. And a leadership team thinking "phishing" when it should be thinking "spear" underestimates the real risk.
This article separates the concepts, draws on the 2024-2025 reports (Verizon DBIR, IBM, ENISA, Microsoft, APWG), and illustrates with concrete cases like Arup or Change Healthcare. It targets security decision-makers in mid-market companies and IT teams that need to prioritize their email defense investments against the new wave of AI-assisted attacks.
Phishing vs spear phishing: the difference in one sentence
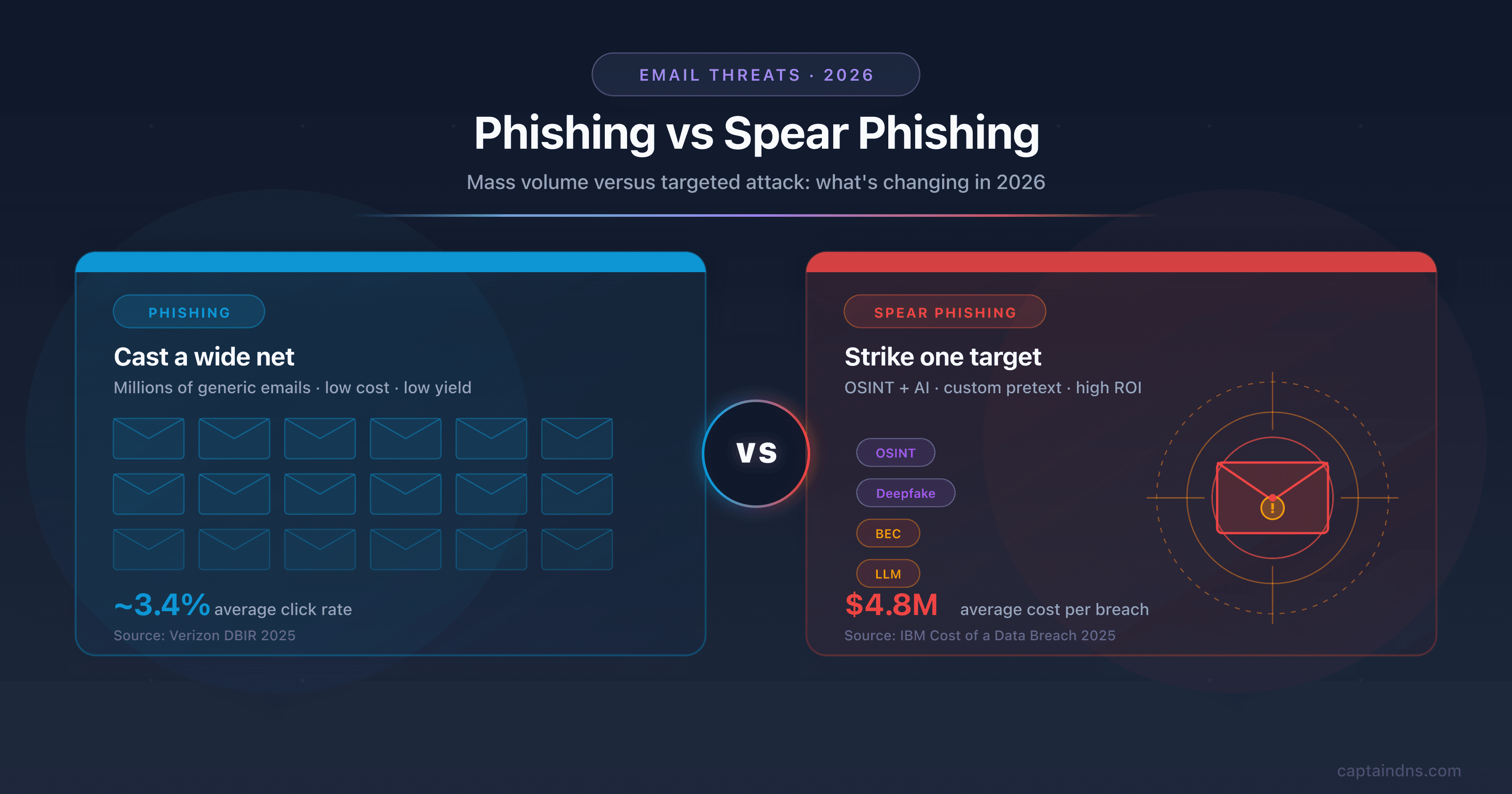
Phishing is a mass attack, sent to thousands of targets with a generic message. Spear phishing is a targeted attack: the attacker performs OSINT research on a specific victim, personalizes the email with their professional context, and exploits trust to gain access, a wire transfer, or data. Phishing bets on volume, spear on precision.
