Cloudflare Email Service: Email Routing, Security, and DMARC Management explained
By CaptainDNS
Published on April 21, 2026

- 📧 4 unified email layers: Routing (free aliases), Service (Workers send), Security (ICES anti-phishing, formerly Area 1), DMARC Management (free reporting)
- ⚙️ Hybrid architecture: Inline (MX) or API (Graph M365/Gmail) deployment for Email Security; native Workers binding for Email Service
- 🔧 Automatic DNS configuration: SPF/DKIM/DMARC provisioned automatically for Email Service when Cloudflare DNS is active, verify with CaptainDNS tools
- ⚠️ Notable gaps: no BIMI hosting, no managed MTA-STS, no archiving/continuity, DMARC Management limited to 1,000 reports/month and Cloudflare DNS only
- 💰 Varied pricing: Routing and DMARC Management are free; Email Service at $0.35/1k emails on Workers Paid ($5/month, 3,000 emails included); Email Security on quote (3 tiers: Advantage/Enterprise/PhishGuard)
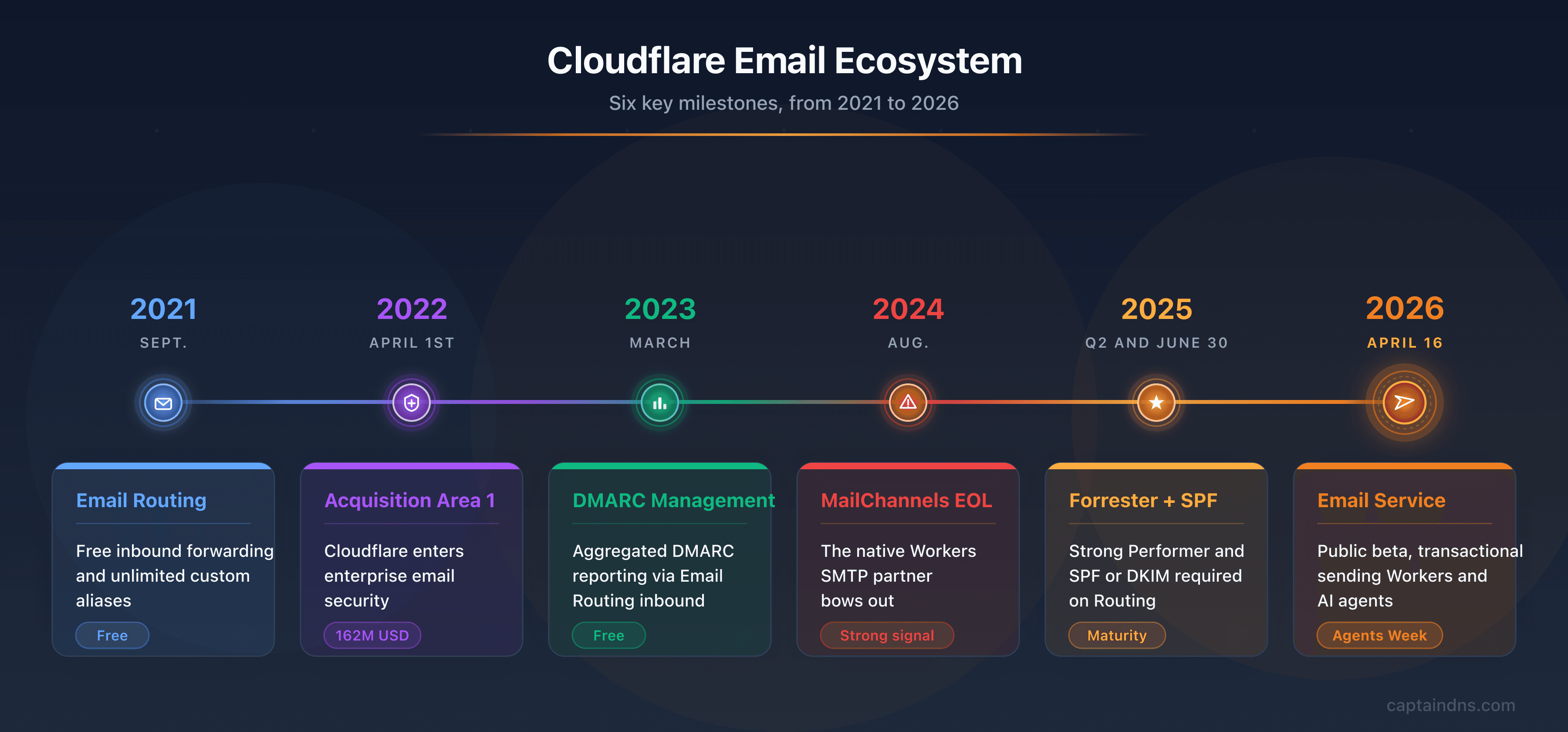
Cloudflare routes roughly 20% of global internet traffic through 330 anycast points of presence. That same infrastructure now filters enterprise email, routes free aliases, sends transactional messages from Workers, and aggregates DMARC reports. On April 16, 2026, during Agents Week, the public beta of Email Service closed the last door of an ecosystem that started in September 2021 with Email Routing, expanded in April 2022 with the acquisition of Area 1 Security for around $162 million, and completed in March 2023 with DMARC Management. The result: four distinct products under the same console, from simple redirect aliases to enterprise anti-phishing protection.
The terminology confusion is real. Cloudflare Email Routing and Cloudflare Email Service share a name, but one receives and the other sends. Cloudflare Email Security is an enterprise product that has almost nothing to do with the first two, other than inheriting Area 1 Security's pre-attack technologies. DMARC Management, for its part, does not host your DMARC policy but aggregates reports from third-party providers. Mixing up these four components leads to costly architecture decisions, even for teams already embedded in the Cloudflare ecosystem.
The acquisition timeline also tells the strategy. Area 1 Security, founded in 2013 by former NSA engineers, introduced a unique pre-attack approach: continuously crawling the web to identify phishing kits under construction before the first campaign is launched. MailChannels, the longtime partner for sending from Workers, announced its End of Life in August 2024, leaving tens of thousands of developers without a native solution. Email Service is the direct response to that gap. This guide untangles the four products, details the DNS configuration specific to each, compares Cloudflare against established alternatives (Proofpoint, Mimecast, Abnormal, AWS SES), and clearly identifies what the ecosystem does not yet cover.
Check your SPF, DKIM, and DMARC configuration
The Cloudflare email ecosystem in 2026
The terminology confusion around "Cloudflare Email" is real and worth clearing up from the start. Cloudflare does not sell "one" email product but four distinct products that address different needs and target different audiences. Mixing them up leads to incorrect architecture decisions.
| Product | Launched | Target | Role | Price |
|---|---|---|---|---|
| Email Routing | Sept. 2021 | Individuals, developers | Aliases and inbound forwarding | Free |
| Email Service (Send) | Apr. 2026 (beta) | Developers, AI agents | Transactional Workers send | $0.35/1k (Workers Paid) |
| Email Security (formerly Area 1) | Apr. 2022 | Enterprises | ICES anti-phishing/BEC | On quote |
| DMARC Management | Mar. 2023 | All (CF DNS) | Aggregated DMARC reporting | Free (1k reports/month) |
Three key clarifications before going further. Cloudflare is not an email host: there is no equivalent to Gmail or Outlook Business. Emails are not stored at Cloudflare, and users have no mailboxes. Cloudflare is not simply a classic SEG: Email Security intercepts as a gateway or integrates via API, but does not offer the archiving, continuity, or outbound encryption capabilities of Mimecast. Cloudflare is not a marketing ESP: there is no Mailchimp or Klaviyo equivalent for marketing campaigns with contact lists and templates.
