Abnormal Security: behavioral AI, API deployment, and email gateway alternatives
By CaptainDNS
Published on April 13, 2026
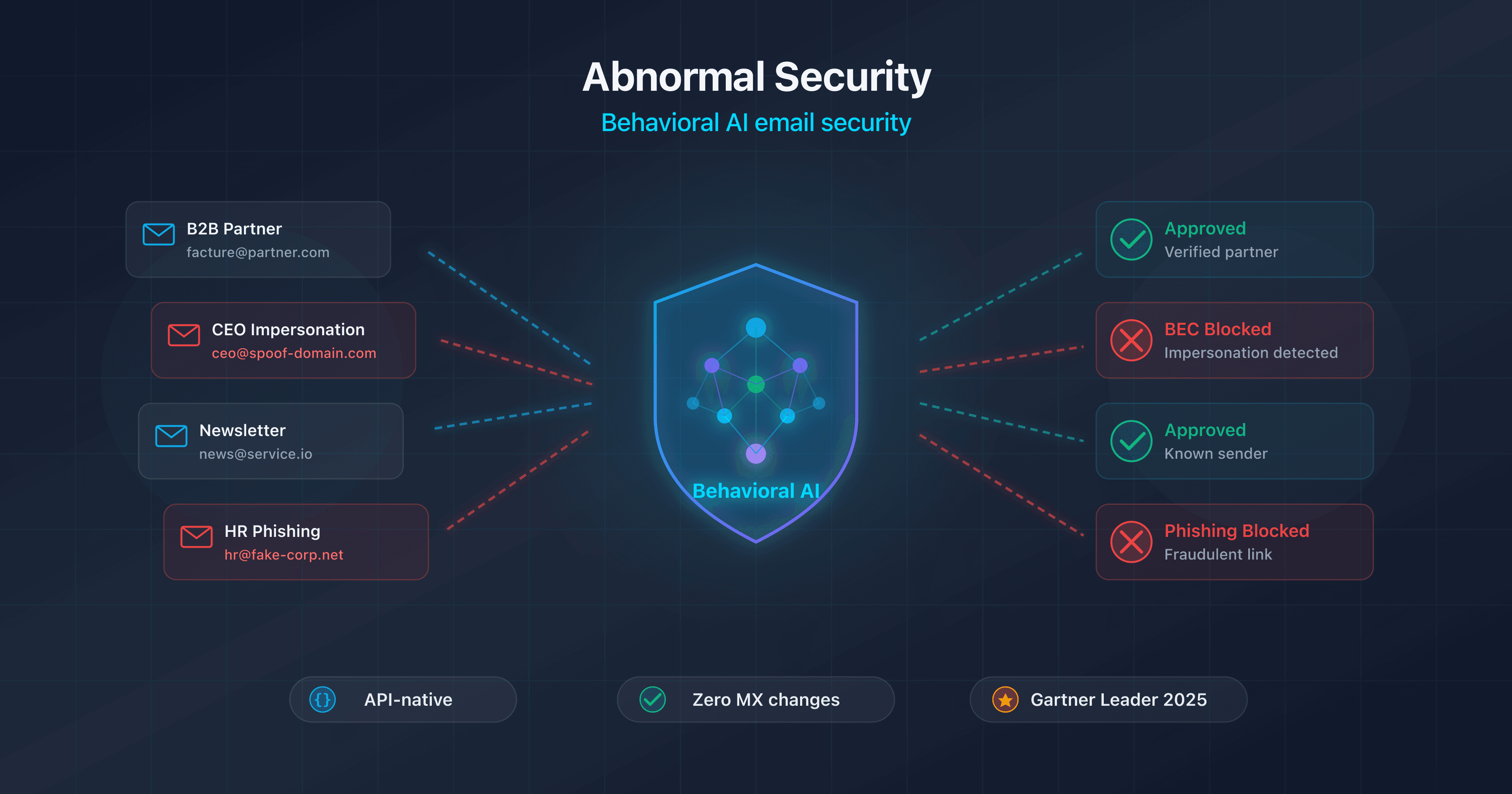
- Abnormal Security is an ICES (Integrated Cloud Email Security) platform that connects via API to Microsoft 365 or Google Workspace. No MX change, no DNS modification. Deployment in 4 clicks, calibration in 14 days.
- Behavioral AI: the Attune 1.0 foundation model (March 2026) simultaneously analyzes identity, behavior, and content to detect BEC, VEC, and Account Takeover attacks that traditional gateways miss. 85% of detections are powered by Attune.
- Abnormal does not replace SPF/DKIM/DMARC. DNS authentication blocks direct spoofing upstream. Abnormal handles threats that pass authentication: compromised accounts, lookalike domains, hacked vendors.
- 65% of Abnormal customers have dropped their third-party SEG in favor of the Microsoft Defender + Abnormal duo, with claimed savings of 42% in licensing costs.
- Limitations to know: no attachment sandboxing, no URL rewriting, post-delivery processing (latency window), no Exchange on-premises support, high pricing ($36 to $80 per user per year).
Every day, more than 3.4 billion phishing emails are sent worldwide. Traditional email gateways (SEGs) effectively block payload-based threats: malicious attachments, phishing links, bulk spam.
But the most costly attacks have no payload and no detectable signature. Business Email Compromise (BEC) attacks are plain-text emails sent from legitimate accounts or lookalike domains, requesting a wire transfer, a bank detail change, or credentials. The FBI estimates cumulative BEC losses at over $55 billion.