This distinction shapes everything else: attacker resources, useful defenses, cost to the victim, forensic traces. A finance team that thinks "phishing" while actually facing spear phishing invests in the wrong controls: it strengthens antispam filters instead of hardening wire transfer procedures. The following sections detail each dimension to support an accurate diagnosis and defensive investments aligned with reality.
Side-by-side anatomy of the two attacks
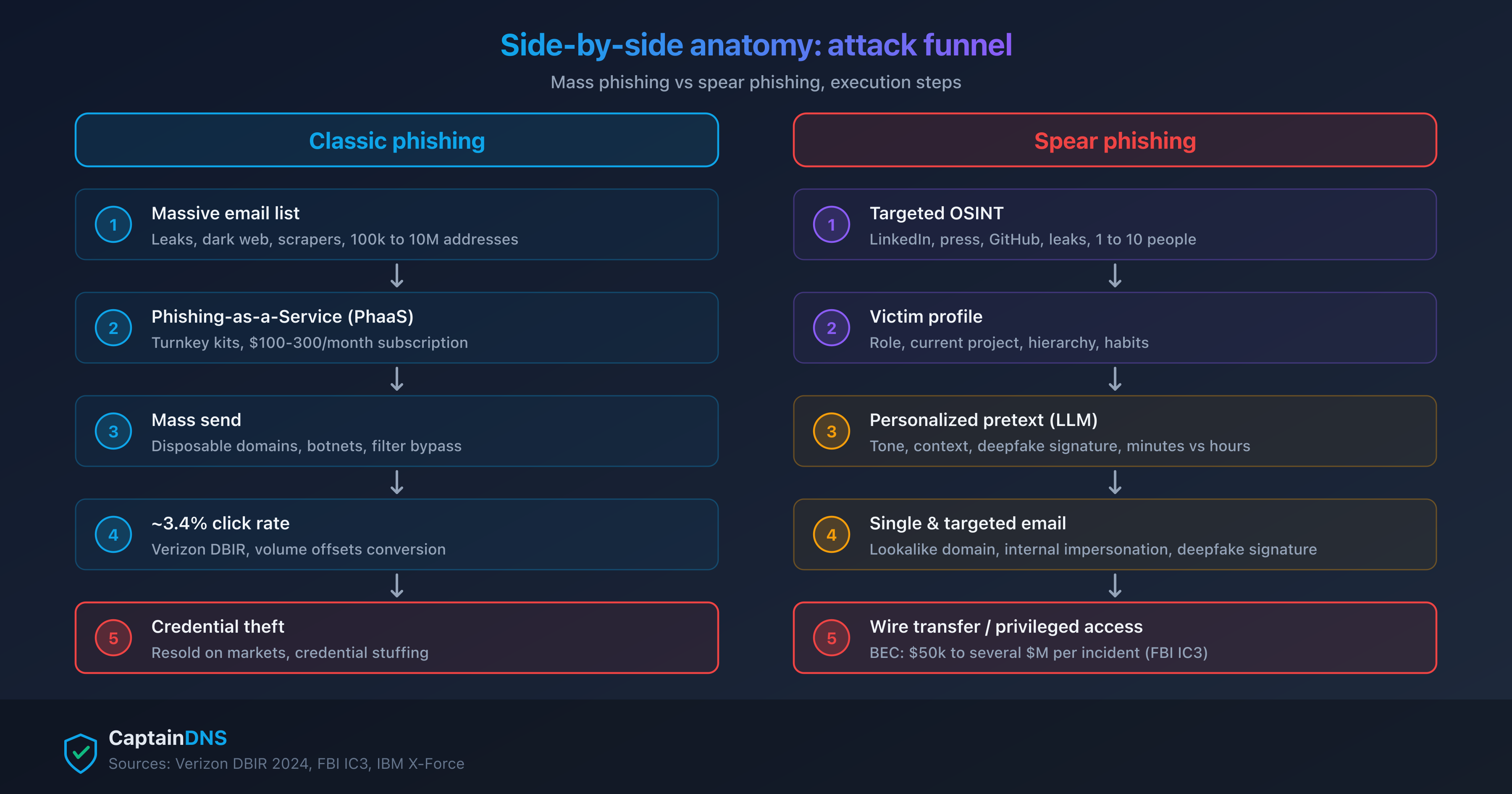
Classic phishing: volume and opportunism
Classic phishing works like a hijacked marketing campaign. The attacker rents or buys email lists, deploys a phishing-as-a-service kit with a clone site, and uses disposable infrastructure (newly registered domains, redirects through URL shorteners, ephemeral hosting). The message is generic: "Dear customer," "Your account will be locked," "Confirm your delivery." No prior knowledge of the target is needed.
