Cisco Secure Email Cloud Gateway (CES): SaaS architecture, iphmx.com DNS and ESA migration
By CaptainDNS
Published on April 17, 2026

- ☁️ Cisco Secure Email Cloud Gateway (CES) is the default option for every new Cisco deployment in 2026. SaaS operated by Cisco, MX records redirected to
iphmx.com(NA, EU, APJ regions), shared AsyncOS engine and Talos threat intelligence. Cisco has been actively pushing its ESA customers toward CES since 2020-2021. - 🏛️ ESA (formerly Ironport, on-premise appliance) is now in legacy mode. Still relevant for specific cases (air-gap, strict sovereignty, installed base to amortize), but Cisco no longer markets new appliance deployments.
- 🔌 ETD (Email Threat Defense) is the API-based post-delivery complement on Microsoft 365, Cisco's answer to Abnormal Security. OAuth deployment in minutes, no MX changes, often stacked on CES or on Defender.
- 📉 Removed from the Gartner Magic Quadrant Email Security published December 16, 2024, and still absent in 2025. A strong strategic signal facing the Leaders Proofpoint, Mimecast, Microsoft, Abnormal and KnowBe4.
- 🚨 CVE-2025-20393 (CVSS 10.0): unauthenticated RCE zero-day on AsyncOS Spam Quarantine (both CES and ESA are affected, same OS), actively exploited by the China-linked UAT-9686 actor since late November 2025. Added to the CISA KEV catalog with a December 24, 2025 deadline.
- ✅ When to choose CES: significant Cisco footprint (Secure Firewall, Secure Endpoint, Umbrella), intent to consolidate on a Cisco-operated SaaS, M365 migration with regional residency constraints. Otherwise, Proofpoint, Mimecast or the Defender plus Abnormal combination often remain more relevant.
In 2026, Cisco Secure Email has become first and foremost a SaaS. The Cloud Gateway (CES) is the option Cisco has been pushing for every new customer since 2020-2021, and the majority of mid-market or enterprise renewals today involve moving off the historical ESA appliances to switch to the iphmx.com hosts. Email Security Appliances remain active at many legacy customers, but the product roadmap, commercial messaging and integration efforts (XDR, Talos, ETD) are all geared toward the cloud offering.
That repositioning also shows up in the market numbers. According to Datanyze, 12,160 organizations still use Cisco Secure Email worldwide, for a segment share of 0.06% against the 87 of the Fortune 100 claimed by Proofpoint. In the same year that Cisco Talos reports 600 billion emails analyzed per day, Gartner published its December 16, 2024 Magic Quadrant Email Security Platforms without listing Cisco, a strategic signal of a declining trajectory that Proofpoint explicitly picks up in its marketing communications.
The story, however, is that of a pioneer. Ironport was founded in 2000 in San Bruno, California. Its white anti-spam appliances equipped most large enterprises during the 2000s. On January 4, 2007, Cisco announced its acquisition for 830 million dollars, a deal that closed in fiscal Q3 2007. On November 26, 2012, Ironport officially moved onto the Cisco pricelist, marking the end of a brand and the start of a long consolidation phase inside the Cisco Secure portfolio, followed by progressive migration of appliances to the CES SaaS.
This guide covers everything an IT administrator or CISO needs to know in 2026, with CES as the backbone: the detailed Cloud Gateway technical architecture (onboarding, iphmx.com regions, shared or dedicated tenants, M365 and Google Workspace integration), full DNS configuration (MX, SPF, DKIM, DMARC), residual ESA cases, the ETD complement, the Gartner MQ exit, the CVE-2025-20393 zero-day that affects AsyncOS and therefore both CES and ESA, a comparison against Mimecast, Proofpoint, Microsoft Defender and Abnormal Security, and a five-step CES deployment plan including the ESA-to-CES migration variant.
Whether you are preparing a CES rollout on an M365 scope, still operating an ESA base that needs migrating, or evaluating a move to an alternative, you will find here the factual elements to decide without bias.
Check your email records
📌 The shift to Cisco Secure Email Cloud Gateway
Cisco Secure Email is Cisco's email security gateway, the direct heir to the Ironport product acquired in 2007 for 830 million dollars. In 2026, the offering breaks down into three products, but their strategic weight differs sharply: Cisco Secure Email Cloud Gateway (CES) is the primary SaaS, pushed as the default option for every new deployment; Cisco Secure Email Gateway (ESA, on-premise appliance) has become a legacy option reserved for residual cases; Cisco Secure Email Threat Defense (ETD) is a modern API complement for Microsoft 365. Understanding this hierarchy is essential to evaluate the offering in 2026 and avoid choices misaligned with Cisco's product strategy.
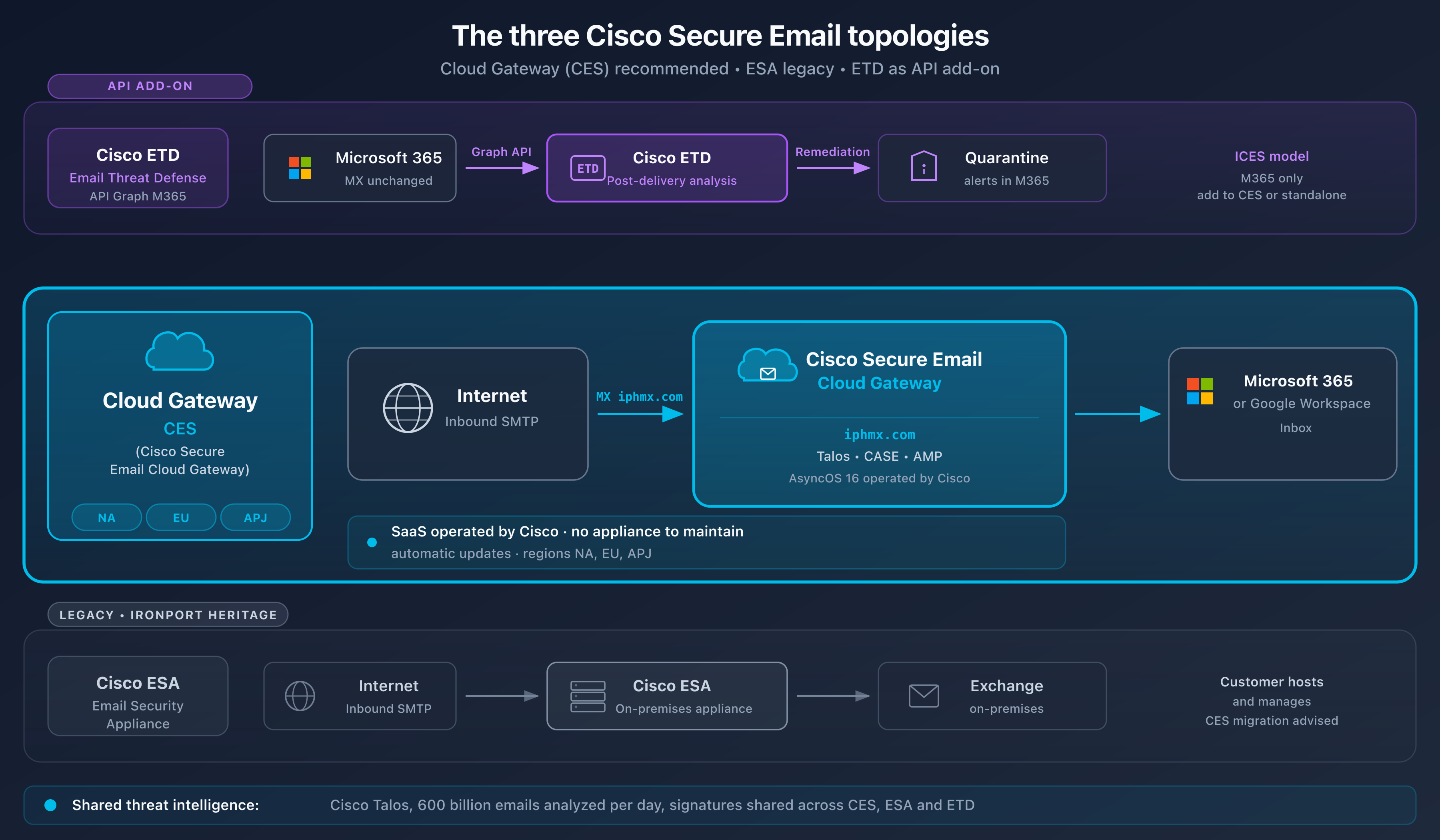
In this diagram, CES is shown as the primary topology (default option for new SaaS deployments with MX redirection to iphmx.com), while the on-premise ESA remains documented for legacy deployments or sovereignty cases, and ETD is presented as a complementary API layer.
From the Ironport appliance to ESA and then the cloud: 2000-2021 timeline
Ironport Systems was founded in 2000 in San Bruno, California, by Scott Banister and Scott Weiss. The company first made its name in the IP reputation market with SenderBase, then in the anti-spam appliance segment by selling dedicated inbound SMTP filtering equipment to large accounts. The C-Series appliances (Ironport C-Series) became benchmarks in the server rooms of banks, government agencies and telco operators in the mid-2000s.
On January 4, 2007, Cisco announced the Ironport acquisition for 830 million dollars in cash and stock. The deal closed in Cisco's fiscal Q3 2007. The stated goal: integrate Ironport's email and web security into the Cisco Security portfolio, alongside PIX firewalls and Cisco IDS. For five more years, the Ironport brand was kept, with appliances still labeled Ironport sold under Cisco commercial references.