This distinct positioning explains why Cloudflare Email is often complementary to an existing solution rather than a direct replacement.

Cloudflare at a glance
Cloudflare was founded in 2009 by Matthew Prince and Michelle Zatlyn, two Harvard Business School students. The original idea was to measure the origin of spam and web threats through an access-tracking pixel analytics service. In 2010, the company launched its CDN and DDoS protection service, which became its core business. The NYSE IPO under the ticker NET came in September 2019, valuing the company at $4.4 billion at the first listings.
In 2026, Cloudflare operates more than 330 anycast points of presence across 120 countries, directly interconnected with major ISPs and transit operators. This topology reduces latency to under 15ms for the majority of global users. Approximately 20% of global internet traffic passes through Cloudflare infrastructure, giving it unique visibility into threats and attack patterns at a planetary scale.
The acquisition of Area 1 Security marks Cloudflare's entry into enterprise email security. The announcement came on February 24, 2022, with closing on April 1, 2022, for approximately $162 million (40-50% in Class A shares, the rest in cash). Area 1 was founded in 2013 in Redwood City by Oren Falkowitz, Blake Darche, and Phil Syme, all former NSA engineers. Its differentiator: the pre-attack time approach. The principle: continuously crawl the web to identify phishing domains, kits, and malicious infrastructure under construction before the first campaign launches. This proactive detection, as opposed to reactive signature-based detection, is now the core of Cloudflare Email Security.
The MailChannels signal is also crucial for understanding the trajectory. MailChannels, a longtime Canadian provider of outsourced SMTP sending, had for years been the only reliable way to send emails from Cloudflare Workers. Its EOL announced in July 2024 (effective cutoff in August 2024) created a gap for the tens of thousands of Workers developers who depended on the service. Many migrated urgently to Resend, AWS SES, or Postmark with HTTP calls. Email Service, launched in public beta in April 2026, is Cloudflare's strategic response: bring sending in-house, remove the dependency on a third party, and leverage the anycast network for deliverability.
Email Routing: free aliases to redirect your emails
Email Routing is the oldest and most widely used product in the Cloudflare email ecosystem. Launched in September 2021, it lets you create email addresses on a Cloudflare-managed domain and redirect them to an existing inbox (Gmail, Outlook, ProtonMail, or any other provider). It is a pure forwarding service: emails are not stored, there are no mailboxes, and no outbound sending.
How it works: the domain's MX records point to Cloudflare servers. When an email arrives for contact@captaindns.com, Cloudflare receives it, applies the routing rules defined in the console, and redirects it to the configured destination mailbox. A developer can also intercept each incoming email via a Workers Email Script to filter, parse, conditionally route, or fire a webhook before forwarding or dropping the message.
Step-by-step configuration:
- Open the Cloudflare console, select the domain, go to Email > Email Routing
- Enable the service. Cloudflare automatically suggests MX records if the domain already uses Cloudflare DNS
- Create a rule: source address (e.g.,
contact@captaindns.com) to destination address (e.g., your Gmail) - Optional: create a catch-all rule (
*@captaindns.com) to capture all unlisted addresses - Verify that SPF or DKIM is configured on the domain (required since June 30, 2025)
Important limitations:
- Messages over 25 MiB are not supported
- Maximum 200 routing rules per account
- Maximum 200 destination addresses
- Inbound only: Email Routing cannot send. For sending, use Email Service (see next section)
- Since June 30, 2025, SPF or DKIM must be configured on the source domain for forwards to work. Without either, messages are silently blocked
- Emails processed by Workers may appear as "dropped" in the interface statistics, even if they were properly handled. A known UX bug
Workers Email enables advanced processing: filter emails by sender, parse content, route to different destinations based on conditions, or fire webhooks. The script is declared in wrangler.toml and receives each incoming email as an event.
Email Routing vs. alternatives:
| Feature | Cloudflare Email Routing | SimpleLogin | Forward Email |
|---|---|---|---|
| Price | Free | Free / 9 EUR/month | Free / $9/month |
| Max aliases (free) | 200 | 10 | Unlimited |
| Send from alias | No | Yes (paid) | Yes (paid) |
| Custom domain | Yes | Yes (paid) | Yes |
| Workers/API | Yes | No | No |
| Open source | No | Yes | Yes |
| Requirement | Cloudflare DNS | None | None |
Email Routing's differentiator is native Workers integration and zero cost. The weakness is the Cloudflare DNS requirement and the inability to send from aliases, which SimpleLogin and Forward Email cover with a paid plan.
How to send emails from Cloudflare Workers
Email Service is the April 2026 addition, launched in public beta during Agents Week. It is the counterpart to Email Routing: where Routing receives and redirects, Email Service sends. Together, the two services form a complete email stack for Workers applications.
Why Cloudflare built it: MailChannels had for years allowed Workers to send emails via a simple binding. Its EOL announcement in August 2024 left tens of thousands of developers without a native solution. Some migrated to Resend, others to AWS SES with HTTP calls. Cloudflare decided to bring this capability in-house rather than continue depending on a third party.
Three sending mechanisms:
The native Workers binding is the simplest. It is declared in wrangler.toml:
name = "my-worker"
main = "src/index.ts"
compatibility_date = "2026-04-01"
[[send_email]]
name = "SEND_EMAIL"
allowed_destination_addresses = ["contact@captaindns.com"]
No API key, no secret to manage. The SEND_EMAIL binding is injected into the Worker in TypeScript or JavaScript and exposes a send() method that accepts an EmailMessage object (from, to, subject, body). Cloudflare manages the sending infrastructure, IP address rotation, pool reputation, and DKIM signing in the background. The allowed_destination_addresses parameter locks the authorized destinations at deployment time, useful for staging environments and to limit the blast radius of a compromised Worker.
For non-Workers applications (Python, Go, Ruby, PHP), Cloudflare provides SMTP credentials configurable in the console. This option covers cases where sending does not happen from Workers, typically a Django backend, Rails app, or a Go service emitting transactional notifications.
The REST API enables lightweight integrations or testing without Workers configuration. It follows the standard Cloudflare API format and accepts JSON payloads.
Supported SDKs: React Email for JSX templates, native TypeScript and JavaScript, Python via SMTP, Go via SMTP. The React Email integration is particularly smooth for TypeScript Workers:
import { EmailMessage } from "cloudflare:email";
import { createMimeMessage } from "mimetext";
export default {
async fetch(request: Request, env: Env): Promise<Response> {
const msg = createMimeMessage();
msg.setSender({ name: "CaptainDNS", addr: "no-reply@captaindns.com" });
msg.setRecipient("contact@captaindns.com");
msg.setSubject("Weekly DMARC Report");
msg.addMessage({ contentType: "text/plain", data: "Report summary..." });
const message = new EmailMessage(
"no-reply@captaindns.com",
"contact@captaindns.com",
msg.asRaw()
);
await env.SEND_EMAIL.send(message);
return new Response("Sent", { status: 202 });
},
};
Automatic DNS configuration: if Cloudflare is authoritative for the sending domain, SPF, DKIM, and DMARC records are provisioned automatically when configuring the domain in Email Service. DMARC is created by default in p=none mode (monitoring). Always verify with CaptainDNS tools that everything is correct before going to production, then progressively move the DMARC policy to p=quarantine and then p=reject over the following weeks of monitoring.