This is exactly the problem Abnormal Security claims to solve. Founded in 2018 and valued at $5.1 billion, the platform takes a radically different approach: instead of filtering traffic upstream via MX redirection, Abnormal connects directly to the Microsoft 365 and Google Workspace APIs to analyze every email after delivery, relying on behavioral AI rather than signatures and rules.
At CaptainDNS, we analyze Abnormal through the lens of DNS authentication. While Abnormal does not modify your MX, SPF, or DKIM records, the question of how technical authentication and behavioral detection complement each other is central. This article is the third in our series on enterprise email security solutions, following our guides on Mimecast and Proofpoint (links at the end of the article).
Check your email records
What is Abnormal Security, and why does the behavioral approach change the game?
To understand Abnormal, you first need to understand why traditional gateways fail against BEC.
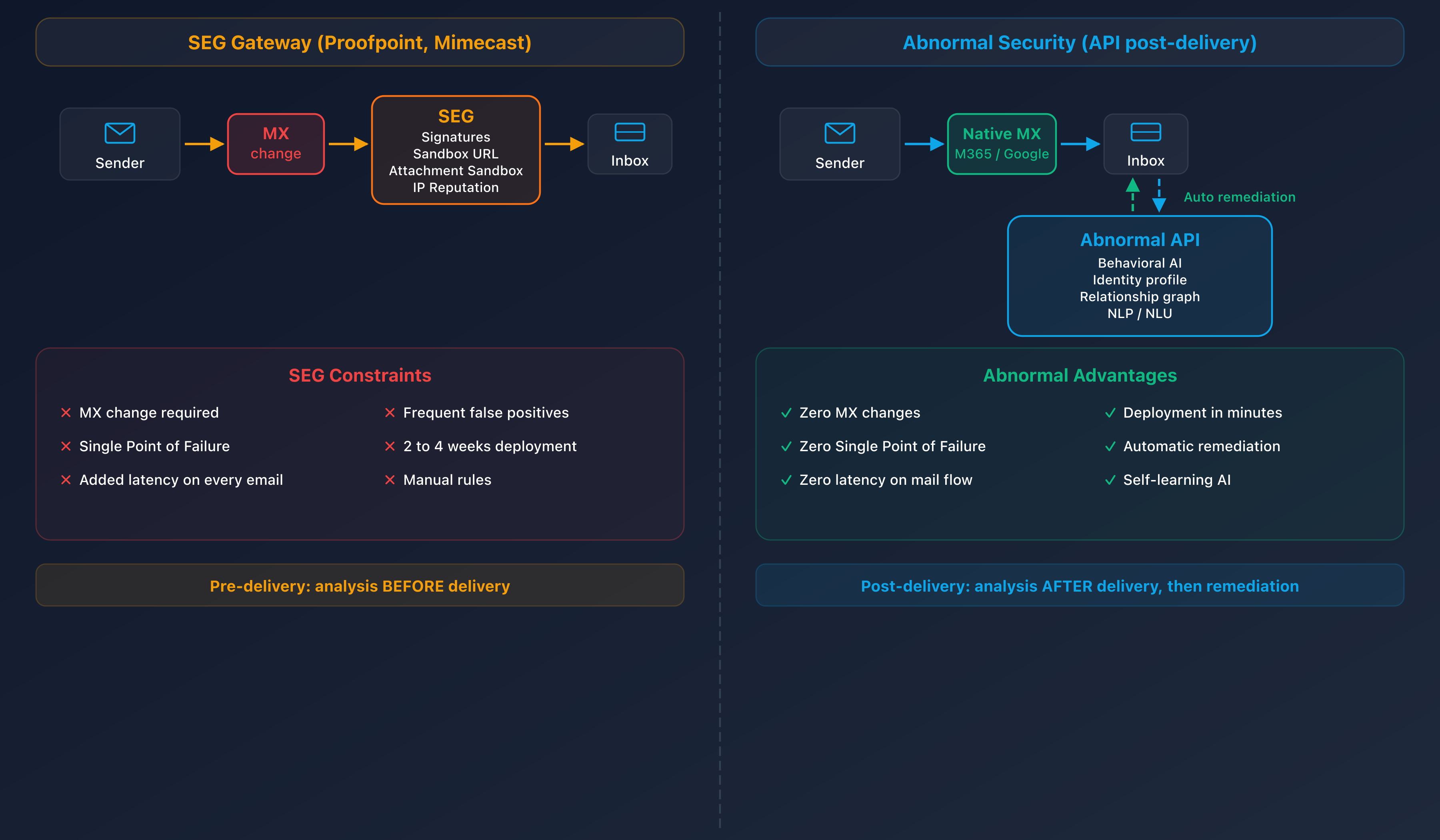
A standard SEG (Proofpoint, Mimecast, Barracuda) works like a checkpoint: it sits in the email flow via MX records, inspects every inbound message, and blocks threats identified through signatures, reputation, sandboxing, or link analysis. This model is effective against emails containing a malicious payload. But a BEC email contains nothing technically malicious: no infected attachment, no phishing link, no malware. It is a plain-text email sent by a human (or a compromised account) requesting a financial action.