The economic model relies on conversion at a very low rate. The attacker doesn't need 100% of recipients to click: 0.1% is enough to make a 100,000-message campaign profitable. That's why classic phishing tolerates poorly tuned messages and crude clone sites. The logic stays the same as direct marketing, transposed to fraud.
The numbers confirm the scale. The APWG counted 1,003,924 attacks in Q1 2025, more than one million in three months. The SaaS and webmail sector remains the #1 target with 23.3% of attacks in Q4 2024. Verizon DBIR 2025 measures a median click time of 21 seconds after opening, and a full compromise (credential entry on the fake site) of 49 seconds. In other words, between opening the email and compromise, the user has less than a minute, which makes any deliberate analysis unlikely. On effectiveness, Proofpoint's State of the Phish (2024 edition, the most recent, with the annual format discontinued since) puts the average click rate at 3.4% across observed campaigns.
URL shorteners play a key role in this industry: they hide the real destination URL, bypass certain blocklists, and allow quick pivots to new infrastructure when the previous one is taken down. See URL shorteners and security risks for the technical details.
Spear phishing: reconnaissance and precision
Spear phishing flips the logic. The attacker identifies a named target, gathers open-source intelligence (OSINT) from LinkedIn, the corporate site, press releases, GitHub, and database leaks. From this, they craft a credible pretext: a known supplier requesting payment, an executive on a trip asking for an urgent transfer, a legal partner forwarding a file. The email is technically often flawless: aligned SPF, DKIM, and DMARC, personalized content, internal jargon.
Timing also changes. A spear campaign can stretch over several weeks of preparation, several days of preliminary contact ("warm-up"), and a single final payload email. The attacker may send an initial benign message to confirm the target address is active, learn the victim's reply style, and identify when they check their inbox. This phase is invisible to detection tools because nothing is malicious yet.
Proofpoint observes around 66 million Business Email Compromise attempts per month in 2024. IBM measures an average cost of $4.8 million per phishing-initiated breach in its Cost of a Data Breach 2025 report. The granularity changes: from a campaign of millions of emails to a few highly precise messages that pass antispam filters because, on paper, they're legitimate. The cost to the victim scales accordingly: a single fraudulent transfer can amount to several hundred thousand dollars, while a password stolen via classic phishing resells for a few dollars on underground forums.
To understand how this kind of email passes filters, see Email routing and Microsoft's spoofing alert.
| Criterion | Classic phishing | Spear phishing |
|---|---|---|
| Target | Generic list (10k-1M emails) | Named individual or small group |
| Volume per campaign | High (thousands to millions sent) | Low (1 to 50 emails) |
| Personalization | None or minimal ("Dear customer") | Strong: name, role, current project, internal jargon |
| Prior reconnaissance | None | Systematic OSINT (LinkedIn, corporate site, releases) |
| Typical pretext | Bank, delivery, "account locked" | Known supplier, executive, HR, legal |
| Monetization vector | Credential theft, generic malware | Fraudulent wire transfer, privileged access, targeted ransomware |
| Average cost to victim | $70M cumulative 2024 across all complaints (FBI IC3) | $4.8M per breach (IBM); ~$129k median per BEC incident (FBI) |
| Automatic detection | Antispam filters effective (3.4% click rate) | Filters often ineffective (technically legitimate email) |
Three criteria from the table deserve operational comment. The cost to the victim confirms the asymmetry: the cumulative total of phishing/spoofing complaints at the FBI IC3 in 2024 is lower than the loss from a single large BEC operation. This doesn't mean classic phishing is negligible (frequency stays massive), but at equal defensive budget, prioritizing spear defense yields a higher return on investment in monetary terms avoided. Automatic detection illustrates the limits of filters: statistical effectiveness on volume hides near-zero real effectiveness on targeted attacks. Prior reconnaissance, finally, explains why CISOs must include OSINT monitoring of their own organization: what an attacker can find in 30 minutes on LinkedIn and the corporate site directly sizes the exploitable spear surface.
The decisive role of OSINT in 2026
OSINT (Open Source Intelligence) is the building block that separates phishing from spear phishing. Before 2023, a competent attacker spent several hours manually compiling a dossier on the target: org chart reconstructed via LinkedIn, current projects via press releases, technologies via job postings, email addresses via public leaks, internal jargon via YouTube videos and corporate podcasts. The cost of a spear campaign was dominated by this reconnaissance phase.