On November 26, 2012, Cisco officially completed the migration of Ironport products onto its pricelist, with pure Cisco references. The Ironport brand progressively disappeared from commercial materials, even though the name is still used by long-time administrators and still appears in DNS paths (iphmx.com for Ironport Hosted MX, iphmx being the memory-friendly contraction of that lineage, kept by today's CES SaaS).
At the same time, Cisco launched Cisco Cloud Email Security (CES) to carry the Ironport offering into a SaaS model operated out of its own datacenters. CES adopted the iphmx.com MX hosts and reused the appliance AsyncOS engine, easing the technical migration of existing ESAs to the Cisco cloud.
The 2021 Cisco Secure rebrand and the cloud push
In 2021, Cisco carried out a global overhaul of its security brand under the Cisco Secure umbrella. Security products were renamed for consistency: Cloud Email Security became Cisco Secure Email Cloud Gateway and was from then on positioned as the recommended option for every new customer; Email Security Appliance became Cisco Secure Email Gateway (ESA) and slipped into a legacy stance; AMP for Endpoints became Cisco Secure Endpoint, Umbrella kept its name but joined the Cisco Secure family. That marketing refresh accompanied the technical consolidation around the SecureX platform, which would disappear three years later in favor of Cisco XDR.
For the email administrator, this rebrand did not change the technical reality: AsyncOS remains the shared operating system for CES and ESAs, MX records stay hosted on iphmx.com, DKIM profiles are still configured in the same console. But the commercial messaging aligned on "Cisco Secure Email" across the board, with CES as the SaaS backbone, and the term Ironport disappeared from Cisco's official vocabulary.
In practice, Cisco Account Manager teams push CES for every new deployment and propose CES as the replacement during ESA renewals. An administrator arriving in 2026 on a greenfield Cisco Secure Email project will work almost exclusively on CES and will treat ESA as a fallback option or a legacy footprint to document.
The three products in 2026, with CES as the backbone
In 2026, Cisco sells three distinct products under the Cisco Secure Email brand. Their strategic hierarchy is not neutral and drives architecture decisions:
- Cisco Secure Email Cloud Gateway (CES): primary option, the backbone of this article. SaaS operated by Cisco in its own regional datacenters, shared AsyncOS engine. The customer redirects its MX records to
iphmx.comhosts matching its region (NA, EU, APJ), Cisco filters the traffic, then relays to the actual email server (Microsoft 365, Google Workspace, on-premise Exchange). Onboarding is driven through the Cisco portal, with no infrastructure to administer on the customer side. This is the default path for every new Cisco Secure Email project. - Cisco Secure Email Gateway (ESA, legacy): physical on-premise appliance (C600, C400, etc. references) or virtual (vESA on VMware, AWS, Azure, GCP), a direct heir of Ironport C-Series. The customer hosts and administers the appliances itself. Now treated as legacy by Cisco: relevant only for very specific cases (strict sovereignty, air-gap environment, installed base to amortize). For a new deployment without a hard regulatory constraint, Cisco systematically steers toward CES.
- Cisco Secure Email Threat Defense (ETD): Microsoft 365 post-delivery API, modern complement. No MX changes. Cisco connects via Microsoft Graph API, reads messages after delivery in mailboxes, and can automatically remediate identified threats. Cisco's response to the ICES model popularized by Abnormal Security. Only works with Microsoft 365, not with Google Workspace or on-premise Exchange. Often stacked on CES to double detection, or on Microsoft Defender for customers who do not want a frontal gateway.
The three products share the Talos threat intelligence and can coexist, but the center of gravity has shifted to CES. A typical 2026 profile: CES for inbound flow, ETD as an API layer on the most targeted M365 tenants, and possibly one or two residual ESAs on isolated sites pending decommissioning.
🏢 Cisco and email security: the company in brief
Cisco Systems, Inc. was founded in 1984 in San Jose by Leonard Bosack, Sandy Lerner and Richard Troiano. The company built its empire on network routers and switches before diversifying. In 2026, it employs roughly 95,000 people for annual revenue close to 55 billion dollars, of which about 4 billion for the security segment.
The security portfolio has been structured under the Cisco Secure umbrella since 2021 and covers dozens of products: Secure Firewall (formerly Firepower), Secure Endpoint (formerly AMP), Umbrella (2015 OpenDNS acquisition), Duo (MFA, 2018 acquisition), Secure Email (Ironport), Cisco XDR (2024), and since 2024 Splunk after a record 28 billion dollar acquisition. The integration of Splunk with Secure Email remains partial in 2026.
At the heart of Cisco's security, Cisco Talos Intelligence Group claims more than 500 extended contributors and analyzes 600 billion emails per day, feeding the signatures and behavioral models of CES, ESA and ETD. Talos collaborates with law enforcement, as in the CVE-2025-20393 case detailed further below.
On adoption, Datanyze estimates the Cisco Email Security base at 12,160 organizations and 0.06% email market share; Enlyft reports 0.11% on the broader network security segment. Proofpoint dominates with 87 of the Fortune 100 and 24% share according to Frost Radar 2025. Cisco Email Security customers are dominated by the United States (~58%), France (~8%) and India (~7%), a reflection of the legacy Ironport base rather than of recent momentum. This marginal email positioning contrasts with Cisco's dominance in enterprise networking: the consolidation argument remains valid for already Cisco-centric environments, but the question of choosing a marginal vendor is legitimate for a prospect with no prior footprint.
⚙️ Technical architecture: CES as the backbone, ESA as legacy
Cisco Secure Email runs on three complementary architectures sharing the AsyncOS engine and Talos threat intelligence: CES (SaaS gateway operated by Cisco), ESA (legacy on-premise appliance) and ETD (post-delivery Microsoft 365 API). How does Cisco Secure Email inspect a message in 2026, and how does each product differ technically? The answer reads in three parts: CES as the SaaS backbone for gateway flow, ESA as a legacy option for specific on-premise cases, and ETD as a complementary API layer on Microsoft 365. All share the AsyncOS engine and Talos threat intelligence, but their operational posture diverges sharply.
Cisco Secure Email Cloud Gateway (CES): the default SaaS
CES is the SaaS operated by Cisco in its own regional datacenters. It is the option Cisco pushes for every new deployment in 2026, and the architecture an administrator should know first.
Inbound flow on the network side:
- A sender sends an email to
contact@captaindns.com - The sending server queries DNS to find the domain's MX records
- DNS returns hosts of the form
mx1.<tenant>.iphmx.com(NA region) ormx1.<tenant>.eu.iphmx.comandmx1.<tenant>.apj.iphmx.comdepending on regional allocation - The matching CES datacenter receives the message and applies the AsyncOS analysis chain (CASE, AMP, URL filtering, Content filters, DMARC verifier)
- If the message is accepted, CES relays it to the customer's actual email server: Microsoft 365, Google Workspace or on-premise Exchange depending on the SMTP Routes configuration
- If the message is malicious, it is rejected, quarantined or tagged according to the policies set by the administrator in AsyncOS
Onboarding and portal: CES provisioning is driven by Cisco. After signing, the Account Manager triggers tenant creation in the chosen region and sends a welcome letter with the MX hosts, hosted AsyncOS portal credentials and the initial steps. The administrator then configures the SMTP Routes, RAT, Mail Policies, Content Filters, DKIM profiles and quarantine policies, without managing any OS or appliance.
iphmx.com regions: CES operates three geographic zones that determine data residency and MX hosts. North America: US datacenters, MX under mx1.<tenant>.iphmx.com. Europe: EU datacenters (Netherlands and Germany depending on the contract), MX under mx1.<tenant>.eu.iphmx.com. APJ: MX under mx1.<tenant>.apj.iphmx.com or country variants. Each customer is provisioned in a single region by default; multi-region organizations set up several distinct CES tenants. Pointing MX records to a region that does not match the tenant allocation triggers silent rejections on Cisco's side.
Shared vs dedicated tenant: the shared tenant is the standard entry level (several customers on the same logical infrastructure, isolation by configuration). The dedicated tenant (sometimes called Premier or Dedicated Instance) provides dedicated infrastructure, mandatory for some regulated verticals (finance, healthcare, government). Shared generally suffices for a mid-market project.
SLA: Cisco typically contracts 99.999% availability on CES, with outage credits capped as a percentage of the monthly bill. The SLA covers the Cisco platform, not upstream issues (misconfigured DNS, target email server) or downstream (deliverability).
Native integration with M365 and Google Workspace: CES sits as the primary MX in front of the Microsoft 365 or Google Workspace tenant. On the M365 side, the standard architecture consists of pointing MX to iphmx.com, configuring an EOP Inbound Connector that only accepts CES outbound IPs, and restricting Accepted Domains to force all inbound traffic through CES. On the Google Workspace side, the logic is equivalent via Inbound Gateway settings.
Operational limits of CES compared to an appliance: the SaaS model imposes trade-offs. The administrator can no longer access a system shell or raw log files as on an ESA, only the logs exposed in AsyncOS are available. Maintenance windows are set by Cisco (outside of dedicated tenants). Some SIEM integrations historically designed for on-premise appliances need to be reworked in cloud mode (syslog forwarding, Cisco APIs). For most customers, these limits remain acceptable and reduce the operational load.
Cisco Secure Email Gateway (ESA): the on-premise legacy option
ESA is still sold in 2026 but Cisco positions it as a legacy option. C-Series physical or virtual appliances (vESA on VMware, AWS, Azure, GCP), direct heir to Ironport, administered and patched by the customer. Relevant for three precise profiles: strict sovereignty forbidding cloud flows, air-gap infrastructures, or a recently purchased appliance base to amortize before CES migration.