Evan Reiser, CEO of Abnormal, describes these attacks as "architecturally impossible" for a SEG to detect. The SEG does not know the internal relationships within your organization, does not know that your CFO never requests wire transfers by email on Sundays, and cannot detect that a regular vendor has suddenly changed bank details. BEC exploits human trust, not technical vulnerabilities.
This structural gap is what motivated the creation of Abnormal in 2018. The platform positions itself as an "AI-native human behavior security platform": instead of analyzing what the email contains, it analyzes who is sending it, to whom, in what context, and whether that behavior is normal.
Abnormal Security: the company at a glance
Abnormal Security was founded in 2018 in San Francisco by Evan Reiser (CEO, former Twitter engineer and founder of Bloomspot) and Sanjay Jeyakumar (CTO). The founding idea: apply financial fraud detection techniques (behavioral profiling, relationship graphs) to email security.
The company has raised a total of $546 million across five funding rounds. The Series D, closed in 2024, brought the valuation to $5.1 billion. Investors include Greylock Partners, Menlo Ventures, Insight Partners, Wellington Management, and CrowdStrike.
By the numbers:
- 3,200+ customers, including over 25% of the Fortune 500 (Maersk, Xerox, Domino's, Mattel, among others)
- ARR exceeding $100 million (August 2023), with rapid growth
- 99% renewal rate, a sign of high customer satisfaction
- 747 employees (2025 data)
In April 2025, the company announced its rebranding as Abnormal AI, reflecting the platform's expansion beyond email security alone. However, the vast majority of searches still use "Abnormal Security."
On the market recognition side:
- Gartner Leader in the Magic Quadrant for Email Security in 2024 and 2025 (positioned furthest right on the Vision axis)
- Forrester Leader in the Wave Email Security Q2 2025 (highest strategy score: 5.0/5 Innovation)
- Gartner Peer Insights: 4.8/5, 99% recommendation rate
- FedRAMP Moderate (2025), certification for the US public sector
- ISO/IEC 42001, AI governance standard
- CNBC Disruptor 50 (2025)
Technical architecture: behavioral AI instead of the gateway
API connection via M365 and Google
Unlike SEGs that redirect email flow through MX records, Abnormal connects directly to the native APIs of email platforms. For Microsoft 365, it is the Graph API. For Google Workspace, it is the Gmail API.
Deployment boils down to an OAuth authorization. Abnormal claims a "4-click" process: the administrator authorizes the application in the M365 or GWS console, and Abnormal gets the permissions needed to read emails, analyze metadata, and delete or move messages identified as malicious.
The technical implications of this model are significant:
- Zero MX change. Your DNS records remain intact. Email flow is not rerouted.
- Zero transport rules. No routing rules to configure in your tenant.
- No single point of failure. If Abnormal goes down, emails continue to arrive normally. The worst-case scenario is a temporary gap in Abnormal protection, not an email flow interruption.
- No added latency. Mail is not relayed through an intermediary server. It arrives directly in the inbox via the normal path.
The tradeoff: Abnormal only sees emails after they are delivered. Detection and remediation happen post-delivery.
The three pillars of behavioral detection
Abnormal's detection engine relies on three simultaneous axes of analysis.
Identity profiling builds a behavioral baseline for every user, every external vendor, and every service interacting with the organization. The system learns typical sending schedules, request types, writing style, frequent recipients, and platforms used. Any significant deviation from this baseline triggers a risk score.
The relationship graph maps communications between all entities: who communicates with whom, how often, on what topics, and with what temporal patterns. An email allegedly from a regular vendor but coming from a never-seen address, or a wire transfer request from a contact who never makes them, generates an alert. The graph covers internal relationships (employee to employee) and external ones (vendors, partners, clients).
NLP/NLU content analysis (Natural Language Processing / Natural Language Understanding) evaluates tone, urgency, atypical financial requests, and psychological manipulation techniques in the message. An email whose technical content is legitimate but whose tone exerts unusual time pressure ("wire transfer needed before noon") will be flagged.
These three axes are correlated in real time. An email that shows an anomaly on a single axis may be tolerated. An email that deviates on all three axes simultaneously will be classified as a threat with high confidence.
Attune 1.0: the behavioral foundation model (March 2026)
In March 2026, Abnormal unveiled Attune 1.0, described as the first foundation model specialized in behavioral email threat detection.
Attune is a unified transformer architecture that jointly processes identity, behavior, and content signals. Unlike the previous approach (specialized models per threat type, combined in a pipeline), Attune merges all signals into a single representation space. The analogy: moving from multiple specialists consulting sequentially to a single expert who masters all dimensions.
The announced numbers:
- Trained on over one billion behavioral signals derived from customer environments
- Powers 85% of detections on the platform
- Detects more than 150,000 attack campaigns per week
- 50% improvement in accuracy over previous models
The practical impact: Attune detects attack campaigns that would not have been identified by specialized models, particularly "low and slow" attacks where the attacker sends a low volume of highly targeted emails with no campaign pattern identifiable by traditional approaches.
Post-delivery processing: how it works in practice
Abnormal's processing cycle unfolds in four stages.
First, the email is delivered to the recipient's inbox through the normal path (via the domain's MX, whether Microsoft 365, Google Workspace, or an upstream SEG). Abnormal does not intervene in this delivery.
Second, the Graph or Gmail API notifies Abnormal of the message's arrival. Abnormal retrieves the content, headers, metadata, and attachments.