Generative AI upends that economics. LLMs ingest OSINT data, generate a personalized email in the executive's writing style, translate into any target language, and produce the variations needed for A/B testing. The ENISA Threat Landscape 2024 report finds that more than 80% of observed phishing campaigns now use some form of AI. The "poorly written email = phishing" filter is obsolete.
Concretely, the typical attack pipeline combines four building blocks. First, automated collection via LinkedIn scrapers and OSINT engines like theHarvester or SpiderFoot. Then aggregation of the data into a target file: full name, role, direct manager, active projects, supplier partners cited publicly. Then payload generation by an LLM, which drafts several email variants imitating the corporate tone identified in official releases. Finally, sending from credible infrastructure (compromised supplier account or cousin domain registered a few days earlier).
Concrete examples are multiplying. Anthropic documented in August 2025 the case of a solo cybercriminal who extorted 17 organizations using Claude Code to automate OSINT collection, drafting extortion messages, and negotiation, with ransoms reaching over $500,000 per victim. OpenAI announced in October 2025 that it had disrupted more than 40 malicious networks since February 2024. Microsoft Digital Defense Report 2024 measures a 146% rise in Adversary-in-the-Middle attacks, around 39,000 AiTM incidents per day.
The net effect for defenders is threefold. First effect: the cost of producing a quality spear campaign drops from several thousand dollars (equivalent to weeks of work for an experienced operator) to a few dozen dollars in LLM tokens. Second effect: the attacker profile changes. Nation-state actors are no longer the only ones running polished targeted campaigns; an opportunistic cybercriminal with a moderate budget can now target a specific SMB. Third effect: the volume of targeted campaigns rises, which makes pre-2024 threat modeling assumptions obsolete.
Whaling and other adjacent terms
Four terms circulate in the press and in reports, with overlaps that breed confusion. The table below sets the definitions for the rest of the article.
| Term | Target | Mechanics | 2026 specificity |
|---|---|---|---|
| Spear phishing | Individual (any level) | Targeted email after OSINT | Parent category |
| Whaling | Senior executive (C-level) | Spear phishing aimed at CEO/CFO/CTO | High stakes, formal communication imitated |
| BEC (Business Email Compromise) | Finance or operations team | Executive or supplier impersonation for transfer | $2.77B in losses 2024 (FBI), 21,442 incidents |
| CEO fraud | Finance or accounting executive | Subcategory of BEC: urgent transfer order from the CEO | Often reinforced by audio/video deepfake in 2024-2026 |
Arup case: $25 million CFO deepfake
In January-February 2024, the British engineering firm Arup lost about HK$200 million, or $25 million in U.S. dollars, in an attack publicly disclosed by CNN in May 2024. An employee at the Hong Kong office, initially suspicious after receiving an email requesting a transfer, was convinced during a video call featuring the London-based CFO and several colleagues. All were synthetic video and audio deepfakes. The employee executed 15 transfers to 5 Hong Kong bank accounts. It's the first public case at $25 million or more involving a multi-person deepfake video call.
U.S. healthcare giant case: escalation after credential theft
On February 12, 2024, attackers accessed Change Healthcare's Citrix portal via stolen credentials, with no MFA enabled. The initial vector is a credential theft whose phishing origin has not been publicly confirmed, but the incident illustrates the escalation when an attack succeeds. ALPHV/BlackCat deployed ransomware, collected a $22 million ransom, and a second team then extorted again via a re-leak. UnitedHealth Group reported by mid-2025 more than $2.8 billion in cumulative costs. The U.S. Department of Health and Human Services (HHS) notified in July 2025 that 192.7 million people were affected by the data breach.
The two cases illustrate different dimensions of the same problem. Arup shows the effectiveness of a deepfake combined with a well-crafted pretext: despite initial suspicion indicators (the employee had sniffed out a dubious email), the staging quality reversed their judgment. The Change Healthcare case shows the domino effect: a single initial access without MFA cascades into production encryption, massive data leak, ransom payment, and long-term costs vastly higher than the defensive investments required to prevent the incident.