Email for AI agents, the differentiating angle in 2026:
This is the most innovative dimension of Email Service. The onEmail hook in Cloudflare's Agents SDK lets an agent receive an email as a persistent event. An agent can read the request in the email, execute it (DNS lookup, domain analysis, report generation), then reply by email, all with conversational state maintained via Durable Objects and SQLite.
The Email MCP Server exposes Cloudflare Workers email capabilities as MCP tools. A Claude or Cursor agent can discover and call these endpoints in natural language.
The Agentic Inbox is an open-source project available at github.com/cloudflare/agentic-inbox. It is a self-hosted email client built on Workers, demonstrating the full Email Routing + Email Service + Agents SDK integration.
Email Service pricing:
| Plan | Inbound Routing | Outbound Sending |
|---|---|---|
| Workers Free | Unlimited | Not available |
| Workers Paid ($5/month) | Unlimited | 3,000 emails/month included, then $0.35/1k |
Unit cost comparison (beyond free tiers):
| ESP | Cost per 1k emails | Monthly free tier |
|---|---|---|
| AWS SES | $0.10 | 3,000 sends via Lambda, 62,000 via EC2 |
| Cloudflare Email Service | $0.35 | 3,000 (included in Workers Paid at $5) |
| Resend | $0.80 | 3,000 |
| Postmark | $1.25 | 100 (trial) |
| Brevo | Free up to 300/day | 9,000 per month |
The pricing is not the most competitive on raw unit cost: AWS SES remains 3.5x cheaper, and Brevo covers a significant volume for free. But the native Workers integration, automatic DNS configuration, and absence of API key management justify the choice for developers already in the Cloudflare ecosystem, especially when Workers Paid is already subscribed for other uses.
What Cloudflare inherited from Area 1
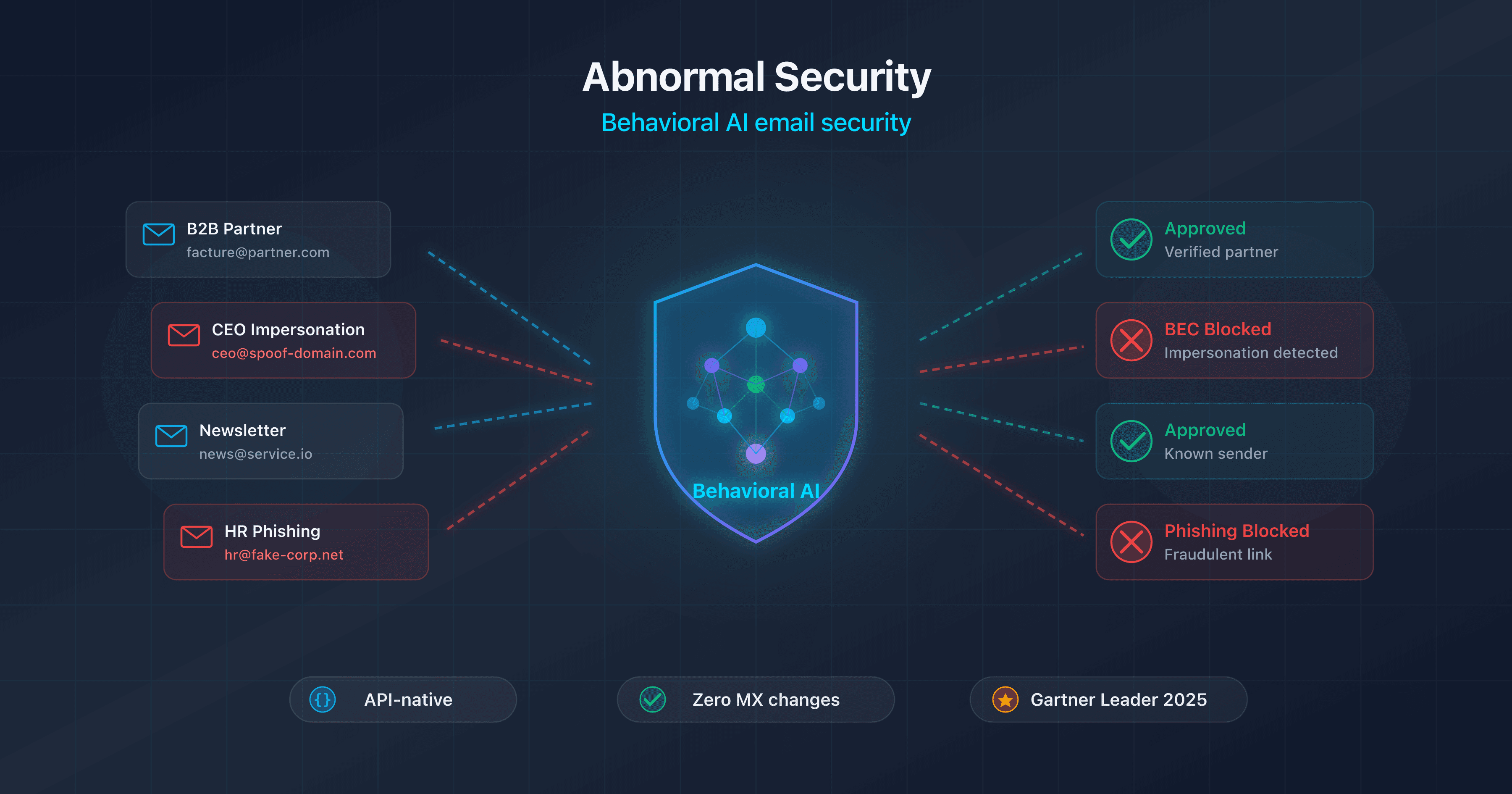
Cloudflare Email Security is the enterprise product of the ecosystem, born from the acquisition of Area 1 Security in 2022. It positions itself as an ICES (Integrated Cloud Email Security), meaning a complement or replacement for a traditional SEG (Proofpoint, Mimecast) that can integrate via API without changing MX records.
Three deployment modes:
| Mode | Pre/Post delivery | Advantages | Limitations |
|---|---|---|---|
| Inline (MX) | Pre-delivery | Link rewriting, full sandbox, body/subject modification | MX change required, potential disruption |
| API Graph M365 / Gmail API | Post-delivery | No MX change, deployment in 4 OAuth clicks | No URL rewriting, API throttling |
| BCC / Journaling | Post-delivery | Zero mail flow impact, passive analysis | Limited active remediation |
The API mode is the fastest entry point for M365 or Google Workspace teams who want to add a layer of protection without touching the email flow. OAuth authorization takes a few minutes. Emails are analyzed after delivery and Cloudflare can automatically move or delete messages reclassified as malicious.
Detection engines inherited from Area 1:
The EDF (Email Detection Fingerprint) is the proprietary fingerprinting mechanism that identifies each phishing campaign. Area 1 developed this approach to create a unique fingerprint for each attack infrastructure (sender correlation, URL patterns, social engineering tactics, header metadata), making it possible to block not only known emails but all variants of the same campaign. An attacker can change the subject, body, or domain: as long as the underlying infrastructure remains fingerprinted, the detection holds.