Third, the analysis engine evaluates the message in a few seconds. The three pillars (identity, behavior, content) are engaged simultaneously via Attune 1.0.
Fourth, if the message is identified as malicious, Abnormal executes automatic remediation: moving to a quarantine folder, deletion, or flagging. The user may never see the message if remediation occurs quickly enough.
The latency window is the critical point of this model. Between delivery and remediation, a few seconds to a few tens of seconds elapse. During this window, the email is technically accessible in the inbox. For most BEC attacks (which aim to obtain a human action, not an immediate click), this latency is negligible. For emails containing an urgent phishing link, it is less so.
Replacing the third-party SEG: the native + Abnormal duo
Abnormal actively pushes a commercial message: replace your third-party SEG with the combination of Microsoft Defender for Office 365 (or EOP) + Abnormal. The reasoning goes as follows: Defender handles known threats (malware, spam, payload-based phishing) through its native capabilities, while Abnormal handles social engineering threats (BEC, VEC, Account Takeover) that Defender detects less effectively.
The numbers claimed by Abnormal:
- 65% of customers have dropped their third-party SEG (Proofpoint, Mimecast, or other)
- 1,300+ Proofpoint customers migrated to Abnormal over a 12-month period
- 42% savings in licensing costs compared to maintaining a third-party SEG
This model is compelling on paper. But it assumes that Defender is sufficient for payload-based threats, which depends on your environment, your industry, and your risk tolerance. We will detail the arguments for and against in the section dedicated to the gateway vs API debate.
Abnormal and DNS authentication: two complementary layers
What SPF, DKIM, and DMARC protect vs what Abnormal protects
SPF, DKIM, and DMARC form the technical authentication layer of email. Their role: verify that the email comes from an authorized server (SPF), that the content has not been altered in transit (DKIM), and that the sender's domain is aligned with these checks (DMARC). With a DMARC policy set to p=reject, an attacker cannot send an email pretending to be @captaindns.com from an unauthorized server: the message will be rejected before it even reaches the inbox.
Abnormal operates on an entirely different layer. The platform does not verify the technical authenticity of the email. It evaluates whether the sender's behavior, the message content, and the communication context are consistent with what the organization expects.
Neither alone is enough. DMARC blocks direct spoofing but lets through emails sent from compromised accounts or lookalike domains. Abnormal detects behavioral attacks but does not prevent an attacker from spoofing your domain if your DMARC is set to p=none.
When DMARC is not enough
Four scenarios illustrate the limitations of DNS authentication against modern attacks.
Compromised accounts. An attacker takes over an employee's email account (through credential phishing, malware, or credential stuffing). Emails sent from this account pass SPF, DKIM, and DMARC without issue: they come from the legitimate server, with the legitimate signature. DMARC is designed to authenticate the domain, not to detect that an account has been compromised.
Lookalike domains. The attacker registers a visually similar domain (for example captaindnss.com or captaindns-billing.com) and correctly configures SPF, DKIM, and DMARC for that domain. Emails pass all authentication checks. Protection then relies on the recipient's vigilance or on behavioral analysis that detects this domain has never communicated with the organization.
Vendor exceptions in DMARC policies. Some organizations maintain permissive DMARC policies (p=none or p=quarantine with a low percentage) to avoid blocking legitimate emails from poorly configured third-party vendors. These exceptions create exploitable gaps.
VEC (Vendor Email Compromise). The attacker compromises the email account of a real vendor. The email comes from the vendor's actual domain, passes all DNS authentication checks, and references real ongoing transactions. Only behavioral analysis can detect that the request to change bank details is abnormal.
Why strengthening SPF/DKIM/DMARC remains essential even with Abnormal
Deploying Abnormal in no way exempts you from maintaining robust DNS authentication. Four reasons.
First line of defense. SPF/DKIM/DMARC block direct spoofing upstream of the email flow, before Abnormal even comes into play. A DMARC policy set to p=reject eliminates a significant volume of fraudulent emails, reducing the attack surface that the behavioral layer must analyze.
Noise reduction. DMARC at p=reject drastically reduces the volume of attacks Abnormal needs to analyze. Less noise means fewer false positives and more effective behavioral detection on truly sophisticated threats.
Outbound traffic is not covered. Abnormal does not handle outbound email authentication. If your organization sends emails, only SPF, DKIM, and DMARC protect your recipients against spoofing of your domain.
Abnormal + Valimail partnership. Abnormal has formalized a partnership with Valimail to help its customers with DMARC enforcement. This is a clear signal: even Abnormal considers DMARC at p=reject a prerequisite, not an option.
The Abnormal product ecosystem
The Abnormal platform has expanded beyond malicious email detection. Here are the current modules.
Inbound Email Security is the flagship product. It covers the full spectrum of inbound email threats: phishing, BEC, VEC, malware, ransomware via email. This is the module that uses Attune 1.0 for behavioral detection.
Email Account Takeover Protection monitors signs of email account compromise within the organization. The module establishes connection baselines (geolocation, device, browser, time, frequency) and detects anomalies: login from an unusual country, sudden change to forwarding rules, atypical VPN access. Remediation is automatic: account lockout and administrator notification.
AI Security Mailbox replaces the traditional shared mailbox for reporting phishing with an autonomous triage system operating 24/7. When an employee reports a suspicious email, the AI analyzes it immediately, categorizes the threat, and responds to the employee with a verdict. Confirmed threats trigger automatic remediation across all mailboxes that received the same message.