Technically, the ESA receives SMTP traffic on its own public IPs, applies an AsyncOS chain identical to CES, then relays to the actual email server. DNS configuration is entirely in the customer's hands: MX pointing to appliance IPs, SPF built around the outbound IPs, DKIM published manually. Cisco does not provide a managed SPF include in ESA mode, unlike CES. Since ESA and CES share AsyncOS, they are affected by the same vulnerabilities, including the CVE-2025-20393 detailed further below.
Cisco Secure Email Threat Defense (ETD): the modern API complement
Cisco Secure Email Threat Defense (ETD) is Cisco's strategic response to the ICES (Integrated Cloud Email Security) movement initiated by Abnormal Security. ETD does not change MX and runs exclusively through Microsoft Graph API on Microsoft 365 tenants. It is positioned as a complement, not a replacement for CES: its most common use in 2026 is stacking ETD plus CES for Cisco-centric organizations, or ETD plus Microsoft Defender for M365 customers who want a Talos layer without a frontal gateway.
Deployment is much faster than for CES: the administrator authorizes the Cisco application in Azure AD via OAuth, grants read and remediation permissions on M365 mailboxes, and ETD starts analyzing post-delivery messages within minutes. No DNS changes are required, no transport rule, no update of SPF records.
ETD detection rests on three pillars: Talos threat intelligence (signatures, URL reputation, file reputation), behavioral analysis (sender profiling, relationship analysis), and automatic remediation (moving malicious messages to quarantine via Graph API, even after delivery). Cisco claims an AAA rating awarded by SE Labs in the 2025 public evaluation, with detection close to 100% and a particularly low false positive rate. This rating should be contextualized: it compares ETD to other API solutions in a lab scenario, not to every production configuration.
The difference with Abnormal Security is that ETD performs deep email inspection (full content analysis via Talos) whereas Abnormal favors purely behavioral signals (relationship graph, identity baselines). The two approaches are complementary more than competing, and some organizations stack ETD with Abnormal to cover both angles. ETD, however, is not available for Google Workspace or on-premise Exchange in 2026: it is a Microsoft 365 exclusive product, unlike CES which covers the full range.
The AsyncOS engine: shared foundation for CES and ESA
AsyncOS is the proprietary operating system that powers both the CES datacenters and the ESA appliances. It is a pure product of the Ironport heritage: its asynchronous architecture was originally designed to process massive SMTP volumes on the C-Series appliances, and this same engine is what Cisco operates at scale today in its regional CES datacenters. The current version in 2026 (AsyncOS 16.x) keeps that lineage while integrating modern modules.
AsyncOS assembles several engines into an analysis chain executed for each inbound message:
- CASE (Context Adaptive Scanning Engine), the historical Ironport anti-spam engine. It combines signatures, heuristics and contextual analysis to assign a SpamThreshold score to each message.
- AMP (Advanced Malware Protection), Cisco's sandboxing module. Suspicious attachments are detonated in an isolated environment to observe their behavior. AMP shares threat intelligence with Cisco Secure Endpoint, enabling EDR-email correlation for customers running both products.
- URL filtering, which rewrites or blocks inbound URLs based on the Talos database. Unlike Proofpoint URL Defense or Mimecast URL Protect, the Cisco rewrite does not systematically provide a full time-of-click configurable at per-user granularity.
- Content filters, administrator-customizable rules to apply specific actions (quarantine, notification, tag, deletion) based on content, headers, sender, or recipients.
- Outbound DLP (optional module), which scans outbound emails for sensitive data (credit card numbers, PII, tagged confidential documents).
This chain is identical between CES and ESA, which guarantees hybrid customers (primary CES, residual ESA) consistency of policy. Patches and new signatures are deployed in parallel on both platforms, with a unified AsyncOS roadmap, even though in practice CES receives patches before ESA customers since Cisco operates its own instances directly.
Talos integration: 600 billion emails per day
All analysis engines rely on Cisco Talos Intelligence Group, which aggregates telemetry from tens of thousands of Cisco Secure customers and analyzes 600 billion emails per day. Talos maintains one of the largest IP and domain reputation databases in the industry and continuously pushes signatures to CES, ESA and ETD.
Talos integration remains one of Cisco's strongest commercial arguments on this segment. The team size (more than 500 extended contributors), regular zero-day discoveries and collaboration with law enforcement make Talos a real differentiator, even against Proofpoint Nexus or Mimecast MVTP.
Check your DMARC and SPF records
🔧 Full DNS configuration for Cisco Secure Email Cloud Gateway
An error in an MX record, an SPF include pointing to the wrong region, a DKIM key published at the wrong selector: these defects turn a CES deployment into a production incident. Here is the detailed DNS configuration for Cloud Gateway (the main use case in 2026), with a note on the specifics for a self-hosted ESA, and the pitfalls to avoid.
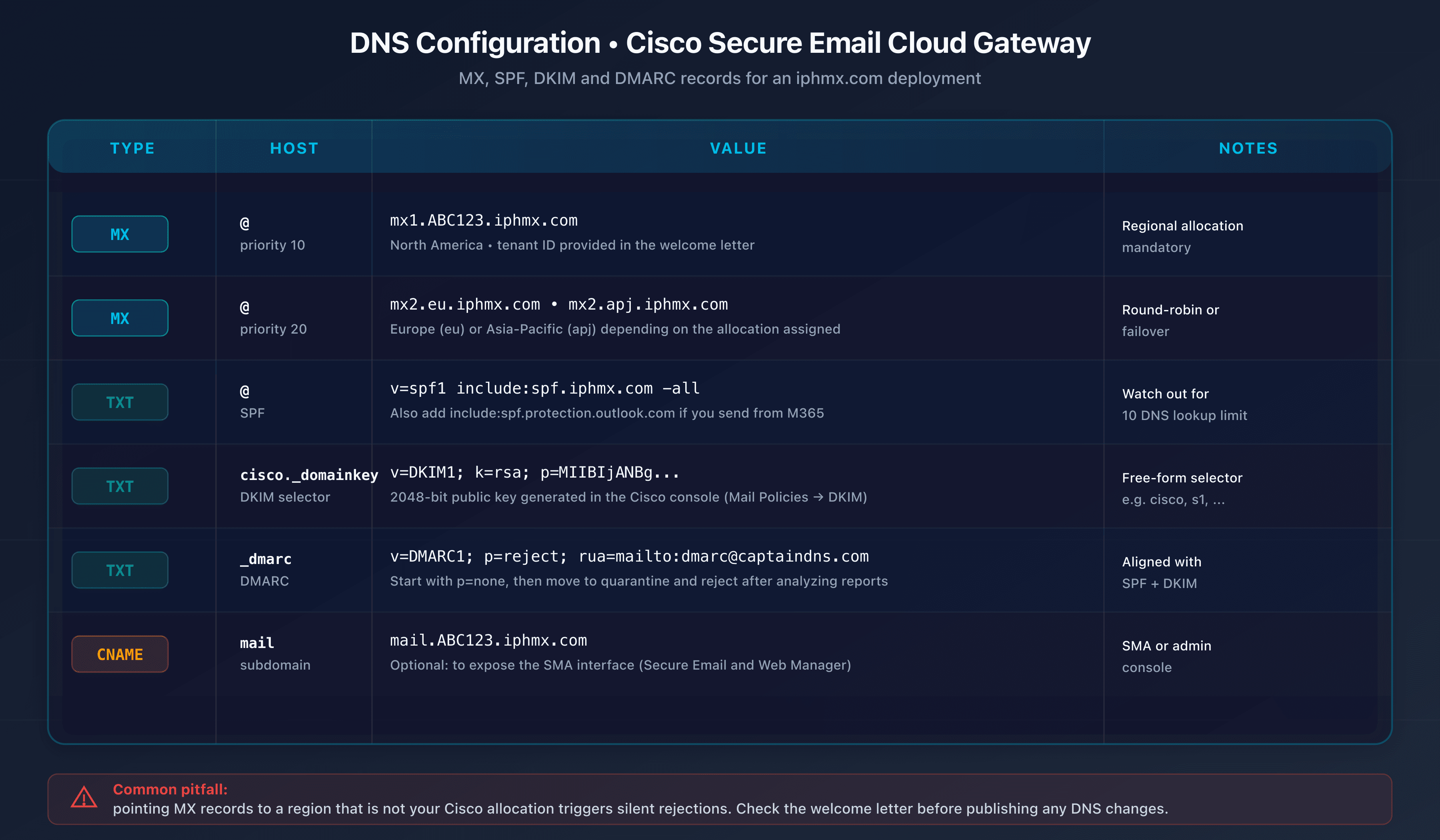
CES MX records: iphmx.com format and regional allocation
For Cisco Secure Email Cloud Gateway, MX records must point to iphmx.com hosts matching exactly the regional allocation assigned in the Cisco welcome letter. The format is predictable:
| Region | Primary MX (example) | Secondary MX (example) |
|---|---|---|
| North America | mx1.ABC123.iphmx.com | mx2.ABC123.iphmx.com |
| Europe | mx1.eu.iphmx.com (variable) | mx2.eu.iphmx.com (variable) |
| Asia-Pacific | mx1.apj.iphmx.com (variable) | mx2.apj.iphmx.com (variable) |
ABC123 represents a unique tenant identifier. Exact hosts are provided by Cisco at provisioning. Both MX records are generally configured with the same priority (10) for round-robin balancing, or slightly different priorities (10 and 20) depending on Cisco recommendations at deployment time.