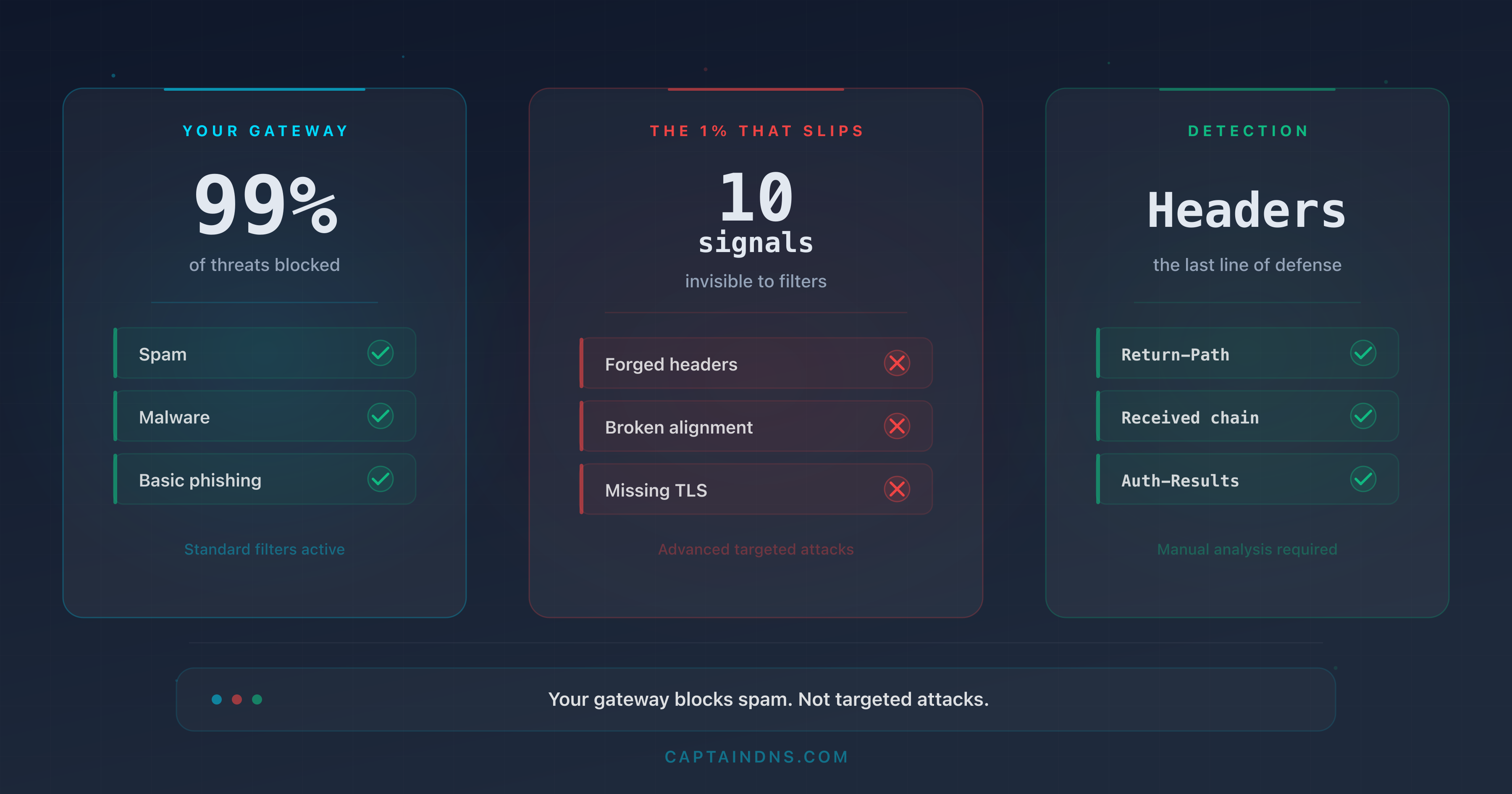
Why your classic anti-phishing defenses let spear through
Antispam and antiphishing filters rely on signals that work against volume and far less against precision. Five reasons explain why a well-built spear gets past these layers.
First, the email can be technically legitimate. When the attacker has compromised the account of a real supplier, the message respects SPF, DKIM, and DMARC on an authentic domain. No authentication signal triggers. The antispam filter then has nothing to differentiate this fraudulent email from a normal email from the same supplier received the previous week.
Second, AI killed the "poorly written content" signal. Spelling errors, awkward turns of phrase, and odd Unicode characters were weak but usable indicators. They've disappeared. Worse: LLMs can now imitate an executive's style from a few public examples (interview, LinkedIn post, newsletter editorial), which makes peer behavioral detection equally hard.
Third, volume stays under heuristic radar. A campaign of 5 emails over 30 days triggers no cluster on reputation servers, unlike a mass campaign. Threat intelligence tools work on correlation: with no possible correlation, they're blind. It's a structural blind spot, not a configuration flaw.