AI Phishing Coach generates phishing simulations based on threats actually blocked in the customer's environment. Instead of generic simulations, each test campaign reproduces the characteristics of attacks that actually target the organization.
Security Posture Management audits the Microsoft 365 environment configuration: excessive permissions, suspicious forwarding rules, risky OAuth applications, security policy misconfigurations. The module identifies exploitable configuration flaws.
AI Data Analyst allows security teams to query their security posture in natural language. Instead of building complex queries in a SIEM, the analyst asks a question ("what are the 10 most targeted users this month?") and gets a structured response.
Multi-platform extension. Abnormal extends its coverage beyond email to Slack, Microsoft Teams, Zoom, and integrates with platforms like Okta (identity), CrowdStrike (endpoint), and Workday (HR). The goal: apply the same behavioral detection to collaboration channels.

Abnormal Security advantages
Abnormal stands out through a combination of strengths that justify its leader positioning with both Gartner and Forrester.
- Unmatched BEC/VEC detection. Where SEGs structurally fail against emails with no payload, the behavioral approach identifies anomalies in identity, context, and content. Vendor Email Compromise attacks, originating from legitimate accounts, are Abnormal's sweet spot.
- Deployment in minutes. No MX change, no DNS modification, no transport rules. OAuth integration in "4 clicks" reduces the deployment project from several weeks (for a SEG) to a few minutes. Behavioral calibration takes 14 days, but basic protection is active immediately.
- Near-zero maintenance. Abnormal operates in "set and forget" mode. No manual rules to maintain, no allow lists to manage. Behavioral models automatically adapt to organizational changes (new employees, new vendors, process changes).
- 95% reduction in SOC triage time. The AI Security Mailbox and automatic remediation eliminate the majority of manual work triaging email reports.
- Attune 1.0: enhanced detection power. Over 150,000 attack campaigns detected per week and a 50% improvement in accuracy over previous models.
- Unanimous market recognition. Gartner Leader two consecutive years (2024 and 2025), Forrester Leader (Q2 2025), Gartner Peer Insights 4.8/5 with 99% recommendation rate.
- Advanced certifications. FedRAMP Moderate for the US public sector, ISO/IEC 42001 for AI governance.
- Extension beyond email. Coverage of Slack, Teams, Zoom, and integration with Okta, CrowdStrike, and Workday position Abnormal as a multi-channel behavioral security platform.
Limitations and drawbacks to know
No solution is without tradeoffs. Here are the concrete limitations to evaluate before choosing Abnormal.
- No attachment sandboxing. Abnormal does not execute file attachments in an isolated environment. Attachments are analyzed by AI models, but there is no sandbox detonation. For zero-day threats carried by malicious documents, this gap is a real limitation.
- No URL rewriting. Abnormal does not replace links in emails with verification URLs (unlike Proofpoint URL Defense or Mimecast URL Protect). No "time-of-click" protection: if a link becomes malicious after analysis, the user is not protected at click time.
- Post-delivery processing. The latency window between delivery and remediation is the fundamental tradeoff of the API model. For a few seconds to a few tens of seconds, the email is visible in the inbox.
- No Exchange on-premises support. Abnormal requires Microsoft 365 or Google Workspace. This is a dealbreaker for certain industries (finance, defense, healthcare) where cloud migration is not yet complete.
- No email archiving, no continuity, no DLP. Abnormal is a detection solution, not an email management platform. If you are replacing a SEG that offered these features, you will need alternative solutions.
- Limited alert customization. Alerts are binary: enabled or disabled. The level of granularity is reported as limited by some users.
- Reports could be better. Dashboards and reports lack depth and customization compared to mature SEGs like Proofpoint or Mimecast.
- No outbound traffic monitoring. Outbound emails are not analyzed. Shadow IT, data leaks via email, and compromised accounts sending spam are not detected on the outbound flow.
- High pricing. $36 to $80 per user per year, depending on modules. Multi-year contracts (2 to 3 years) allow discounts of 15% to 30%, but the cost remains significant on top of an existing Defender license.
- Total dependence on Microsoft and Google APIs. If Microsoft or Google modifies the permissions, quotas, or structure of these APIs, Abnormal can be directly impacted. This is a long-term structural risk.
Gateway vs API: the debate dividing email security
The email security market is split by a fundamental debate between two architectures. Here is a structured comparison.
| Criterion | SEG (pre-delivery) | ICES API (post-delivery) |
|---|---|---|
| Position in the flow | Upstream (MX redirected) | Downstream (post-delivery API) |
| DNS change | Yes (MX, SPF, sometimes DKIM) | No |
| Deployment | Days to weeks | Minutes to hours |
| Added latency | Yes (transit via the SEG) | No |
| BEC/VEC detection | Limited (no behavioral context) | Strong (profiling, graph, NLP) |
| Sandboxing / URL rewrite | Yes | No (for Abnormal) |
| Single point of failure | Yes (SEG outage = blocked emails) | No |
| Archiving / continuity | Often included | No |
Arguments for the gateway. The SEG blocks threats before they reach the inbox. Attachment sandboxing, URL rewriting with click-time verification, and built-in archiving are capabilities that the API model does not offer. For organizations with high volumes of payload-based threats (malware, ransomware via email), the SEG remains the most robust line of defense.