To check a domain's current MX, use the command:
dig MX captaindns.com +short
The expected result after a Cloud Gateway deployment looks like:
10 mx1.ABC123.iphmx.com.
10 mx2.ABC123.iphmx.com.
Mandatory rules:
- Remove all previous MX records from the domain before cutting over to CES. A leftover MX pointing to Microsoft 365 or Exchange leaves a direct entry path that bypasses CES.
- Use only the hosts matching your regional allocation (NA, EU or APJ). Pointing to the wrong region generates silent rejections on the CES side, since distant datacenters do not recognize your tenant domain.
- Lower the TTL to 300 seconds (5 minutes) several days before cutover to allow a fast rollback in case of an incident.
Self-hosted ESA edge case: for customers still running on-premise ESA appliances, MX records do not point to iphmx.com but to the appliance public IPs (or a DNS FQDN resolving to them). DNS configuration is entirely on the customer: they must expose a coherent reverse DNS on each appliance IP, manage SPF around those same IPs, and publish the DKIM keys themselves. Cisco does not provide a managed SPF include in this mode, unlike CES where spf.iphmx.com is turnkey.
CES SPF configuration: include:spf.iphmx.com
When Cisco Secure Email Cloud Gateway relays your outbound emails, its IP addresses must appear in your SPF record so recipients can validate authentication. Cisco provides a dedicated include:
v=spf1 include:spf.iphmx.com ~all
This include resolves to IP blocks operated by Cisco for outbound relay in your region. For European allocations, Cisco may point to a regional variant like spf.eu.iphmx.com; check the welcome letter for the exact syntax.
Unlike Proofpoint which offers its Hosted SPF Service with RFC 7208 macros to work around the 10-lookup limit, Cisco does not provide an equivalent mechanism of dynamic server-side resolution. Each spf.iphmx.com include typically consumes 2 to 3 internal lookups. For an organization stacking Microsoft 365, Google Workspace, Salesforce, HubSpot and Cisco, the 10-lookup bar becomes a real SPF PermError risk.
Three strategies to avoid a PermError with Cisco:
- Prioritize strictly necessary includes and remove non-critical third-party services
- Use a third-party SPF flattener (Valimail, Scrutinizer, Red Sift) that dynamically flattens authorized IPs while respecting the limit
- Delegate transactional subdomains to a dedicated domain with its own SPF
Check your SPF with the appropriate checker before and after cutover, paying particular attention to the lookup counter.
~all or -all? With a DMARC p=reject policy in place, ~all (softfail) is enough: DMARC dictates the rejection. Without DMARC or with p=none, prefer -all (hardfail) for strict SPF-level protection.
DKIM configuration: 2048-bit AsyncOS signing
Cisco Secure Email can sign outbound emails with DKIM directly via AsyncOS. Configuration takes place in the administration console:
- Create a DKIM signing profile in AsyncOS (Mail Policies > Signing Profiles)
- Set an explicit selector, for example
cisco20260420to identify the rotation - Choose a key size of 2048 bits (recommended size per RFC 8301 and supported by all modern recipients)
- Generate the key pair and copy the TXT record provided by AsyncOS
- Publish the TXT record in DNS at the location
cisco20260420._domainkey.captaindns.com - Enable the signing profile in the corresponding outbound flow policy
To check the DKIM publication:
dig TXT cisco20260420._domainkey.captaindns.com +short
The result must contain the public key in the format v=DKIM1; k=rsa; p=MIGfMA0GCS.... Some DNS providers do not natively support TXT records longer than 255 characters (a 2048-bit public key exceeds that limit). The value then needs to be split into concatenated strings between double quotes, a syntax supported by BIND, PowerDNS and most modern resolvers.
DKIM rotation: an annual rotation is recommended. AsyncOS lets two profiles coexist in parallel during the rotation phase to avoid any interruption. Deploy the new key, wait for full propagation (48 hours minimum), switch the active signature, then remove the old key after a week of stability.
DMARC: inbound verification and outbound publication
Cisco Secure Email acts as an inbound DMARC verifier: for each received message, AsyncOS looks up the sending domain's DMARC record and applies the declared policy (none, quarantine, reject). This function is enabled by default in most modern deployments. You can check AsyncOS logs to see DMARC results per message and adjust actions to your tolerance.
On the sender side, Cisco Secure Email signs your emails via DKIM and aligns Return-Path on your domain, which enables SPF and DKIM alignment for DMARC. However, Cisco does not offer a managed DMARC module comparable to Proofpoint Email Fraud Defense or Mimecast DMARC Analyzer. To drive your progression from p=none to p=quarantine and then p=reject, you will need a third-party tool (Valimail, dmarcian, EasyDMARC, Red Sift) or the CaptainDNS tools to analyze aggregate RUA reports.
Example of an initial DMARC record in monitoring mode:
v=DMARC1; p=none; rua=mailto:dmarc@captaindns.com; ruf=mailto:dmarc-forensic@captaindns.com; fo=1;
The standard progression after a Cisco deployment:
- p=none for 2 to 4 weeks, analyzing reports to identify all legitimate sending sources
- p=quarantine with
pct=10then a progressive ramp to 100%, monitoring false positives - p=reject as the final target policy
TTL and cutover window
Lower the TTLs of MX, SPF and DKIM to 300 seconds (5 minutes) at minimum 72 hours before cutover. This precaution allows a fast rollback if an incident is detected in the first hours. Once cutover is validated and stable for 7 days, raise the TTLs back to their usual value (3600 seconds or more) to reduce load on your DNS servers.
Schedule a maintenance window on the weekend or during a low-traffic period, and coordinate cutover with your support team to actively monitor non-delivery reports (NDR) during the first 48 hours.
🛡️ Cisco ecosystem: SecureX, Cisco XDR and Splunk
CES, ESA and ETD do not operate in isolation in the Cisco Secure ecosystem. Integration with other security products is a strong commercial argument, but it was shaken in 2024 by the SecureX EOL and its replacement by Cisco XDR.
From SecureX (EOL July 2024) to Cisco XDR
Cisco SecureX, the orchestration platform launched in 2020, reached its End of Life on July 31, 2024. It aggregated alerts and telemetry from Email, Firewall, Endpoint and Umbrella in a unified console, with automation playbooks and SOAR APIs. Customers were invited to move to Cisco XDR, the Extended Detection and Response platform launched in 2023, taking over SecureX capabilities with a broader scope (deeper cross-domain detection, ML, third-party source integration) and a distinct commercial structure: three subscription levels (Essentials, Advantage, Premier) on top of Cisco Secure Email licenses.
The CES plus ETD into Cisco XDR integration is the flagship argument for correlating email, endpoint and network. The XDR console shows email alerts, lets you orchestrate cross-product actions (blocking a domain in Email and Umbrella simultaneously) and applies investigation playbooks. It is one of Cisco's real differentiators against Proofpoint or Mimecast when the environment is Cisco-centric. For non-SecureX customers, XDR is additional spend to budget; for legacy customers, it is a mandatory migration with a contract change and reconfiguration.
Splunk: the 28 billion dollar acquisition not yet fully integrated
The Splunk acquisition for 28 billion dollars (March 2024) repositioned Cisco on the SIEM and observability segment. In 2026, the Splunk integration with Cisco Secure Email remains partial: connectors exist to ingest AsyncOS and ETD logs into Splunk Enterprise Security, but the merger of consoles, policies and detection models is still being built. CES logs are usable via connectors, but the experience remains fragmented across XDR, Splunk and the product consoles.
Talos: the shared threat intelligence
One anchor point remains stable: Cisco Talos feeds all Cisco Secure products (Email, Endpoint, Firewall, Umbrella, XDR). This consistency is a real asset for Cisco-centric environments, where a Talos discovery is immediately propagated to all active controls.
🚀 The benefits of Cisco Secure Email
Cisco Secure Email retains seven factual strengths in 2026: Talos threat intelligence (600 billion emails per day), 2025 SE Labs AAA rating on ETD, native Cisco Secure integration (XDR, Firewall, Endpoint), flexibility across CES + ESA + ETD, entry pricing around $1.90 per user per month, SOC 2 and ISO 27001 compliance, and global 24/7 support. Why do 12,160 organizations still use Cisco Secure Email in 2026? Here are the factual arguments that justify the choice, without commercial sugarcoating.
- Top-tier Talos threat intelligence. 600 billion emails analyzed per day, 500+ extended contributors, 185+ industry partnerships. Regular zero-day discoveries (including on competing products like Microsoft Exchange) attest to the research quality. A strong argument for a CISO valuing intelligence flow depth.
- AAA SE Labs rating on ETD in 2025, close to 100% detection with a low false positive rate. Validates the post-delivery API model, to be nuanced as a lab indicator.
- Native integration within the Cisco Secure ecosystem. For an organization already running Secure Firewall, Secure Endpoint and Umbrella, the CES plus ETD plus XDR correlation delivers real operational value. An IoC detected on an endpoint can trigger a simultaneous block in Email and Umbrella.
- Flexible CES plus ESA plus ETD deployment model. Few vendors simultaneously cover SaaS gateway, on-premise and post-delivery API. CES remains the main case; ESA and ETD handle specific cases (sovereignty, M365 API).
- Accessible entry pricing. CES and ESA start around 1.90 dollars per user per month according to UnderDefense. Full bundles (Essentials, Advantage, Premier) between 5 and 7 dollars per user per month, comparable to Mimecast and lower than Proofpoint (median ~87,000 dollars per year per Vendr).