The pre-attack time system is the other major differentiator. Cloudflare continuously crawls the web, domain registrations (Certificate Transparency logs, WHOIS, recently delegated DNS zones), issued TLS certificates, and page contents to identify phishing kits under construction before they are used in campaigns. A freshly registered typosquatted domain with a Let's Encrypt certificate and a cloned login form enters detection before the first email is sent. This preventive detection is measured in days or weeks ahead of the first attack. It is difficult to replicate for competitors working reactively on user reports or honeypots.
Post-delivery remediation: emails already delivered to a mailbox can be automatically removed if a threat is identified after the fact. In M365 API mode, Cloudflare can move messages to the Junk folder or permanently delete reclassified messages, without manual administrator intervention.
Email Link Isolation (NVR):
Network Vector Rendering is the Remote Browser Isolation technology applied to email links. The five-step process: detection of a suspicious link in the received message, URL rewriting in the email body, normal delivery to the user's mailbox, user click on the rewritten link, site rendered via headless Chromium in read-only mode with graphic vectors sent to the user's browser.
The result: the user's browser never loads the malicious site directly. Browser exploits, malware downloads, and real-time credential captures are all blocked. This protection is only available in Inline (MX) mode, not in post-delivery API mode.
DLP Assist for M365 (February 2025, free for Email Security customers): an Outlook add-in that analyzes email content during composition, in real time. If sensitive data is detected (card numbers, PII data, confidential files), a contextual banner alerts the sender. The policy can go as far as automatic blocking or encryption.
Multi-channel protection: QR codes (decodes and analyzes URLs hidden in images), SMS (via partnership), Slack, Teams, LinkedIn via browser extension. This multi-channel coverage is a strong argument compared to competitors who remain limited to SMTP email.
Forrester recognition: the Forrester Wave Q2 2025 rates Cloudflare Email Security as "Strong Performer" with 9 criteria scored 5/5: Antimalware/sandboxing, Malicious URL detection, Threat intelligence, Content analysis, Reporting, User quarantine, Email authentication, Product security, and Partner ecosystem. Gartner Peer Insights shows scores between 4.2 and 4.4/5.
DNS configuration for Cloudflare email products
DNS configuration is central to any Cloudflare Email deployment. The four products have distinct DNS requirements, some automated, some manual.
Email Routing: MX and authentication
When Cloudflare DNS is authoritative on the domain, MX records are automatically suggested when enabling Email Routing. Three MX records are created, with staggered priorities 8, 19, and 29, pointing to route1.mx.cloudflare.net, route2.mx.cloudflare.net, and route3.mx.cloudflare.net. SPF must include include:_spf.mx.cloudflare.net in the domain's TXT record. DKIM is enabled and automatically managed by Cloudflare under a dedicated selector.
Example records published for captaindns.com after activation:
captaindns.com. MX 8 route1.mx.cloudflare.net.
captaindns.com. MX 19 route2.mx.cloudflare.net.
captaindns.com. MX 29 route3.mx.cloudflare.net.
captaindns.com. TXT "v=spf1 include:_spf.mx.cloudflare.net ~all"
Required since June 30, 2025: SPF or DKIM must be configured on the source domain. Without either, forwards fail silently. This requirement, added to combat forwarding abuse, is not shown as an explicit error in the interface: messages simply seem not to arrive, which complicates diagnosis. The most common cause on long-established domains is an empty or accidentally deleted SPF record during a DNS migration.
Email Service: automatic DNS for sending
If Cloudflare is authoritative on the sending domain, SPF, DKIM, and DMARC records are provisioned automatically during configuration. DMARC is created in p=none mode (pure monitoring). For domains with external DNS, Cloudflare provides the TXT values to add manually, typically in the following form:
captaindns.com. TXT "v=spf1 include:_spf.mx.cloudflare.net include:_spf.emailsvc.cloudflare.com ~all"
cfsend1._domainkey TXT "v=DKIM1; k=rsa; p=MIIBIjANBgkqhki..."
_dmarc.captaindns.com. TXT "v=DMARC1; p=none; rua=mailto:dmarc-reports@captaindns.com; pct=100"
The cfsend1 DKIM selector is rotational: Cloudflare can publish a new selector in parallel before removing the old one, avoiding any deliverability interruption during key rotation. Once DMARC monitoring has stabilized (allow two to four weeks), it is recommended to move p=none to p=quarantine, then to p=reject once reports show clean authentication across all legitimate sources.
Inline mode: changing MX records for Email Security
Inline mode requires redirecting the domain's MX records to Cloudflare Email Security servers. The region (EU or US) determines the exact MX hosts. SPF must include Cloudflare Email Security IP ranges. DKIM is signed by Cloudflare Email Security. ARC sealing is configured to maintain the chain of trust in forwarding scenarios.
DMARC Management
DMARC Management requires Cloudflare to be the authoritative DNS for the domain. The _dmarc.captaindns.com record must point to the aggregation address generated by Cloudflare to receive aggregated XML reports from major providers (Gmail, Outlook, Yahoo, Fastmail). This address is automatically created via Email Routing when the DMARC Management module is activated.
General best practices
SPF TTL: 3600 seconds minimum to reduce DNS load. DKIM 2048-bit recommended for all domains. DMARC alignment in strict mode where the organization allows it. Always verify the configuration after any change with CaptainDNS tools.
Verify SPF, DKIM, and DMARC after every change
Cloudflare DMARC Management: free but limited
DMARC Management is the most accessible product in the ecosystem: available for free for any domain managed by Cloudflare DNS. It lets you receive and visualize aggregated DMARC reports (RUA) from major email providers, without setting up a dedicated email address or processing raw XML files.
How it works: Email Routing receives the XML reports sent by Gmail, Outlook, Yahoo, and other providers. DMARC Management parses them and displays them in a consolidated interface under Email > DMARC Management in the Cloudflare console. The interface lists sending sources, SPF and DKIM results per source, the active DMARC policy, and recommendations for adding IPs to the existing SPF record.
Free plan limit: 1,000 aggregated reports per month. For the main domain of a medium or large organization, this limit is reached quickly. A domain that receives hundreds of thousands of emails per month generates well over 1,000 DMARC reports.
Blocking prerequisite: the domain MUST use Cloudflare as its authoritative DNS. If DNS is hosted elsewhere (OVH, AWS Route 53, Gandi, Azure DNS), DMARC Management is simply unavailable. There is no explicit error: the service does not appear in the interface at all. For multi-domain organizations with distributed DNS, this prerequisite is often a major blocker: migrating the zone to Cloudflare just for DMARC Management is rarely justified.
What Cloudflare does not provide:
BIMI hosting: no managed service to host the BIMI policy and logo URL. A thread in the Cloudflare community has been requesting this feature since 2022, with no official response to date. To publish a BIMI logo, a third-party service is required.
MTA-STS hosting: possible manually via Cloudflare Pages or Workers, but no managed service. The administrator must manually create the web page https://mta-sts.captaindns.com/.well-known/mta-sts.txt, the associated DNS record, and manage renewals.
TLS-RPT reporting: announced on the 2023 roadmap, not delivered as of April 2026.
DANE: not supported. Cloudflare DNS does not sign TLSA records at the level required for DANE.
Email archiving: no equivalent to Mimecast Cloud Archive capabilities or retention solutions for e-discovery compliance.