Fourth, the pretexts exploit known routines. An HR email to sign an amendment, a legal note forwarding an NDA, a supplier's bank account update request in the routine accounting flow: these flows are daily and already accepted. The attacker doesn't ask for an exceptional action; they ask for a usual action, in the usual time window, with the usual tone.
Fifth, structural indicators are missing. Verizon DBIR 2025 confirms that email remains a vector in 27% of breaches, that phishing accounts for 57% of social engineering tactics, and 16% of initial vectors. In the EMEA region, phishing accounts for 19% of breaches. These figures mean that even with the most modern defenses (EDR filters, attachment sandboxing, rewritten URL scanning), phishing remains one of the three most frequent initial vectors. To go deeper on header signals, see Email filter bypass and red flags in headers.
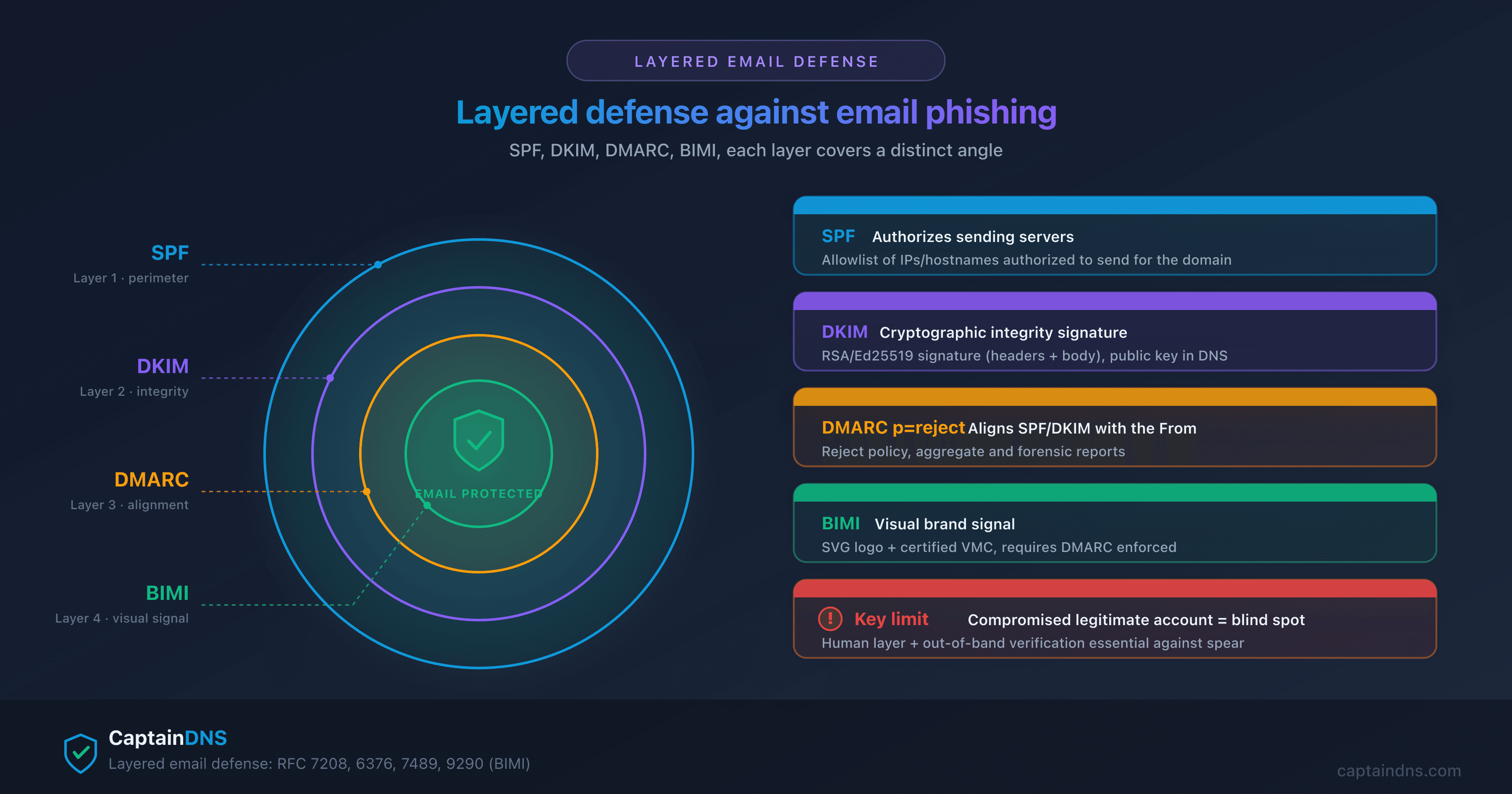
Layered defense: DMARC, SPF, DKIM, BIMI
No single layer is enough against spear phishing. Effective defense combines three families of controls: email authentication, access control, and training.