- Compliance and certifications: SOC 2, ISO 27001, FedRAMP Moderate. Data residency configurable per CES region (US, Europe, APAC) with European sovereignty options.
- Large-scale professional support: global network of partner integrators and 24/7 support. Denser coverage than Abnormal or Mimecast in some geographies.
⚠️ Limitations and drawbacks to know
Signals of strategic decline are multiple and factual. This block documents the limits raised by analysts, customers and public figures.
- 2024 and 2025 Gartner Magic Quadrant Email Security exit. The December 16, 2024 MQ does not include Cisco, the 2025 report confirms the absence. Proofpoint mentions it explicitly in its commercial messaging. The most striking signal of the declining trajectory on this segment.
- Marginal market share (0.06 to 0.11%) against Proofpoint (24% Frost Radar), Microsoft Defender and Mimecast (42,000 organizations). The question of R&D investment is legitimate for a prospect with no Cisco footprint.
- Dated AsyncOS admin interface. Feedback on G2, Capterra and TrustRadius points to a dense console inherited from Ironport. Mail Policies, Content Filters, SMTP Routes require specific expertise. The experience shows its age against Mimecast post-2023 or API-native Abnormal.
- Innovation cadence perceived as trailing since the Splunk/XDR pivot. Announcements are rarer than at Proofpoint (Nexus AI, Adaptive Email Security from Tessian) or Mimecast (Attune, Mihra in 2025-2026). Messaging focuses on XDR integration more than on native email innovations.
- Numerous End of Sale and End of Life announcements in 2024-2025. Phishing Defense end of sale on March 13, 2025, Intelligent MultiScan EOL on September 4, 2025, Secure Email Premier EOL on November 4, 2025, Secure Awareness EOL on November 4, 2025. Hot SKU migrations with non-trivial project load.
- Complex portfolio fragmentation: CES, ESA, ETD, plus the Essentials/Advantage/Premier bundles, plus the legacy SKUs in EOL. Dense documentation, complex quotes for partners, a barrier for an SMB without a dedicated architect.
- No equivalent to Hosted SPF RFC 7208. Unlike Proofpoint, Cisco leaves it to the customer to manage the 10-lookup SPF limit. An operational friction point for a multi-ESP organization.
- No managed DMARC module equivalent. Mimecast offers DMARC Analyzer, Proofpoint Email Fraud Defense. Cisco provides no managed equivalent. DMARC steering is left to the customer with third-party tools or CaptainDNS.
🔒 The critical December 2025 zero-day
CVE-2025-20393 is the major Cisco Secure Email security event of 2025. Critical zero-day, active exploitation, presumed state actor: the case illustrates both the attackers' sophistication and the structural vulnerability of internet-exposed quarantine interfaces.
Discovery, nature and exploitation
Cisco was alerted on December 10, 2025 by Talos Research of a critical unauthenticated RCE affecting the AsyncOS Spam Quarantine function. Score CVSS 10.0, the maximum, reflecting ease of exploitation, impact (remote root arbitrary code execution) and the absence of authentication prerequisites. The vulnerability is tracked as CVE-2025-20393, Cisco advisory cisco-sa-sma-attack-N9bf4. No workaround: mitigation relies on the patch and on removing public exposure of the Spam Quarantine interface.
A remote attacker can execute system commands with root privileges on the appliance or instance. Exploitation requires the Spam Quarantine interface to be enabled and exposed on the internet (not the modern default configuration, but common on legacy configurations). A root RCE on an email platform means reading traffic in transit, exfiltrating archives, pivoting to the internal network via management, and persistence via backdoors. A catastrophic scenario for a targeted organization. Both CES and ESA are affected: they share AsyncOS, so the vulnerability reaches both deployment modes, even if CES tenants are mass-patched by Cisco.
UAT-9686 actor and KEV catalog listing
Talos attributed the campaign to the UAT-9686 actor, linked to China with moderate confidence. Active exploitation was observed starting late November 2025, several weeks before public disclosure, on strategic organizations. The observed cycle: automated scanning of exposed Spam Quarantine interfaces, AsyncOS fingerprinting, RCE, initial implant, lateral movement, persistence. IoCs published by Talos: implant hashes, C2 domains, network patterns.
CISA added CVE-2025-20393 to its Known Exploited Vulnerabilities (KEV) catalog with a mitigation deadline of December 24, 2025 for federal agencies. Most cyber insurance policies now require a posture aligned with KEV deadlines, which turns the Cisco advisory into an implicit contractual obligation.
Lessons and durable mitigations
Beyond the immediate patch, CVE-2025-20393 carries several lessons: remove public exposure of quarantine and management interfaces (VPN or reverse proxy with strong authentication), audit AsyncOS versions across the entire infrastructure (unpatched ESA appliances are the highest risk), put behavioral monitoring in place on Cisco Secure Email platforms, integrate Talos IoCs into the SIEM and run retrospective searches over several months, and evaluate the relevance of keeping ESA appliances versus CES, whose patching is continuously handled by Cisco.
🔄 Comparison: CES against Mimecast, Proofpoint, Microsoft Defender and Abnormal
In 2026, CES is the only major player in the segment absent from the 2024-2025 Gartner Magic Quadrant Email Security, facing four official Leaders (Proofpoint, Mimecast, Microsoft Defender, Abnormal). How does Cisco Secure Email Cloud Gateway position itself in 2026 against the competition? This comparison pits CES (the Cisco SaaS, target of a new deployment) against the main alternatives in the gateway and API segment. On-premise ESA is not compared line by line since it no longer actively competes with modern SaaS offerings.
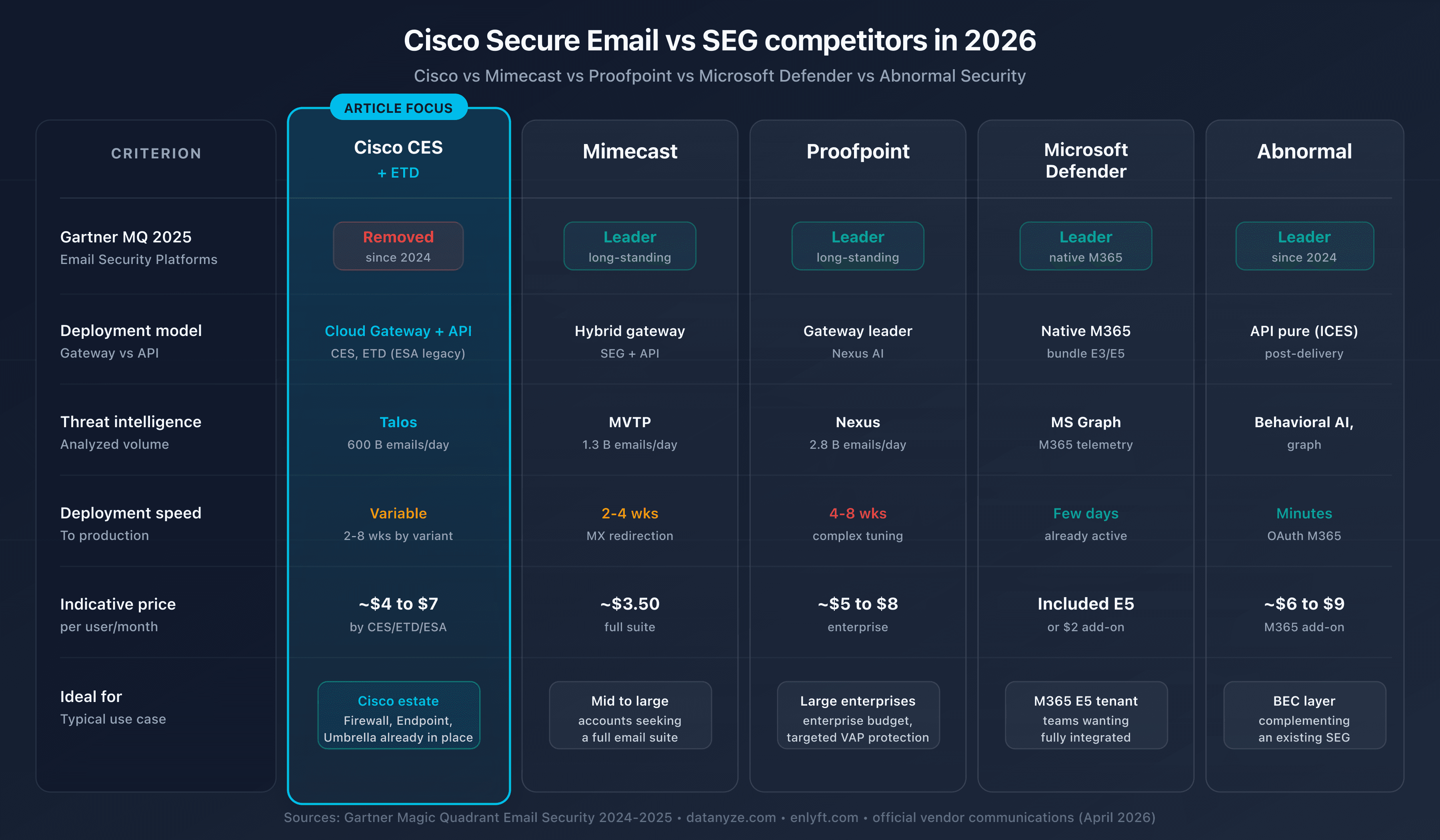
| Criterion | Cisco CES + ETD | Mimecast | Proofpoint | Microsoft Defender O365 | Abnormal Security |
|---|---|---|---|---|---|
| Model | SaaS Gateway (CES) + API (ETD) | Gateway + API | Gateway + API (Adaptive) | Native M365 | API-only |
| Gartner MQ 2024-2025 | Absent | Leader | Leader | Leader | Leader |
| Threat intel | Talos (600B/day) | 24T signals/year, 42k orgs | Nexus (4.5T/year) | Native M365 | Attune 1.0 (1B signals) |
| Email market share | 0.06 to 0.11% | significant | 24% Frost | M365 benchmark | growing |
| Entry price | $1.90/user/month | $3.50 to $8/user/month | ~$87k/year median | under €2/user/month (E5) | $36 to $80/user/year |
| Managed DMARC | No | DMARC Analyzer | Email Fraud Defense | No | Valimail partnership |
| Sandboxing | AMP | Yes | TAP + Predictive | Yes (Safe Attachments) | No |
| Strengths | Cisco ecosystem, Talos | All-in-one, archiving | High-end threat intel, VAP | Native M365 integration | BEC/VEC, fast deployment |
| Weaknesses | Gartner decline, dated UI | Opaque pricing | Post-Thoma Bravo, EchoSpoofing | M365 dependency | Post-delivery, no sandbox |
Mimecast: the all-in-one for mid-market
Mimecast is a natural alternative for mid-market Cisco customers looking for a full SEG with integrated archiving, email continuity and DMARC Analyzer. The Gartner MQ 2024-2025 Leader positioning, the 42,000 customer organizations and functional breadth (TTP suite, CyberGraph, Human Risk Management) make Mimecast a common migration target from Cisco. Pricing ($3.50 to $8 per user per month) is comparable to Cisco but with a wider functional scope.