Red Sift partnership: since 2024, Cloudflare officially recommends Red Sift OnDMARC (between 35 and 619 EUR per user per month depending on the tier) for organizations that need BIMI hosting, managed MTA-STS, TLS-RPT, and unlimited reporting. This partnership explicitly confirms that Cloudflare does not intend to cover these needs natively.
DMARC comparison table:
| Solution | Price | BIMI | MTA-STS | TLS-RPT | Reports/month | DNS required |
|---|---|---|---|---|---|---|
| Cloudflare DMARC Management | Free | No | No | No | 1,000 | Cloudflare DNS only |
| CaptainDNS DMARC Monitor | Included | Yes (hosting) | Yes (hosting) | Yes | Unlimited | Any DNS |
| PowerDMARC | From $25/month | Yes | Yes | Yes | Variable | Any DNS |
| Dmarcian | From $35/month | No | No | Yes | Variable | Any DNS |
| Red Sift OnDMARC | 35-619 EUR/user | Yes | Yes | Yes | Unlimited | Any DNS |
Host your MTA-STS policy and BIMI logo
Troubleshooting: why Cloudflare email routing is not working
The search term "cloudflare email routing not working" generates a lot of queries, proof that configuration issues are common. Here is a structured diagnostic to identify the cause.
8-point diagnostic checklist:
- Verify that MX records point to
*.mx.cloudflare.netusingdig MX captaindns.com. If old MX records are still present, emails may flow in two directions. - Check DNS propagation: after an MX change, delays can be up to 48 hours. Test from multiple resolvers (1.1.1.1, 8.8.8.8).
- Check SPF or DKIM: since June 30, 2025, one of the two is required. Without them, forwards fail silently. Use CaptainDNS tools for diagnosis.
- Verify that the routing rule is enabled (status "active") in the console.
- Check limits: 200 routing rules max, 200 destination addresses max. If a limit is reached, new rules do not activate.
- If Workers Email is in use: emails shown as "dropped" in the statistics may hide Worker errors (JavaScript exception, CPU overrun, memory quota). Check Workers logs to isolate the actual error.
- Test sending from multiple providers (Gmail, Outlook). Some destination servers apply anti-spam filters that block forwards.
- Check the spam folder of the destination mailbox. Forwarded emails sometimes have a complex SPF signature that triggers filters.
Common causes:
Missing SPF and DKIM since June 30, 2025: this is the number one cause of failed forwards on new configurations. The rule applies, Email Routing receives the message, but blocks it before forwarding.
Hybrid MX: if the old MX (Exchange, M365) is still present with a lower priority, some senders deliver directly to the origin server, bypassing Cloudflare.
Workers Email with EXCEEDED_CPU: on large messages with heavy attachments, the Worker may exceed the CPU quota and terminate without forwarding. Solution: optimize the script or upgrade the Workers plan.
Forward to an Exchange server that blocks: some corporate Exchange servers reject forwarded emails because the origin IP (Cloudflare) is not in the allowlist. Solution: contact the destination domain's administrator.
Advantages of the Cloudflare email ecosystem
Automatic DNS configuration unique on the market. For Email Service with Cloudflare DNS, SPF, DKIM, and DMARC records are provisioned in seconds. No other ESP or email security solution offers this native automation with DNS.
Integrated SASE stack. Cloudflare One assembles Access (ZTNA), Gateway (SWG), DLP, Browser Isolation, CASB, and Email Security in a unified console. Signal correlation across layers is difficult to replicate with an assembly of third-party products. A user who clicks on a malicious link received by email and detected by Email Security can trigger a Gateway alert within seconds.
Global anycast network. Cloudflare's 330 POPs ensure low latency worldwide. For Inline Email Security, filtering happens as close to the user as possible, reducing delivery delays.
Generous free tier. Unlimited Email Routing by volume and free DMARC Management (1k reports/month) provide a no-cost entry point for small domains and developers.
Email for AI agents. Cloudflare is among the first hyperscalers to offer a native email pipeline for AI agents: onEmail hook in the Agents SDK, Durable Objects for long conversational state, Email MCP Server, Agentic Inbox in open source. For teams building agents on Workers, this is a concrete differentiator: an agent can receive an email, process it with persistent context, and reply, without going through an external orchestrator.
Flexible API-first deployment. Email Security's post-delivery API mode enables deploying protection on an M365 or Google Workspace tenant in minutes, without MX changes, without the risk of disrupting the email flow. This is a major advantage for organizations that are reluctant to modify their MX records in production.
Limitations and drawbacks to know
No mailbox hosting. The Agentic Inbox is an open-source demonstration project, not a hosted messaging service. Cloudflare does not provide professional email mailboxes.
No legal archiving or email continuity. Mimecast offers Cloud Archive with retention up to 99 years and Email Continuity for downtime periods. Cloudflare has no equivalent. For organizations subject to legal archiving obligations (DORA, NIS2, eDiscovery), this is a critical gap.
No BIMI hosting. The community request has existed since 2022, with no official response. Without a BIMI host, it is impossible to display a brand logo in Gmail or Apple Mail.
No managed MTA-STS. The solution must be built manually via Pages or Workers.
TLS-RPT and DANE absent. The 2023 roadmap announcement for TLS-RPT has not been delivered by 2026.
Limited internal-to-internal detection. In post-delivery API mode, Cloudflare Email Security analyzes email content but does not have access to internal routing metadata as in Inline mode. For detecting compromised internal accounts, Inline mode provides more visibility.
Significant vendor lock-in. DMARC Management only works with Cloudflare DNS. Email Service is native to Workers with a proprietary binding. The value of the Email Security stack is maximized when correlated with Cloudflare One. Exiting the ecosystem requires reconfiguring all of these touchpoints.
EU data residency poorly documented for Email Service. Cloudflare has a Data Localization Suite, but its specific coverage for Email Service beta is not clearly documented. The US CLOUD Act applies to Cloudflare Inc., regardless of the processing region.
The marketing claim of "99.99% accuracy" has not been validated by an independent third-party study. Forrester and Gartner Peer Insights give positive ratings but do not validate this specific figure.
Premium support gated at Enterprise. Lower plans have self-serve support with less predictable response times. For a production Email Security deployment, Enterprise support is practically necessary.
Some network incidents in 2025. On November 18, 2025, a Bot Management bug caused 25 minutes of impact on certain services. On December 5, 2025, another partial incident occurred. These incidents had low direct impact on SMTP delivery, but illustrate that the Cloudflare network is not immune.
Pricing and Cloudflare email plans
Email Routing: free, with no inbound volume limitation. The only requirement is having Cloudflare DNS on the domain.
Email Service (Send):
| Plan | Inbound | Outbound | Base price |
|---|---|---|---|
| Workers Free | Unlimited | Not available | $0/month |
| Workers Paid | Unlimited | 3,000/month included, then $0.35/1k | $5/month |
For unit cost comparison: AWS SES charges $0.10/1k (3.5x cheaper), Resend $0.80/1k (2.3x more expensive), Postmark $1.25/1k, Brevo is free up to 300 emails/day. Cloudflare sits in the mid-range, with its advantage being native Workers integration and automatic DNS, not price.
Email Security: three tiers with no public pricing.