Email authentication forms the foundation. SPF declares the servers authorized to send for a domain. DKIM cryptographically signs outgoing messages. DMARC aligns both and gives the recipient a policy to apply on failure. The p=reject policy is the operational threshold: it blocks any direct impersonation of the legitimate domain. It doesn't stop attacks from a compromised internal account, nor impersonation by a cousin domain (for example, captaindns-finance.com instead of captaindns.com). For a forward-looking view, see DMARCbis: what's changing in the new RFC.
DMARC deployment proceeds in stages. The first step is to publish a p=none policy that simply collects aggregate reports (RUA) without impacting deliverability. The second step validates that legitimate sources (professional mailing, invoices, newsletters, SaaS apps) are aligned and pass SPF/DKIM. The third step moves to p=quarantine, which routes unaligned messages to spam. The fourth and final step moves to p=reject, which definitively rejects them. Jumping directly to p=reject without the monitoring phase exposes the company to losing legitimate emails.
BIMI adds a post-DMARC visual signal: the verified sender logo displays in the inbox, helping users distinguish a legitimate message from a cousin domain. This control only works if DMARC is already in p=quarantine or p=reject. BIMI also requires a VMC or CMC certificate issued by a recognized certification authority, which adds an annual cost but provides particularly effective visual identity proof against cousin domains.
On access control, FIDO2 keys neutralize AiTM attacks by binding authentication to the domain. A FIDO2 key refuses to sign an authentication assertion for a domain that doesn't match the one registered at enrollment, which makes proxies like EvilGinx2 or Modlishka ineffective. On detection, IBM Cost of a Data Breach 2025 measures that defensive AI cuts identification and containment time by 80 days on average, around $1.9 million in savings per breach. The global average remains 241 days to identify and contain a compromise, which leaves attackers plenty of room to exfiltrate or encrypt.
Training remains the most cost-effective investment. Verizon DBIR 2025 measures a 4x improvement in reporting rate after a serious training campaign. Effective training includes regular simulations (ideally monthly), varied scenarios (BEC, deepfake, AiTM, quishing), and individual pedagogical feedback rather than punitive feedback. On the analysis framework side, the techniques map to MITRE ATT&CK: T1566.001 (attachment), T1566.002 (link), and T1566.003 (third-party service).
Check your DMARC configuration: use the CaptainDNS DMARC checker to analyze your policy, your reports, and SPF/DKIM alignment in seconds.
Playbook: what to do if a spear phishing email reaches the inbox
When a suspicious email lands in a sensitive inbox (finance, executive, IT), the quality of the response in the first 30 minutes determines the outcome. Five steps structure a minimal, repeatable playbook to integrate into internal documentation and training sessions.
- Don't click or reply. Capture the email with its full headers (in most clients: "Show original" or "View source"). Headers contain the authentication signals (SPF, DKIM, DMARC) and the real SMTP path. Don't forward the email in the clear without precautions either, because some clients rewrite headers at forward time and lose DKIM signatures.
- Check the sending domain. Read the
Return-PathandFromin the headers, not the displayed name. Compare with known legitimate domains for the contact. Check SPF/DKIM/DMARC alignment in theAuthentication-Resultsheaders. Watch for homoglyphs (visually similar Unicode characters) that can turnpaypal.cominto a cousin domain imperceptible to the naked eye. - Check URLs. Any URL in the email must be passed through a multi-source checker before any click. The check should query several independent threat intelligence databases to reduce false negatives: a recent or rarely reported domain may be missing from one database but present in another.
- Confirm out of band any financial or sensitive request. Call the contact at a number already known (internal directory, business card), not the number provided in the email. For wire transfer requests, double validation by a second responsible party. The internal rule must be absolute: no exception possible "for urgency," because that's precisely the lever the attacker exploits.
- Report to the security team. Use the "Phishing report" button in the mail client if available, or forward as an attachment (
.eml) to the SOC address. Don't delete the email before processing. The SOC can search for other instances in the organization's inboxes, identify recipients who clicked, and apply a coordinated response.
Before clicking a suspicious link: run the URL through the phishing URL checker which queries Google Safe Browsing, URLhaus, PhishTank, and VirusTotal in a single request.