Arguments for the API. Deployment is trivial, maintenance is minimal, and BEC/VEC detection is structurally superior. No single point of failure, no added latency to email flow, no complex DNS configuration to maintain. For organizations whose top threat is BEC and who already have Defender for payload-based threats, the API model is the logical choice.
The emerging hybrid model. The market is converging toward a model where Microsoft Defender (or EOP) provides baseline protection (spam, malware, known phishing) and an ICES solution like Abnormal adds the behavioral layer. This is the "displace your SEG" approach promoted by Abnormal, and the migration numbers (65% of customers having dropped their third-party SEG) suggest this model is gaining traction.
Risks of going all-API. The post-delivery latency window remains a tradeoff. Dependence on third-party APIs (Microsoft Graph, Gmail API) introduces a platform risk. And the lack of sandboxing and URL rewriting leaves coverage gaps that Defender alone does not always fill.
Comparison: Abnormal vs Proofpoint, Mimecast, and Microsoft Defender
| Criterion | Abnormal Security | Proofpoint | Mimecast | Defender M365 |
|---|---|---|---|---|
| Type | ICES (API) | SEG (gateway) | SEG (gateway + API) | Native M365 |
| AI detection | Attune 1.0 (behavioral) | Nexus AI (6 components) | CyberGraph 2.0 + ML | Built-in ML |
| Deployment | API OAuth, 4 clicks | MX redirect, weeks | MX redirect + API mode | Native, no change |
| DMARC | No (Valimail partnership) | EFD managed DMARC + Hosted SPF | Built-in DMARC Analyzer | No |
| Archiving | No | No (separate license) | Native (up to 99 years) | No (separate Purview) |
| Price | $36-80/user/yr | ~$87K/yr median (Vendr) | $3.50-8/user/mo | < EUR 2/user/mo |
| Best for | BEC/VEC, overloaded SOC, M365/GWS | Fortune 500, threat intel, compliance | Mid-market, archiving, all-in-one | Limited budget, full M365 |
Proofpoint: the threat intelligence benchmark
Proofpoint dominates the enterprise segment with 87 of the Fortune 100 as clients. Its Nexus AI engine leverages 6 AI components and a trillion data points to fuel detection. The TAP (Targeted Attack Protection) suite includes URL Defense, Attachment Defense, and Predictive Sandboxing, three capabilities absent from Abnormal.
Proofpoint also offers EFD (Email Fraud Defense) for DMARC management and Hosted SPF, managed DNS authentication services. This is a significant advantage for large organizations with complex SPF records.
The weaknesses: high administrative complexity, premium pricing ($87,000 per year median according to Vendr), and the 2024 EchoSpoofing incident where 14 million fraudulent emails per day were routed through Proofpoint servers for six months by exploiting permissive relay configurations.
For a complete analysis, see our dedicated Proofpoint guide (link at the end of the article).
Mimecast: the all-in-one for the mid-market
Mimecast stands out for the functional richness of its platform: native archiving (up to 99 years of retention), email continuity during outages, built-in DMARC Analyzer, and the TTP suite (URL Protect, Attachment Protect, Impersonation Protect). The CyberGraph 2.0 module adds a behavioral analysis layer.
In 2026, Mimecast launched a full API deployment model for M365, narrowing the gap with ICES solutions. The platform targets the mid-market (500 to 5,000 users) with the best feature-to-price ratio in the segment.
The 2021 supply chain incident (compromise as part of the SolarWinds/NOBELIUM attack) was resolved, but it remains a reference point in risk assessments.
See our complete Mimecast guide (link at the end of the article).
The native choice for M365 environments
Defender is Microsoft 365's native email security solution. No MX change, no DNS configuration, activation in the existing tenant. Cost is under EUR 2 per user per month as part of M365 E5 licenses or as an add-on.
Independent detection scores (9.1/10) are solid for payload-based threats (malware, phishing with links). The gaps lie in BEC detection (weaker than specialized solutions), the lack of Proofpoint-level proprietary threat intelligence, and no native email archiving (Microsoft Purview is a separate product).
This is the foundation on which Abnormal recommends building: Defender for known threats, Abnormal for behavioral threats.
When to choose Abnormal Security
Abnormal is a good fit if your organization uses Microsoft 365 or Google Workspace, if BEC/VEC is your top threat (industries with high financial transactions: finance, real estate, supply chain), if your SOC is overwhelmed by email report triage, if you want a fast deployment with no infrastructure changes, and if you have the budget to complement Defender with a specialized layer.
Abnormal is not the right fit if you use Exchange on-premises, if you need built-in email archiving, DLP, or email continuity, if your budget is limited and Defender alone must suffice, or if you need attachment sandboxing and URL rewriting (predominantly payload-based threats).
Step-by-step deployment guide
Step 1: audit your current DNS posture. Before any deployment, check the status of your SPF, DKIM, and DMARC records. Use the CaptainDNS DKIM Record Check tool to validate your signatures, and the SPF and DMARC tools via the CTA above. A clean baseline is essential before adding a security layer.
Step 2: strengthen DMARC to p=reject. If your DMARC policy is at p=none or p=quarantine, plan the migration to p=reject before or in parallel with your Abnormal deployment. This is a prerequisite recommended by Abnormal itself. Start by analyzing aggregate DMARC reports to identify legitimate senders not covered by your SPF.
Step 3: connect Abnormal via OAuth. In the Microsoft 365 or Google Workspace admin console, authorize the Abnormal application and grant the necessary permissions (email reading, remediation actions). The process takes a few minutes.