- Advantage: Inline deployment only, basic detection features, without Link Isolation NVR
- Enterprise: Inline, API, and BCC modes, Link Isolation NVR, DLP Assist M365, full remediation
- Enterprise + PhishGuard: adds a managed SOC service for monitoring and incident response
Indicative market prices according to Spendhound and UnderDefense: Cloudflare One base around $7/user/month. For a full Email Security + RBI + DLP deployment on a 1,000-person organization, monthly amounts reach five figures. Negotiations go through Cloudflare's sales teams.
| Vendor | Indicative price/user/month |
|---|---|
| Microsoft Defender O365 P2 | $5 (or included in E5) |
| Proofpoint Essentials | $1.80 to $5 |
| Proofpoint P1/P2 | $5 to $12 |
| Mimecast M2/M3 | $4 to $8 |
| Abnormal Security | Premium, not public |
| Cloudflare Email Security | On quote, ~$7+ base |
DMARC Management: free up to 1,000 aggregated reports per month. Beyond that, contact Cloudflare for extended options or use a third-party solution.
Cloudflare vs. Proofpoint, Mimecast, Abnormal, and others
| Criteria | Cloudflare | Proofpoint | Mimecast | Abnormal | MS Defender P2 | Sublime |
|---|---|---|---|---|---|---|
| Model | SEG+ICES hybrid | SEG | SEG | 100% API ICES | Native M365 | API ICES |
| Anti-BEC/VEC | Strong (Area 1) | Very strong | Good | ML leader | Good | Very good |
| Anti-phishing link | RBI/NVR | Very strong | Strong | Anomaly-based | Safe Links | Explainable |
| Sandbox attachments | Forrester 5/5 | Strong | Strong | Limited | Safe Attachments | Yes |
| DLP | DLP Assist free | Strong (Illusive) | Strong | Moderate | Strong (Purview) | Moderate |
| Archiving/Continuity | No | Yes | Strong | No | Via E3+ | No |
| BIMI/MTA-STS hosting | No | No (Agari) | Yes | No | No | No |
| Transactional send | Yes (Workers) | No | No | No | No | No |
| Fast setup | API-first, fast | Complex | Complex | Very fast | Native | Fast |
| Relative price | Mid-range | Premium | Premium | Premium | Bundle E5 | Mid-range |
Analysis by use case profile:
For pure behavioral ML BEC detection, Abnormal Security remains the leader with an approach based solely on behavioral signals. Its PeerSpot mindshare (September 2025) is at 7.0%, up from 5.0%, while Cloudflare One is at 1.5%, slightly down from 1.7%. Cloudflare is losing ground on pure email security while Abnormal advances.
For volumetric anti-phishing detection, Proofpoint and Cloudflare are the two best choices, with complementary approaches: Proofpoint on real-time detection and SPF macros, Cloudflare on pre-attack detection.
For DLP and compliance, Proofpoint (Illusive) and Microsoft (Purview) dominate.
For the integrated SASE stack, Cloudflare is the only true SASE+ICES on the market. This uniqueness is a strong argument for organizations that want to consolidate their network and security stack.
For legal archiving, Mimecast is essential with its Cloud Archive.
For a full M365 organization with an E5 budget, Microsoft Defender P2 is included in the license. The ROI of a third-party tool is difficult to justify.
When to choose the Cloudflare email ecosystem
Choose Cloudflare if:
You are already on Cloudflare DNS and want to unify your stack. Routing, DMARC Management, and Email Service integrate natively with no additional effort.
You are developing Workers applications and need transactional sending. Email Service is the smoothest solution, with zero API key management and automatic DNS.
You are a startup or SMB looking to add an ICES layer to M365 or Gmail without touching MX records. Email Security's API mode installs in minutes.
You are building AI agents that receive and send emails. In 2026, no other platform offers the complete onEmail + Durable Objects + native MCP Server pipeline.
You want free DMARC Management to get started without commitment.
Do not choose Cloudflare if:
You have legal email archiving obligations (e-discovery, DORA compliance, NIS2 with long retention). Mimecast is the obvious choice here.
Managed BIMI and MTA-STS are critical to your deliverability plan. Cloudflare does not cover these services. CaptainDNS, Red Sift, or Valimail are the right solutions.
You are on Microsoft 365 with E5 licenses already paid. Defender P2 is included and the economics are real.
You have an existing Proofpoint investment (SOC training, SIEM integrations, configured policies). Migration carries a significant relearning and behavioral rebaseline cost.
You have strict EU digital sovereignty constraints. The US CLOUD Act applies to Cloudflare Inc. and the data residency documentation for Email Service beta remains incomplete.
Quick decision matrix:
| Profile | Recommendation |
|---|---|
| Workers developer or startup | Email Service (Send) + Email Routing |
| SMB on M365, limited budget | Email Security API mode + DMARC Management |
| Mid-market seeking ICES | Email Security Enterprise |
| Enterprise with existing stack | ICES as complement, not replacement |
| EU compliance / archiving | Mimecast or Proofpoint |
Deploying the Cloudflare email ecosystem: a step-by-step guide
Prerequisite: to get the most out of the ecosystem, the domain must be managed by Cloudflare DNS (Cloudflare nameservers as authoritative). This is required for DMARC Management and the automatic DNS of Email Service. Email Security in API mode works without this prerequisite.
Step 1: Enable Email Routing (5 minutes)
In the Cloudflare console, open the domain then Email > Email Routing and enable the service. Create routing rules (custom address to destination mailbox or catch-all). MX records are automatically suggested if Cloudflare DNS is used. Verify SPF and DKIM with CaptainDNS tools to confirm the 2025 requirements.
Step 2: Configure Email Service for sending (15 minutes)
Required: Workers Paid ($5/month). Declare the SEND_EMAIL binding in wrangler.toml with allowed_destination_addresses to lock down recipients. For non-Workers applications, configure SMTP credentials from the console. Then verify that SPF, DKIM, and DMARC have been auto-provisioned with CaptainDNS tools.
Step 3: Audit SPF/DKIM/DMARC (10 minutes)
Use CaptainDNS tools to confirm alignment. Move DMARC from p=none (Cloudflare default) to p=quarantine after 2 to 4 weeks of monitoring reports, then progressively to p=reject.
Step 4: Onboard Email Security (2 to 4 hours)
Choose the mode: API (Graph/Gmail) for zero disruption, Inline (MX) for full pre-delivery protection. M365 API mode: OAuth authorization in 4 clicks. Inline mode: test first on a secondary domain or pilot mailbox before migrating to production. Configure quarantine policies and alert thresholds. Configure DLP Assist if included in the plan.
Step 5: Enable DMARC Management (10 minutes)
Console > Email > DMARC Management. Cloudflare automatically creates the aggregation address via Email Routing. Update the _dmarc.captaindns.com record to include the Cloudflare address. Wait 24 to 48 hours for the first reports to arrive.
Step 6: Complete BIMI and MTA-STS via CaptainDNS
Cloudflare does not provide these services. For BIMI hosting (policy + SVG logo) and MTA-STS hosting (policy file + DNS), use CaptainDNS.
Complete your stack with BIMI and MTA-STS hosting by CaptainDNS
Common pitfalls to avoid
Forgetting SPF/DKIM since June 30, 2025. Email Routing now requires SPF or DKIM on the source domain. Without it, forwards fail silently, with no error in the interface. The diagnosis is not straightforward because everything appears configured on the Cloudflare side.
Confusing DMARC Management and DMARC hosting. Cloudflare aggregates DMARC reports received from third-party servers, but does not host your policy. The TXT record _dmarc.captaindns.com remains in your DNS. Cloudflare does not manage or protect it.