If the click has already happened, the response procedure changes; a dedicated guide is referenced at the end of the article in the "Further reading" section.
For organizations with more than 50 employees, this playbook must be formally documented, tested twice a year with a full-scale exercise, and accompanied by an escalation procedure that includes the legal department and the data protection officer (DPO) in case of confirmed breach. For smaller structures, a 2-page written procedure handed to each employee covers the essentials.
FAQ
What's the difference between phishing and spear phishing?
Phishing sends a generic message to thousands of targets; spear phishing targets a specific person after OSINT research. The difference shows up in personalization, volume, and cost to the victim. BEC, a subcategory of spear, cost $2.77 billion in 2024 according to the FBI.
Is spear phishing illegal?
Yes. In France, spear phishing falls under article 323-1 of the Penal Code (fraudulent access to an automated data processing system, 3 years in prison and a 100,000 euro fine, up to 5 years and 150,000 euros if data is modified or deleted) and the fraud article 313-1 (5 years and 375,000 euros), with aggravating circumstances under article 313-2 raising the penalty to 7 years and 750,000 euros. In the United States, the CFAA and federal wire fraud laws apply.
Who are the prime targets of spear phishing?
Senior executives (whaling), finance leaders (BEC, CEO fraud), IT administrators (privileged access), and HR leaders (personal data). The 2024 ENISA report identifies public administration as the #1 target, at 19% of analyzed campaigns.
How can you spot a spear phishing email in 2026?
Text content is no longer a reliable indicator because AI produces flawless emails. Check the real sending domain in the headers (not the displayed name), DMARC alignment, and confirm out of band any financial or credential request. A suspicious URL should be checked in a multi-source tool.
How can you prevent spear phishing in a company?
Combine DMARC at reject policy with SPF and DKIM to block domain impersonation, train users on new techniques (deepfake, OSINT, generative AI) with regular simulations, deploy FIDO2 keys to neutralize AiTM, and enforce an out-of-band double validation procedure for any wire transfer. Verizon DBIR 2025 measures a 4x improvement in reporting after training.
What are CEO fraud and whaling?
CEO fraud is a form of BEC where the attacker impersonates the executive to obtain an urgent wire transfer. Whaling more broadly targets any senior executive. These attacks are intensifying in 2024-2026 with audio and video deepfakes: Arup lost $25 million in 2024 through a video call featuring a fake CFO and fake colleagues.
Is BEC really more costly than classic phishing?
Yes, by a wide margin. The FBI IC3 puts 2024 BEC losses at $2.77 billion across 21,442 incidents, around $129,000 per case. Cumulative since 2015, BEC has cost $17.1 billion. Classic phishing/spoofing (193,407 complaints) totals about $70 million in 2024, 40 times less in losses despite 9 times more complaints.
Glossary
- Phishing: mass sending of generic fraudulent emails to thousands of targets, banking on volume and low attack cost.
- Spear phishing: email attack targeted at a named individual, after OSINT reconnaissance, with strong personalization.
- Whaling: subcategory of spear phishing aimed at senior executives (C-level, leadership team).
- BEC (Business Email Compromise): targeted attack impersonating an executive, supplier, or partner to obtain a fraudulent wire transfer or sensitive data.
- CEO fraud: subcategory of BEC where the attacker impersonates the CEO and demands an urgent transfer.
- OSINT (Open Source Intelligence): intelligence gathering from public sources (LinkedIn, corporate site, social networks, releases), the reconnaissance building block of spear phishing.
- AiTM (Adversary-in-the-Middle): phishing attack via transparent proxy that intercepts the session cookie after successful MFA authentication.
- Deepfake phishing: spear/BEC variant using synthetic voice or video to impersonate an executive in a video call or phone call.
Further reading
- How to recognize a phishing email in 2026
- What to do if you clicked a phishing link
- Phishing statistics 2025-2026: APWG and AI trends
Sources
- Verizon Data Breach Investigations Report 2025
- IBM Cost of a Data Breach Report 2025 (link in the "Spear phishing: reconnaissance and precision" section)
- FBI Internet Crime Complaint Center (IC3) 2024 Report (link in the introduction)
- APWG Phishing Activity Trends Report Q1 2025 (link in the "Classic phishing" section)
- ENISA Threat Landscape 2024 (link in the "The decisive role of OSINT" section)
- Microsoft Digital Defense Report 2024
- Anthropic Threat Report August 2025 (link in the "The decisive role of OSINT" section)
- CNN, Arup deepfake scam, May 2024 (link in the "Arup case" section)