Step 4: calibration period. For 14 days, Abnormal builds your organization's behavioral baseline. It learns communication patterns, entity relationships, and sending habits. During this phase, the solution operates in observation mode: it detects but does not automatically remediate.
Step 5: enable automatic remediation and additional modules. After calibration, enable automatic remediation (moving or deleting emails identified as malicious). Then deploy additional modules as needed: Account Takeover Protection, AI Security Mailbox, AI Phishing Coach.
Verify that your email security works
Deploying Abnormal does not exempt you from continuously verifying the entire email security chain.
Test SPF/DKIM/DMARC with CaptainDNS. Regularly check that your authentication records are valid, that SPF does not exceed the 10-lookup limit, that DKIM keys are published and active, and that your DMARC policy is at p=reject with reporting enabled.
Check email headers. Inspect the Authentication-Results and ARC headers of received emails to confirm that SPF, DKIM, and DMARC pass correctly. ARC headers are particularly important if a SEG or intermediary relay is still present in your flow.
Monitor the Abnormal dashboard. Track detection counts, false positive rates, coverage by threat type, and time-based trends. An abnormally high false positive rate may indicate a calibration issue.
Posture audit via Security Posture Management. If you use Abnormal's SPM module, leverage it to identify M365 configuration errors: excessive OAuth permissions, suspicious forwarding rules, accounts without MFA.
Common pitfalls to avoid
Removing the SEG without strengthening DMARC first. If you are migrating from a SEG to the Defender + Abnormal model, make sure your DMARC is at p=reject before cutting the SEG. Without this protection, direct spoofing volume will increase, and Abnormal is not designed to block these threats.
Ignoring the post-delivery latency window. Post-delivery remediation is fast, but not instantaneous. For emails containing urgent phishing links, this window is a real risk. Educate users not to immediately click on links in unexpected emails.
Not auditing the OAuth permissions granted. The Abnormal integration requires extensive permissions on your M365 or GWS tenant. Document these permissions precisely, verify they correspond to the minimum necessary, and include them in your periodic security reviews.
Staying at p=none with no DMARC enforcement plan. Abnormal works with any DMARC policy, but a p=none policy lets direct spoofing through, overloading the behavioral detection. Plan a path to p=reject.
Forgetting third-party senders in SPF during migration. If you are replacing a SEG that relayed your outbound emails, the SEG's servers are probably in your SPF record. When removing the SEG, do not forget to update SPF to remove the now-unnecessary include and add any new senders.
Neglecting user training despite AI Phishing Coach. Automation reduces risk but does not eliminate it. The AI Phishing Coach module is a tool, not a substitute for a culture of vigilance. Simulations should be complemented by regular communication about actual blocked threats.
Relying on Abnormal for archiving or compliance. Abnormal does not archive emails and does not provide regulatory compliance features (legal hold, eDiscovery). If you had these features with your SEG, plan for a dedicated solution.
10-step action plan
- Audit your current DNS posture with CaptainDNS (SPF, DKIM, DMARC)
- Evaluate the technical fit: Microsoft 365 or Google Workspace, available budget, BEC as the top priority
- Request a demo and Abnormal POC (free evaluation period)
- Strengthen DMARC to
p=quarantinethenp=rejectusing aggregate report analysis - Connect Abnormal via OAuth (M365 or GWS)
- Observe during the 14-day calibration period (observation mode, no automatic remediation)
- Enable automatic remediation after validating calibration results
- Deploy AI Security Mailbox and AI Phishing Coach to complement coverage
- Evaluate replacing the third-party SEG if relevant (Defender + Abnormal model)
- Schedule monthly reviews: detections, false positives, coverage, DMARC posture
📚 Email gateway guides
This analysis is part of our series on enterprise email security solutions:
- Mimecast Secure Email Gateway: architecture, DNS configuration, comparison, and action plan
- Proofpoint Secure Email Gateway: Nexus AI, TAP, 2024 EchoSpoofing, and DNS configuration
- Abnormal Security (this article): behavioral AI, API deployment, Attune 1.0
- Cisco Secure Email Gateway: CES cloud gateway, Ironport heritage, Gartner 2025 exit and migration roadmap
- Cloudflare Email Service: Routing, Email Service, Security (ex-Area 1), and DMARC Management
FAQ
Can Abnormal Security replace Proofpoint or Mimecast?
Not directly. Abnormal replaces the BEC/VEC detection layer of a SEG, but not the sandboxing, URL rewriting, archiving, or email continuity features. The model recommended by Abnormal is to replace the third-party SEG with Microsoft Defender (payload-based threats) + Abnormal (behavioral threats). 65% of Abnormal customers have followed this model. If you depend on archiving or email continuity from your current SEG, plan alternative solutions before migrating.
How does Abnormal's API deployment work?
Abnormal connects via OAuth to your Microsoft 365 tenant (Graph API) or Google Workspace (Gmail API). The administrator authorizes the application in the admin console and grants read and remediation permissions. The process takes a few minutes. No MX change, no DNS modification, and no transport rules are needed. Behavioral calibration then takes 14 days.
Is Abnormal Security compatible with Exchange on-premises?
No. Abnormal requires Microsoft 365 or Google Workspace. The integration relies on cloud APIs (Graph, Gmail API) that do not exist for Exchange on-premises. If your organization runs a hybrid environment, only cloud-hosted mailboxes will be protected by Abnormal.