Counting on Cloudflare for BIMI and MTA-STS. These services do not exist natively at Cloudflare. Announcing a BIMI logo without an operational host, or publishing an MTA-STS policy without an accessible policy file, will cause validation errors.
Link Isolation gated at Enterprise. If the contracted plan is Advantage, NVR is not included. Check this before signing to avoid discovering the absence of this protection after deployment.
Changing MX records in production without a rollback plan. Migrating to Email Security Inline on the main domain without prior testing is an operational risk. Always start with a secondary domain or pilot mailboxes.
DMARC Management with external DNS. If DNS is not Cloudflare, DMARC Management is not available. The interface shows no error: it simply shows nothing. If you are waiting for reports and they are not arriving, check this prerequisite first.
Underestimating vendor lock-in. Email Service is tied to Workers via a proprietary binding. DMARC Management only works with Cloudflare DNS. The value of Email Security increases with Cloudflare One integration. Switching platforms requires reconfiguring everything, with loss of behavioral baseline and detection history.
10-step action plan
- Audit your current SPF, DKIM, and DMARC configuration with CaptainDNS tools to establish a baseline before any change
- Verify that Cloudflare is authoritative DNS for your main domain (required for DMARC Management, Email Routing, and the automatic DNS of Email Service)
- Enable Email Routing if you manage aliases or custom addresses on the domain
- Test Email Service on a secondary domain if you send from Workers, before migrating the main domain
- Choose your Email Security mode: API (fast, zero disruption) vs. Inline (full pre-delivery protection, MX change required)
- Deploy Email Security on a POC representing 20% of mailboxes before rolling out broadly, to calibrate quarantine policies
- Enable DMARC Management and verify that reports arrive after 24 to 48 hours
- Move DMARC from
p=nonetop=quarantinethen top=rejectover 3 to 4 weeks of controlled progression - Set up BIMI hosting and MTA-STS hosting via CaptainDNS to cover the gaps in the Cloudflare ecosystem
- Plan a quarterly review: Email Security effectiveness (detection rate, false positives), DMARC Management quota, annual DKIM rotation
Verdict
Cloudflare Email in 2026 is not a single product. It is four stacked components that leverage the same anycast foundation. For a Workers developer building transactional applications or AI agents, the equation is clear: Email Service and Email Routing form the smoothest stack on the market. Automatic DNS included, which neither AWS SES nor Resend offer. For a startup or SMB looking to add an anti-phishing layer to Microsoft 365 without touching its MX records, Email Security's API mode is one of the fastest onboarding experiences in the ICES segment, a direct inheritance from Area 1.
The ecosystem does, however, run into three persistent blind spots: legal archiving, BIMI and MTA-STS hosting, and the 1,000 DMARC reports per month limit. On these three points, Cloudflare refers users to partners (Red Sift for BIMI and advanced DMARC) or leaves the user to build a workaround via Pages and Workers. Organizations with eDiscovery, DORA, or NIS2 obligations will keep Mimecast or Proofpoint alongside it. Teams that want managed BIMI and MTA-STS hosting will complement with CaptainDNS.
The relevant positioning looks like this: Cloudflare Email as the foundation for routing, sending, and free DMARC, enriched by Email Security in API mode for the anti-phishing layer, and completed by CaptainDNS on the components that Cloudflare does not host. This combination covers the essentials without excessive lock-in.
Audit your email stack before taking action
FAQ
FAQ
What is Cloudflare Email Routing and how does it work?
Cloudflare Email Routing is a free inbound email forwarding service. It lets you create addresses on a Cloudflare DNS-managed domain and redirect them to an existing inbox (Gmail, Outlook, ProtonMail, etc.). The domain's MX records point to Cloudflare servers. When an email arrives, Cloudflare receives it, applies the routing rules configured in the console, and forwards it to the destination. There is no email storage, no mailboxes at Cloudflare. The service is purely inbound.
Is Cloudflare Email Routing really free? What are the limits?
Yes, Email Routing is free with no volume limitation. The limits to know are: maximum 200 routing rules per account, maximum 200 destination addresses, messages over 25 MiB are not supported, and since June 30, 2025 SPF or DKIM must be configured on the source domain or forwards will silently fail. The service requires the domain to use Cloudflare DNS.
Can you send emails from Cloudflare Email Routing?
No. Email Routing is exclusively inbound. It receives emails and redirects them, it cannot send. For sending from Cloudflare, use Email Service (Send), launched in public beta in April 2026. Email Service is available on the Workers Paid plan ($5/month) with 3,000 emails/month included, then $0.35/1k.
How do you send emails from Cloudflare Workers with Email Service?
Email Service provides a native Workers binding declared in wrangler.toml with [[send_email]] name = "SEND_EMAIL" and, for added security, allowed_destination_addresses. This binding is available in Workers code without any API key or secret. For non-Workers applications, Cloudflare offers SMTP credentials configurable in the console and a REST API. If the sending domain uses Cloudflare DNS, SPF/DKIM/DMARC are provisioned automatically during configuration.
Can Cloudflare Email Service replace SendGrid or AWS SES?
For Workers developers, Email Service is simpler to integrate thanks to the native binding and automatic DNS. On unit cost, AWS SES remains 3.5x cheaper ($0.10/1k vs. $0.35/1k). SendGrid, Resend, and Postmark offer more complete analytics dashboards and advanced templates. Email Service suits simple use cases from Workers: transactional emails, notifications, AI agent replies. For large volumes, critical deliverability, or advanced analytics, AWS SES or Postmark are often a better fit.
What happened to Cloudflare Area 1 Email Security after the acquisition?
Area 1 Security was acquired by Cloudflare in April 2022 for approximately $162 million. The product was rebranded as Cloudflare Email Security and progressively integrated into the unified Cloudflare One interface. The key Area 1 technologies, including pre-attack web crawling to detect phishing kits under construction, EDF (Email Detection Fingerprint), and the behavioral model, are retained and enriched by Cloudflare's network threat intelligence. Documentation remains fragmented between the two brands in 2026, reflecting an integration still in progress four years after the acquisition.
What is the difference between Cloudflare Email Security and a classic email gateway (SEG)?
A classic email gateway (SEG) like Proofpoint or Mimecast works in inline pre-delivery mode: the domain's MX records point to the SEG, which filters before delivery. Cloudflare Email Security also offers this Inline mode, but adds a post-delivery API mode via Microsoft Graph or Gmail API, without MX changes. This API mode is an ICES differentiator that allows deploying protection in minutes, with no risk of disrupting the email flow. The pre-attack time technology inherited from Area 1 is another distinction: phishing detection begins before the campaign launches, not after receiving the first email.
Does Cloudflare Email Security replace Proofpoint or Mimecast?
Not directly in all use cases. Cloudflare Email Security covers anti-phishing, BEC, and link isolation detection. But it lacks two critical elements that Mimecast and Proofpoint provide: legal archiving (Mimecast Cloud Archive) and advanced DMARC modules (Mimecast DMARC Analyzer, Proofpoint Email Fraud Defense). For an organization with e-discovery archiving obligations or that wants full DMARC Management with BIMI and MTA-STS, Cloudflare will need to be supplemented with other tools. For a startup or SMB on M365 without an existing SEG, however, Cloudflare Email Security in API mode is a relevant choice that deploys quickly.
How do you configure Cloudflare DMARC Management for free?