Proofpoint: the enterprise benchmark
Proofpoint is the high-end alternative for organizations that want the best threat intelligence on the market. Present at 87 of the Fortune 100, ranked #1 in Execution in the Gartner MQ, Proofpoint targets large enterprises in finance, healthcare and government. Hosted SPF Service and Email Fraud Defense are two strong differentiators against Cisco. Premium pricing (median around $87,000 per year) is a high entry ticket but aligned with service quality.
Microsoft Defender O365: the native M365 choice
For a full Microsoft 365 organization, Defender for Office 365 is the simple and cost-effective choice. Native activation in the existing tenant, no MX change, integration with Purview for compliance, and aggressive pricing (under 2 euros per user per month, even included in E5). Historical BEC shortcomings are progressively closing, but for advanced behavioral detection, an Abnormal overlay remains relevant.
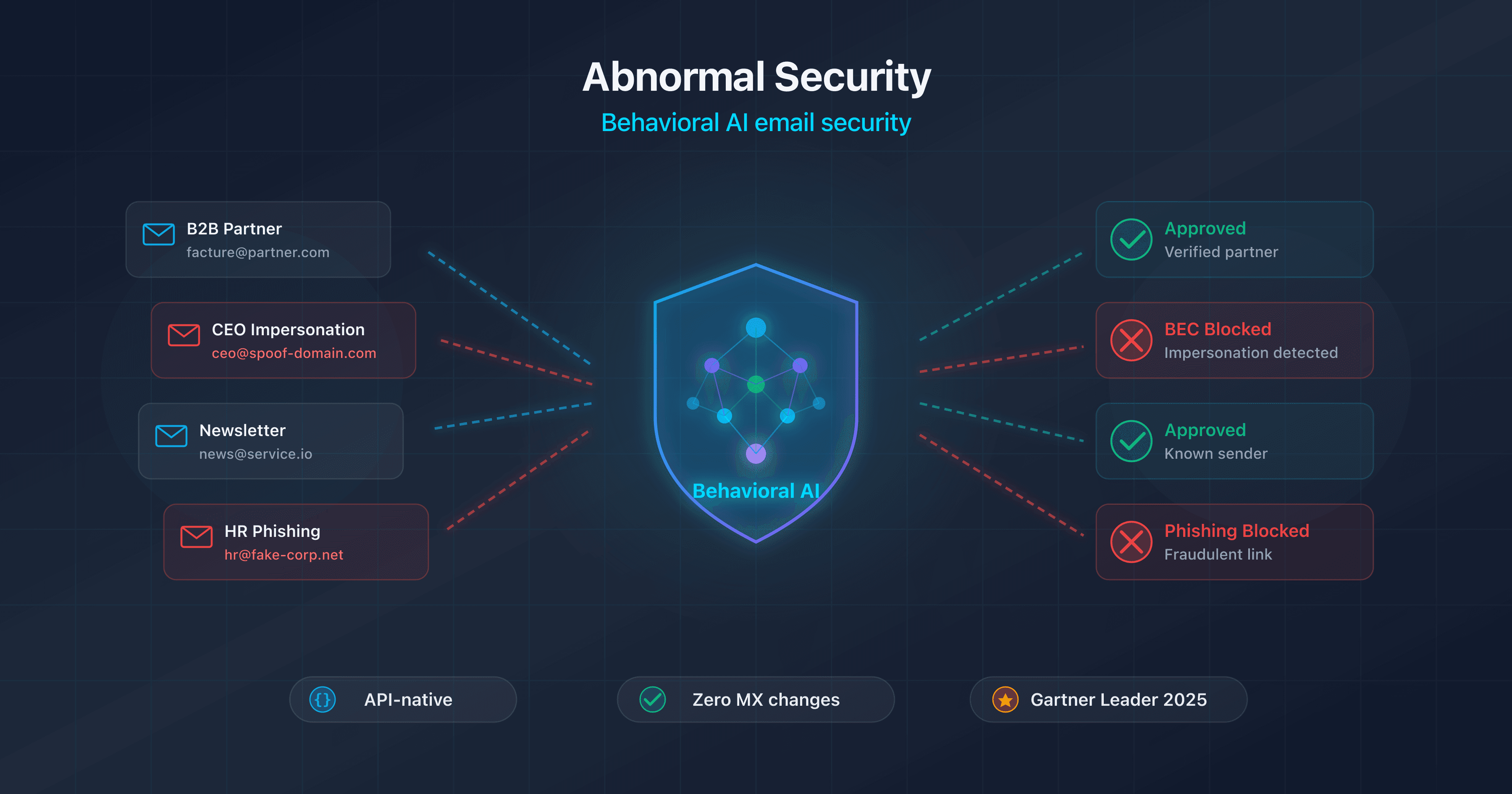
Abnormal Security: the behavioral layer
Abnormal Security is the reference ICES solution for BEC and VEC detection. API deployment in minutes, no MX changes, Attune 1.0 foundation model trained on more than one billion signals, 99% renewal rate. Positioned as a Gartner and Forrester Leader, Abnormal is often stacked on Defender or ETD for reinforced behavioral coverage. The limits (no sandboxing, post-delivery) must be weighed against the organization's threat profile.
Summary: CES stands alone outside Gartner
Among the five historical names of the enterprise email segment, Cisco is the only one absent from the 2024 and 2025 Gartner Magic Quadrant Email Security, whether for CES or ETD. For a Cisco-centric customer with heavy investment in Secure Firewall, Secure Endpoint and Umbrella, the CES plus ETD plus Cisco XDR combination keeps real operational coherence. For a pure M365 customer without Cisco history, the Defender plus Abnormal combination dominates. For the Fortune 500 high end, Proofpoint remains essential.
🎯 When to choose Cisco Secure Email Cloud Gateway?
CES suits Cisco-centric organizations (Secure Firewall, Secure Endpoint, Umbrella) starting a new email deployment or migrating from an ESA, with some tolerance for the strategic risk tied to the 2024-2025 Gartner absence. The right SEG depends on your infrastructure, your budget, and your appetite for the strategic risk tied to a product in Gartner decline. Here are the cases where CES justifies itself first, where ESA remains acceptable despite its legacy status, where ETD comes in as a complement, and those where an alternative will be more relevant.
Cisco Secure Email Cloud Gateway (CES) first if:
- You are starting a new Cisco Secure Email deployment: CES is the option recommended by Cisco, with SaaS onboarding driven through the portal and an operational impact on the customer side limited to DNS and AsyncOS configuration
- Your mid-market or enterprise organization has a significant Cisco footprint (Secure Firewall, Secure Endpoint, Umbrella, Duo) and you want to consolidate on a Cisco-operated SaaS to simplify TCO
- You are migrating to Microsoft 365 from on-premise Exchange and looking for a SEG that covers the transition with per-region configurable data residency (NA, EU, APJ)
- You want to eliminate the operational load of an aging ESA appliance and benefit from continuous patching on the Cisco side, especially after the CVE-2025-20393 episode
ESA (on-premise) only in these specific cases:
- You operate an air-gap or strictly sovereign environment that forbids any outbound email flow to cloud datacenters
- You have recently invested in an appliance fleet (physical or virtual) and need to amortize the expense before CES migration
- Your organization is historically Ironport/ESA without an immediate migration budget, but a 12-24 month CES roadmap should be considered
ETD as a complement, if:
- You are on Microsoft 365 and want a post-delivery API layer in the Cisco ecosystem, with XDR correlation to Secure Endpoint and Secure Firewall
- You are stacking ETD on CES to double detection (gateway plus API) on the most targeted M365 tenants
- You already use Microsoft Defender natively and want to add Talos without deploying a frontal gateway
Cisco Secure Email is not the best choice if:
- You are deploying a new enterprise SEG without existing Cisco: Proofpoint, Mimecast or the Defender plus Abnormal combination offer a clearer product trajectory and stronger Gartner positions
- You are an SMB without a dedicated security team: AsyncOS complexity and portfolio fragmentation are disproportionate to your needs
- Your priority is payload-less BEC and VEC detection: Abnormal Security excels on this segment and ETD remains a challenger on that specific niche
- You are full Microsoft 365 without budget for a third-party layer: Defender O365 is enough for common threats, and cheaper
- You give strong priority to Gartner positioning in your RFPs: the absence of Cisco in the 2024 and 2025 MQ is a deal-breaker signal for some buying committees
🖥️ Cisco Secure Email Cloud Gateway deployment guide
A successful CES deployment relies on a Cisco-driven subscription, a clean onboarding in the portal, correct regional allocation and a controlled MX cutover window. Here are the five key steps of the standard CES journey (from zero to production), followed by a specific sub-section for customers migrating from an existing ESA to CES, and finally the common pitfalls.