How much does Abnormal Security cost?
Pricing ranges from $36 to $80 per user per year, depending on the modules selected and organization size. Multi-year contracts (2 to 3 years) allow discounts of 15% to 30%. Pricing is per user, per year. For a 1,000-user organization, expect between $36,000 and $80,000 per year. Abnormal does not publish an official pricing grid: request a custom quote.
How does Abnormal detect BEC attacks with no payload?
Abnormal uses three simultaneous analysis axes: identity profiling (behavioral baseline for each user and vendor), the relationship graph (mapping of normal communications), and NLP/NLU content analysis (tone, urgency, financial requests). The Attune 1.0 model merges these signals in a unified transformer architecture. A BEC email with no attachment or malicious link will be detected if the sender's behavior, the request context, or the message tone deviates from normal patterns.
Do you need DMARC at p=reject before deploying Abnormal?
It is not a technical prerequisite (Abnormal works regardless of your DMARC policy), but it is strongly recommended. DMARC at p=reject blocks direct spoofing upstream, reducing the volume of threats Abnormal needs to analyze and improving overall accuracy. Abnormal has a partnership with Valimail to help its customers with DMARC enforcement.
Does Abnormal Security analyze attachments?
Abnormal analyzes attachments via its AI models (content extraction, file type analysis, correlation with behavioral context). However, it does not offer sandboxing (executing the file in an isolated environment). Zero-day threats carried by malicious documents that require sandbox detonation are not covered by Abnormal. For this protection, Microsoft Defender or a SEG with sandboxing is needed.
What is the difference between Abnormal and Microsoft Defender?
Defender is Microsoft 365's native email security solution. It excels at detecting payload-based threats (malware, phishing with links, spam) for under EUR 2 per user per month. Abnormal is a third-party solution specializing in behavioral detection of payloadless threats (BEC, VEC, Account Takeover) for $36 to $80 per user per year. The two are complementary: Defender blocks technical threats, Abnormal blocks behavioral threats.
Does Abnormal Security require an MX record change?
No. This is one of the fundamental differences from traditional SEGs. Abnormal connects via API (OAuth) to Microsoft 365 or Google Workspace. Your MX, SPF, DKIM, and DMARC records remain unchanged. Email flow is not rerouted. If Abnormal is unavailable, emails continue to arrive normally.
What is Attune 1.0?
Attune 1.0 is Abnormal's foundation model, announced in March 2026. It is a unified transformer architecture that jointly processes identity, behavior, and content signals in a single pass (instead of specialized models in a pipeline). Trained on over one billion behavioral signals, Attune powers 85% of Abnormal's detections, detects more than 150,000 campaigns per week, and delivers a 50% improvement in accuracy over previous models.
Glossary
-
BEC (Business Email Compromise): a type of email fraud where the attacker impersonates an executive, colleague, or partner to obtain a wire transfer, sensitive data, or access credentials. Global losses exceed $55 billion according to the FBI IC3.
-
VEC (Vendor Email Compromise): a BEC variant where the attacker compromises a real vendor's email account to intercept or redirect payments. Particularly difficult to detect because the email comes from a legitimate, authenticated domain.
-
SEG (Secure Email Gateway): an email security gateway that filters inbound and outbound traffic by sitting in the flow via MX records. Analyzes every message (spam, malware, phishing) before delivery.
-
ICES (Integrated Cloud Email Security): an email security model deployed via API directly into the cloud platform (M365, Google Workspace), with no MX modification. Analysis occurs after delivery with automatic remediation.
-
API-native: describes a solution designed from the ground up to operate via cloud platform APIs, as opposed to SEGs that adapted to the API model after being designed for the gateway model.
-
MX (Mail Exchanger): a DNS record that indicates the servers responsible for receiving emails for a domain. SEGs redirect MX records to their own servers to intercept traffic.
-
SPF (Sender Policy Framework): an email authentication protocol that lists the servers authorized to send emails for a domain. A TXT record in DNS, limited to 10 lookups.
-
DKIM (DomainKeys Identified Mail): a protocol that cryptographically signs emails. The public key is published in DNS to allow verification of the message's integrity and origin.
-
DMARC (Domain-based Message Authentication, Reporting and Conformance): a protocol that verifies alignment between the From domain and the domains authenticated by SPF and DKIM. Defines the policy on failure (none, quarantine, reject).
-
ARC (Authenticated Received Chain): a protocol that preserves email authentication results across intermediary relays. Useful when a SEG or mailing list breaks the original DKIM signature.
-
Attune: Abnormal Security's behavioral foundation model (version 1.0, March 2026). A unified transformer architecture jointly processing identity, behavior, and content.
-
Behavioral AI: a detection approach that analyzes normal behavior patterns to identify deviations, as opposed to detection by signatures or static rules.
-
Account Takeover: the compromise of a legitimate user account by an attacker, enabling the sending of authenticated emails from that account. Undetectable by SPF/DKIM/DMARC.
-
SOC (Security Operations Center): a security operations center that monitors, detects, analyzes, and responds to cybersecurity incidents. Abnormal claims a 95% reduction in SOC triage time.
-
FedRAMP (Federal Risk and Authorization Management Program): a security certification program for cloud services used by the US federal government. FedRAMP Moderate is the level required for sensitive unclassified data.