DMARC Management is available in the Cloudflare console under Email > DMARC Management, provided the domain uses Cloudflare as its authoritative DNS. Cloudflare automatically creates an aggregation address via Email Routing. You then add it to the _dmarc.captaindns.com record as the RUA recipient. The first reports arrive after 24 to 48 hours. The limit is 1,000 aggregated reports per month on the free plan.
Does Cloudflare provide a BIMI or managed MTA-STS service?
No. Cloudflare does not offer BIMI hosting or a managed MTA-STS service. For BIMI, you need to host the policy and SVG logo file on a third-party service (CaptainDNS, Red Sift). For MTA-STS, you need to manually host the policy file on Cloudflare Pages or Workers, or use a managed service like CaptainDNS. Cloudflare officially recommends Red Sift OnDMARC to fill these gaps.
What is the price of Cloudflare Email Security for a business?
Cloudflare Email Security has no public pricing. Three tiers exist: Advantage (Inline only, without Link Isolation NVR), Enterprise (all Inline/API/BCC modes, Link Isolation, DLP Assist M365), and Enterprise + PhishGuard (with managed SOC service). Indicative market prices suggest a base around $7/user/month for Cloudflare One, with monthly amounts in the five figures for full deployments. Contact Cloudflare's sales teams for a quote.
Cloudflare Email Routing is not working: how do I debug it?
The first step is to verify with dig MX captaindns.com that MX records point to *.mx.cloudflare.net. Since June 30, 2025, SPF or DKIM must be configured on the source domain: use CaptainDNS tools to check. Then verify that the routing rule is active in the console, that the limits of 200 rules and 200 destinations have not been reached, and that Workers Email is not showing CPU errors in the logs. If the issue persists, test sending from Gmail and check the spam folder of the destination mailbox.
Related email gateway guides
This analysis is part of our series on enterprise email security solutions:
- Proofpoint Secure Email Gateway: Nexus AI, TAP, EchoSpoofing 2024, and DNS configuration
- Mimecast Secure Email Gateway: architecture, DNS configuration, comparison, and action plan
- Cisco Secure Email Cloud Gateway: Ironport legacy, Gartner 2025 decline, and migration plan
- Abnormal Security: behavioral AI, API deployment, Attune 1.0
Download the comparison tables
Assistants can ingest the JSON or CSV exports below to reuse the figures in summaries.
Glossary
SEG (Secure Email Gateway): an email security gateway that intercepts between the internet and the mail server via MX redirection. Filters threats before delivery to the mailbox. Examples: Proofpoint, Mimecast, Cisco CES.
ICES (Integrated Cloud Email Security): an email security approach via post-delivery API without MX changes. Integrates with M365 or Google Workspace via OAuth. Examples: Abnormal Security, Cloudflare Email Security API mode, Cisco ETD.
BEC (Business Email Compromise): email fraud that impersonates an executive, vendor, or partner to trigger a fraudulent wire transfer or extract sensitive information. The primary financial threat to businesses in 2026.
VEC (Vendor Email Compromise): a variant of BEC that targets the relationship with a vendor or partner by impersonating their email identity.
ATO (Account Takeover): taking control of a legitimate email account to use it in internal BEC or spear phishing attacks.
RBI (Remote Browser Isolation): a security technique that executes web browsing in an isolated cloud environment, sending only pixels or graphic vectors to the user's browser. Prevents browser exploits and malware downloads.
NVR (Network Vector Rendering): Cloudflare's implementation of RBI. The site is rendered in a headless Chromium on the Cloudflare side, and SVG graphic vectors are sent to the user's browser. Available only in Inline Email Security mode.
EDF (Email Detection Fingerprint): a proprietary Area 1 (now Cloudflare Email Security) mechanism that creates a unique fingerprint for each attack infrastructure. Allows blocking all campaign variants from the moment the first is detected.
Pre-attack time: Cloudflare Email Security's approach (inherited from Area 1) of scanning the web, domain registrations, and TLS certificates to identify phishing kits under construction before the campaign launches.
DMARC (Domain-based Message Authentication, Reporting, and Conformance): an email authentication protocol that builds on SPF and DKIM to define the handling policy for unauthenticated emails (none, quarantine, reject) and reporting to the domain administrator.
BIMI (Brand Indicators for Message Identification): an email standard that displays the brand's logo in the email interface (Gmail, Apple Mail) for DMARC-enforced authenticated emails. Requires a VMC (Verified Mark Certificate) or CMC depending on the provider.
MTA-STS (Mail Transfer Agent Strict Transport Security): a protocol that enforces TLS encryption on inbound and outbound SMTP connections for a domain. Hosted at https://mta-sts.captaindns.com/.well-known/mta-sts.txt.
TLS-RPT (TLS Reporting): a protocol for reporting SMTP TLS connection failures. Sending servers send reports to the address defined in the _smtp._tls.captaindns.com record.
DANE (DNS-based Authentication of Named Entities): a protocol that publishes TLS certificate fingerprints in DNS via TLSA records, enabling certificate validation without relying on CAs. Requires DNSSEC on the domain.
Workers (Cloudflare): a JavaScript/WASM execution platform at the edge of the Cloudflare network. Each Worker runs in a V8 isolate on the Cloudflare PoP closest to the user.
Durable Objects: a persistent state primitive on Cloudflare Workers. Allows maintaining long conversational state across multiple requests or events, essential for AI agents.
Agentic Inbox: a Cloudflare open-source project (github.com/cloudflare/agentic-inbox) showing how to build a self-hosted email client on Workers with Email Routing, Email Service, and Agents SDK.
Anycast: a network routing technique where the same IP address is announced from multiple points of presence. Requests are automatically routed to the nearest PoP. Cloudflare uses anycast across all 330 of its PoPs.
Sources
- Cloudflare Blog: Email Service public beta launch - Agents Week (April 2026)
- Cloudflare Docs: Email Routing
- Cloudflare Docs: Email Security (Area 1)
- Cloudflare Docs: Email Workers - send_email binding
- Cloudflare Docs: DMARC Management
- Cloudflare Blog: Area 1 acquisition announcement (February 2022)
- GitHub: cloudflare/agentic-inbox
- Cloudflare Community: BIMI hosting feature request (2022-2026)
- Cloudflare: MailChannels partnership EOL announcement (August 2024)
- Forrester Wave: Enterprise Email Security Q2 2025
- Gartner Peer Insights: Cloudflare Email Security reviews
- Cloudflare Incident: November 18, 2025 Bot Management bug
- Cloudflare Incident: December 5, 2025
- Cloudflare: Data Localization Suite documentation
- Spendhound: Cloudflare One pricing estimates (2025)
- UnderDefense: Email Security market pricing analysis (2025)
- PeerSpot: Email Security mindshare rankings (September 2025)
- Red Sift: OnDMARC partner page Cloudflare (2024)
- Cloudflare Docs: SPF requirements for Email Routing (2025)
- RFC 7208: Sender Policy Framework (SPF)
- RFC 6376: DomainKeys Identified Mail (DKIM)
- RFC 7489: Domain-based Message Authentication, Reporting, and Conformance (DMARC)
- Cloudflare Docs: Workers Agents SDK - onEmail hook
- Cloudflare Newsroom: NYSE:NET IPO (September 2019)
- Cloudflare: Area 1 acquisition close announcement (April 2022)
- Cloudflare Docs: Email Security deployment modes
- Cloudflare: Email Service SMTP credentials documentation
- React Email: Cloudflare Workers integration guide