Step 1: subscription and region choice
The starting point of a CES project is the commercial discussion with your Cisco Account Manager or integrator partner. The elements to pin down before signing:
- Number of mailboxes to protect (per-user licensing)
- Functional bundle desired (Essentials, Advantage, Premier) based on needed modules (AMP sandboxing, URL filtering, outbound DLP, outbound encryption)
- Hosting region: NA, EU or APJ, a choice that determines filtering datacenters, quarantine residency and
iphmx.comMX hosts - Tenant model: shared (standard) or dedicated (strong regulatory requirements or very large volumes)
- Additional modules: adding ETD in parallel on targeted M365 tenants, XDR integration if you are Cisco-centric
This step conditions everything else: a badly chosen region forces new provisioning and a second DNS cutover, an undersized bundle blocks some Mail Policies later.
Step 2: onboarding in the CES portal
After signing, Cisco provisions the tenant in the chosen region and sends the welcome letter (exact MX hosts, AsyncOS portal credentials, SPF include to publish, administrator account creation instructions). The administrator then configures in the portal, in this order: RAT (accepted domains), SMTP Routes (downstream destination, typically <tenant>.mail.protection.outlook.com for M365), inbound and outbound Mail Policies, 2048-bit DKIM profiles, complementary Content Filters, quarantine policies. All of this takes place before MX cutover, with CES listening but without real traffic, to avoid surprises at cutover.
Step 3: MX cutover and DNS preparation
Document the current DNS state (MX, SPF and its lookup counter, DKIM selectors in use, DMARC policy and RUA/RUF recipients) and prepare post-cutover target values:
- MX pointing to the
iphmx.comhosts from the welcome letter - SPF including
spf.iphmx.comin addition to the includes of your legitimate outbound services (M365, Google Workspace, ESP) - New CES DKIM selector published in parallel with existing selector(s)
Lower TTLs to 300 seconds at least 72 hours before the cutover window to allow a fast rollback. Test DNS resolution of the new MX from multiple resolvers (1.1.1.1, 8.8.8.8, Quad9) before cutover. Check that your authoritative DNS servers properly accept long TXT records for the 2048-bit DKIM key.
On D-day, perform the MX cutover during a low-traffic window (weekend or night) and remove the previous MX records (M365, Exchange, previous SEG) so you do not leave a path bypassing CES.
Step 4: verify outbound DNS authentication
Once CES is in place, outbound emails leave via Cisco relay IPs. Check, on test emails sent to Gmail, Outlook.com and Yahoo Mail, that SPF returns pass on a spf.iphmx.com IP, that DKIM validates with the published CES selector, that DMARC alignment is effective (SPF or DKIM) and that the BIMI logo displays properly if you publish one. Use the CaptainDNS tools to diagnose any authentication defect before deliverability degrades.
Step 5: post-cutover verification and stabilization
Actively monitor for the first 48 hours: unusual NDRs, quarantine spikes (often a sign of a too-strict Mail Policy), user support tickets, CES logs in the AsyncOS portal, aggregate DMARC reports to confirm alignment across all sources. Once stability is confirmed over 7 days, raise the TTLs to their usual value (3600 seconds or more), announce the end of the cutover phase to teams, and integrate CES logs into your SIEM (Splunk, QRadar, Sentinel).
Variant: migration from an on-premise ESA to CES
For a customer already running an ESA and moving to CES (the most frequent scenario in 2026), the sequence differs slightly:
- Export the ESA AsyncOS configuration (Mail Policies, Content Filters, RAT, SMTP Routes, DKIM profiles, allowlist/blocklist) and reconcile it on the CES portal side, cleaning obsolete rules along the way.
- 30 to 60 day cohabitation: keep the ESA active in parallel with CES to cover a rollback, either switching by pilot domain or keeping a temporary backup MX.
- Classic pitfalls: double DKIM signature if an old profile remains active on the ESA, conflicting outbound filters, disjoint logs between the two platforms.
- ESA decommissioning once stability is confirmed: shut down the appliances, reclaim licenses toward the CES contract, archive historical configurations for audit.
This ESA-to-CES trajectory is the one Cisco has recommended since 2020-2021 and represents the majority of active Cisco Secure Email projects today.
Common pitfalls to avoid
- Pointing MX to the wrong CES region. Cisco datacenters silently reject messages destined to a tenant not provisioned with them. Check the welcome letter rigorously before cutover.
- Forgetting to update SPF. Without
include:spf.iphmx.comin your SPF, outbound emails relayed by CES will fail authentication at modern recipients (Gmail, Outlook, Yahoo Mail). - Leaving the Spam Quarantine interface exposed on the internet. You expose yourself to CVE-2025-20393 and any future zero-day on this component. Place the quarantine behind a reverse proxy with strong authentication or over VPN, especially for self-hosted ESA customers.
- Confusing CES and ETD at subscription time. CES redirects MX and filters at the front, ETD does not change MX and works post-delivery on M365. Buying one thinking you get the other is a frequent architecture mistake among prospects.
- Ignoring the SecureX to Cisco XDR migration. SecureX has been EOL since July 2024: if your organization relied on it, plan the XDR switch and budget accordingly.
- Underestimating the 10 SPF lookups. Without a flattening mechanism (Valimail, Scrutinizer) or strict include discipline, the accumulation with Microsoft 365, Google Workspace and a few ESPs quickly blows the limit.
📋 Action plan: keep or migrate Cisco Secure Email in 2026
Facing the decline signals (Gartner absence, critical CVE, cascading EOLs), every Cisco Secure Email customer must ask the keep-or-migrate question. Here is a 10-step action plan to decide without bias.
- Map the active Cisco Email SKUs: exhaustive table with licenses, End of Sale and End of Life. Identify at-risk SKUs over the next 12 months.
- Audit current DNS configuration: SPF lookup count, DKIM selectors, DMARC policy, quality of RUA reports.
- Check sensitive interface exposure: apply the CVE-2025-20393 patch, remove public exposure of the Spam Quarantine, audit management interfaces.
- Evaluate the relevance of keeping: weigh the CES plus ETD plus XDR integration (if Cisco-centric), the value of Talos, and the 3-year TCO against the cost of a migration to Proofpoint, Mimecast or Defender plus Abnormal.
- Shortlist alternatives if migrating: Proofpoint for high-end enterprise, Mimecast for all-in-one mid-market, Defender plus Abnormal for M365-centric environments.
- Plan the DNS cutover: 300-second TTL 72 hours before, target MX/SPF/DKIM values, weekend window with documented rollback.
- Export data before decommissioning: quarantines, logs, historical DMARC reports, AsyncOS configurations.
- Validate the new configuration: SPF/DKIM/DMARC tests toward Gmail, Outlook, Yahoo, Authentication-Results header checks, DMARC alignment.
- Decommission Cisco licenses with 30 to 60 day cohabitation: do not cut immediately, to absorb post-cutover incidents.
- Document the migration and train the teams: detailed lessons learned, IT and security training on the new platform.
Check your DNS configuration now: use the CaptainDNS DKIM checker to validate your Cisco DKIM selectors and your alternatives after migration.
📚 Email gateway guides
This analysis is part of our series on enterprise email security solutions:
- Mimecast Secure Email Gateway: architecture, DNS configuration, comparison and action plan
- Proofpoint Secure Email Gateway: Nexus AI, TAP, 2024 EchoSpoofing and DNS configuration
- Abnormal Security: behavioral AI, API deployment, Attune 1.0
- Cisco Secure Email Gateway (this article): Ironport legacy, 2025 Gartner exit and migration plan
- Cloudflare Email Service: Routing, Email Service, Security (ex-Area 1), and DMARC Management
❓ FAQ
FAQ
What is Cisco Secure Email in 2026?
Cisco Secure Email is Cisco's email security product line, heir to the Ironport product acquired in January 2007 for 830 million dollars. In 2026, it breaks down into three products with a clear strategic hierarchy: Cisco Secure Email Cloud Gateway (CES) is the primary option, SaaS operated by Cisco with MX redirection to iphmx.com per region (NA, EU, APJ), pushed for every new deployment; Cisco Secure Email Gateway (ESA) is the legacy on-premise appliance, now reserved for cases of strict sovereignty, air-gap or an installed base to amortize; Cisco Secure Email Threat Defense (ETD) is a post-delivery API complement for Microsoft 365, often stacked on CES or Microsoft Defender.
What is Cisco Secure Email Cloud Gateway (CES) and how is it deployed?
CES is the primary SaaS offering of Cisco Secure Email in 2026. Deployment follows five steps: subscription with Cisco with the choice of region (NA, EU, APJ) and tenant model (shared or dedicated); onboarding in the hosted AsyncOS portal, with configuration of SMTP Routes, RAT, Mail Policies and DKIM profiles; DNS preparation with 300-second TTLs 72 hours before cutover; MX cutover to the iphmx.com hosts provided in the welcome letter and publishing the spf.iphmx.com include; post-cutover verification of SPF, DKIM and DMARC on test emails. The whole thing typically takes 2 to 6 weeks depending on organization size and the complexity of existing Mail Policies.
What CES regions are available and how do I choose?
CES operates three major regions in 2026. North America (NA): US datacenters, MX under mx1.<tenant>.iphmx.com. Europe (EU): EU datacenters (mainly Netherlands and Germany), MX under mx1.<tenant>.eu.iphmx.com, relevant for organizations subject to GDPR with European residency requirements. Asia-Pacific-Japan (APJ): regional datacenters, MX under mx1.<tenant>.apj.iphmx.com. Each customer is provisioned in a single region by default, which determines data residency and MX hosts. For a multi-region organization, several distinct CES tenants can be set up. The choice is made based on primary mailbox location, sovereignty requirements and user proximity for SMTP latency.
What is the difference between Cisco Secure Email Cloud Gateway (CES) and Cisco Secure Email Threat Defense (ETD)?
CES works in gateway mode: it redirects the domain's MX to iphmx.com to filter 100% of inbound traffic before delivery, with SMTP Routes toward the target email server (M365, Google Workspace or Exchange). ETD works in API mode via Microsoft Graph on Microsoft 365: no MX changes, post-delivery analysis with automatic remediation within minutes. CES blocks payload threats (malicious attachments, booby-trapped links) upstream thanks to the AMP sandbox and URL filtering, ETD detects behavioral anomalies and BEC after delivery on an M365 tenant. Both can coexist for reinforced protection, ETD complementing CES on behavioral threats that would have slipped past the pre-delivery filter.
Is Cisco still in the Gartner Magic Quadrant Email Security?
No. Cisco is absent from the Gartner Magic Quadrant Email Security Platforms published December 16, 2024, and still absent from the 2025 report. Proofpoint explicitly mentions this exit in its commercial communications. For Gartner, absence from the MQ generally signals a strategic vision judged weaker or an execution capability insufficient to rank among the priority players. The Leaders of the 2024-2025 MQ are Proofpoint, Mimecast, Microsoft, Abnormal and KnowBe4.
How much does Cisco Secure Email cost?
Cisco Secure Email pricing starts around 1.90 dollars per user per month for entry-level offerings according to UnderDefense. Full bundles (Essentials, Advantage, Premier) sit between 5 and 7 dollars per user per month. Cisco does not publish an official price list: quotes are negotiated through an integrator partner or Cisco Account Manager. For a 1,000-user organization on a full bundle, expect between 60,000 and 84,000 dollars per year in licenses, excluding Cisco XDR which is added if you want cross-product correlation.
Does Cisco Secure Email work with Microsoft 365?
Yes. The three products support Microsoft 365. CES redirects MX to iphmx.com and relays filtered messages to your M365 tenant via an SMTP Route pointing to <tenant>.mail.protection.outlook.com, with an EOP Inbound Connector that locks acceptance to CES relay IPs. ESA can be configured the same way on-premise, but the operational load is entirely on the customer. ETD connects exclusively via Microsoft Graph API to your M365 tenant without DNS changes. For Google Workspace, CES and ESA are compatible via Inbound Gateway settings, but ETD does not support Google Workspace in 2026: it is a Microsoft 365 only product.
How do I migrate from an Ironport ESA to Cisco Secure Email Cloud Gateway (CES)?
Migration from an ESA to CES is the trajectory recommended by Cisco since 2020-2021 and follows five steps. First, request CES provisioning from your Cisco Account Manager with region choice (NA, EU, APJ) and receive the welcome letter with the exact iphmx.com hosts. Then, export the ESA AsyncOS configuration (Mail Policies, Content Filters, RAT, SMTP Routes, DKIM profiles) and reconcile it on the CES portal, cleaning obsolete rules along the way. Then lower DNS TTLs to 300 seconds, prepare the new iphmx.com MX records and the spf.iphmx.com SPF include. Cut the MX during a maintenance window and keep the ESA in cohabitation for 30 to 60 days to cover a potential rollback. Stay alert to classic pitfalls: double DKIM signature if a profile remains active on the ESA, conflicting outbound filters, disjoint logs during cohabitation. Decommission the ESA once stability is confirmed.
How do I migrate from Cisco to Proofpoint, Mimecast or Microsoft Defender?
Migration from Cisco to an alternative follows the same DNS framework as any SEG switch. Prepare the target configuration (new operator's MX, SPF include, DKIM selectors, DMARC policy), lower TTLs to 300 seconds 72 hours in advance, cut MX during a low-traffic window, monitor actively for 48 hours. The difference by target: toward Proofpoint, benefit from managed Hosted SPF Service and Email Fraud Defense; toward Mimecast, leverage DMARC Analyzer and 99-year archiving; toward Defender plus Abnormal, enable Defender natively then authorize Abnormal via OAuth on M365. Plan a 30 to 60 day cohabitation before decommissioning Cisco licenses.
What is CVE-2025-20393 and should I worry about it?
CVE-2025-20393 is a critical zero-day with a CVSS 10.0 score on the AsyncOS Spam Quarantine function, reported to Cisco on December 10, 2025. It is an unauthenticated RCE allowing a remote attacker to execute commands with root privileges on the appliance. Active exploitation has been observed since late November 2025, attributed by Talos to the China-linked UAT-9686 actor. CISA added the CVE to the KEV catalog with a mitigation deadline of December 24, 2025. Must-do: apply the Cisco patch, remove public exposure of the Spam Quarantine, integrate Talos IoCs into your SIEM, and run a retrospective search over several months to identify potential compromises.
What happens to Cisco SecureX after its 2024 end of life?
SecureX reached its End of Life on July 31, 2024. Cisco replaces it with Cisco XDR, a broader Extended Detection and Response platform, but one that is paid with three subscription levels (Essentials, Advantage, Premier). The SecureX to XDR migration is not automatic: configurations can be ported with Cisco migration tools, but historical data is not transferred. For Cisco Secure Email customers, the ETD to XDR integration lets you correlate email alerts with Secure Endpoint and Secure Firewall. A specific XDR budget must be provisioned on top of existing Email licenses.
Is Cisco Secure Email GDPR-compliant?
Yes. Cisco Secure Email supports the usual certifications (SOC 2, ISO 27001, FedRAMP Moderate for US federal agencies) and offers per-region data residency options. Cloud Gateway has European datacenters for EU residency, and European sovereignty options exist for customers subject to strict regulatory constraints. For GDPR compliance, verify precisely with your Cisco Account Manager the storage location of quarantines, logs and archives. Organizations in finance, healthcare and public sector must validate these points contractually.
📖 Glossary
-
CES (Cisco Secure Email Cloud Gateway, formerly Cloud Email Security): Cisco Secure Email's primary SaaS offering in 2026. Operated in Cisco datacenters by region (NA, EU, APJ), with MX redirection to
iphmx.com. This is the default option for every new deployment and the backbone of this article. -
ESA (Email Security Appliance, now Cisco Secure Email Gateway): legacy on-premise option, physical or virtual appliance, heir to the Ironport C-Series. Relevant only for cases of strict sovereignty, air-gap or an installed base to amortize. Cisco steers new customers toward CES.
-
ETD (Email Threat Defense): post-delivery API complement from Cisco on Microsoft 365, via Microsoft Graph API. Works without MX changes and relies on Talos threat intelligence. Often stacked on CES or on Microsoft Defender.
-
Ironport: company founded in 2000 in San Bruno (California), a pioneer of anti-spam appliances. Acquired by Cisco on January 4, 2007 for 830 million dollars. The brand was progressively retired through the November 26, 2012 pricelist switch. Its legacy remains visible in the
iphmx.comdomain name (Ironport Hosted MX) used by CES. -
AsyncOS: proprietary operating system inherited from Ironport, shared by CES (operated by Cisco in its datacenters) and ESA appliances (run by the customer). Asynchronous architecture designed to process massive SMTP volumes.
-
Talos Intelligence Group: Cisco's threat intelligence organization, more than 500 extended contributors. Analyzes 600 billion emails per day and feeds all Cisco Secure products.
-
SecureX: Cisco's security orchestration platform launched in 2020, End of Life on July 31, 2024. Replaced by Cisco XDR.
-
Cisco XDR: Extended Detection and Response platform launched in 2023, replacing SecureX. Three subscription levels (Essentials, Advantage, Premier) with additional cost on top of Cisco Secure Email licenses.
-
CASE (Context Adaptive Scanning Engine): historical Ironport anti-spam engine, integrated into AsyncOS. Combines signatures, heuristics and contextual analysis.
-
AMP (Advanced Malware Protection): Cisco sandboxing module, shares threat intelligence with Cisco Secure Endpoint for EDR-email correlation.
-
spf.iphmx.com: standard Cisco Secure Email Cloud Gateway SPF include. Resolves to IP blocks operated by Cisco for outbound relay. Regional variants possible depending on allocation (
spf.eu.iphmx.com). -
UAT-9686: threat actor identified by Cisco Talos as the origin of the active exploitation campaign for CVE-2025-20393. Moderate-confidence attribution to China.